Da die Hexenzeit immer näher rückt, möchte ich mit einem Auszug aus einem zeitlosen Technik-Klassiker beginnen, dem Gedicht mit dem Titel "The Ramen". Ich weiß nicht, von wem es stammt, aber Hut ab vor demjenigen:
Einst war ich arbeitsmüde und auf der Suche, öde und trübe,
Suche nach vergessenen Dateien, die in unserem Datenspeicher verloren gegangen sind -
Ich saß da, nicht freiwillig, kämpfte gegen den Schlaf an und verlor leider,
Ich habe mir überlegt, es mit einem Nickerchen zu versuchen - einem Nickerchen auf dem Boden meines Büros.
"Keine schlechte Idee", brummte ich, "auf dem Boden meines Büros zu dösen -
Ich halte das nicht mehr aus."
Daher wird er Ihnen zur Genehmigung vorgelegt: Ein einsamer Systemadministrator in einem Rechenzentrum in einer dunklen und stürmischen Nacht. Während die Stunden mit seiner angeschlagenen Psyche Krieg führen, schwingt er eine der gefährlichsten Waffen, die die Geschäftswelt kennt: System Center Configuration Manager. SCCM ist das moderne Excalibur der IT-Welt, und in den richtigen Händen ist es extrem mächtig. Es wird jedoch mit einer gewissen Bestürzung festgestellt, dass diese moderne Waffe ihrem Besitzer gegenüber nicht so diskriminierend ist wie das Schwert der Sage. Viele Administratoren haben im Laufe der Zeit mit einem simplen Tastendruck oder Mausklick Chaos in Unternehmen angerichtet. Lassen Sie uns gemeinsam eine Weile an diesem kalten, regennassen Abgrund der Finsternis entlanggehen und sehen, welche Schrecken einige unserer Vorgänger angerichtet haben und wie wir ihr Schicksal vermeiden können.
In SCCM 2007 werden sie Anzeigen genannt. In SCCM 2012 werden sie Deployments genannt. Wie auch immer sie genannt werden, sie sind eines der wertvollsten Juwelen von Configuration Manager, da sie es uns Administratoren ermöglichen, software und Updates an Sammlungen unserer Wahl zu verteilen, aber was passiert, wenn wir.....schlecht wählen? Dies ist die erste gequälte Seele eines Systemadministrators:
Derjenige, der für die Kollektion "All Systems" geworben hat:
Es gibt Zeiten, in denen Sie etwas an alle Systeme senden möchten, aber diese Zeiten sind eher selten. Microsoft empfiehlt, niemals Werbung für diese Sammlung zu machen. Die bevorzugte Lösung ist die Erstellung einer geeigneten Sammlung, z. B. "Alle Desktops" oder "Alle Windows 7-Rechner" (Sie haben doch Windows 7 installiert, oder? Sie haben nur noch so viel Zeit). Hier sind einige einfache Schritte für den Anfang:
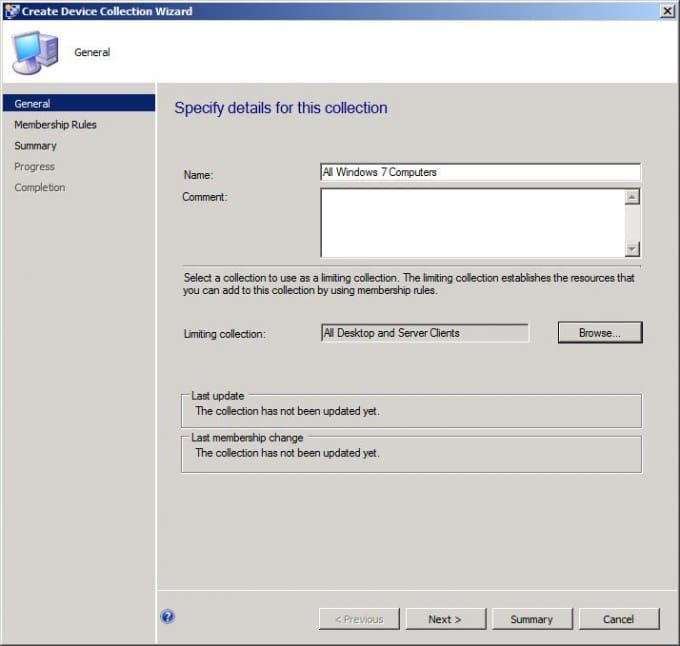
In SCCM 2012 klicken Sie unter Assets and Compliance mit der rechten Maustaste auf Device Collections und wählen Create Device Collection. Geben Sie die allgemeinen Informationen ein, aber hüten Sie sich davor, die Sammlung einzuschränken! Wenn Sie eine Standardsammlung einrichten, ist jede Sicherheit, die Sie dieser Sammlung gewähren, so gut wie null und nichtig. Wenn Sie eine einschränkende Sammlung auf eine Standardsammlung setzen, hat jeder, der die Berechtigung für die erstellte Sammlung hat, Zugriff auf alle Sammlungen. Lesen Sie sich die letzte Aussage noch einmal durch und klicken Sie dann auf Weiter.
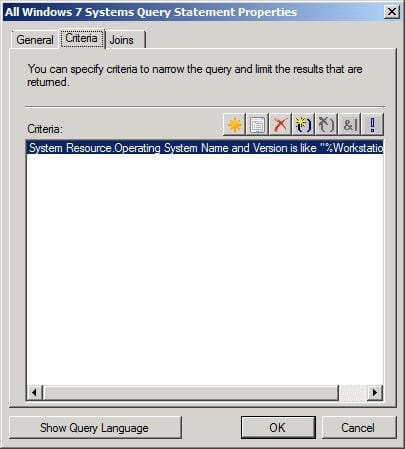
Klicken Sie auf Regel hinzufügen und wählen Sie Abfrageregel (verwenden Sie immer Abfrageregeln als beste Praxis). Geben Sie der Abfrage einen Namen und klicken Sie auf Abfrageanweisung bearbeiten. Klicken Sie auf der Registerkarte Kriterien auf den Stern und dann auf Auswählen, um die Systemressource mit dem Attribut Name und Version des Betriebssystems auszuwählen. Als Operator sollte "ist wie" gewählt werden und als Wert %Workstation 6%. Klicken Sie dann zweimal auf OK und setzen Sie ein Häkchen bei Inkrementelle Updates für diese Sammlung verwenden zweimal auf Weiter und Schließen.
Die nächste Station auf unserer Tour der Verdammten zeigt uns, dass der Weg zur Hölle wirklich mit guten Absichten gepflastert ist. Diese gequälte Seele versuchte, seinen Mitstreitern unter den Systemadministratoren zu helfen, indem sie ihnen uneingeschränkten Zugang zu SCCM gewährte, und teilte am Ende das Schicksal von Julius Cäsar:
Er, der denen, die es nicht verdienen, ungehinderten Zugang gewährt hat:
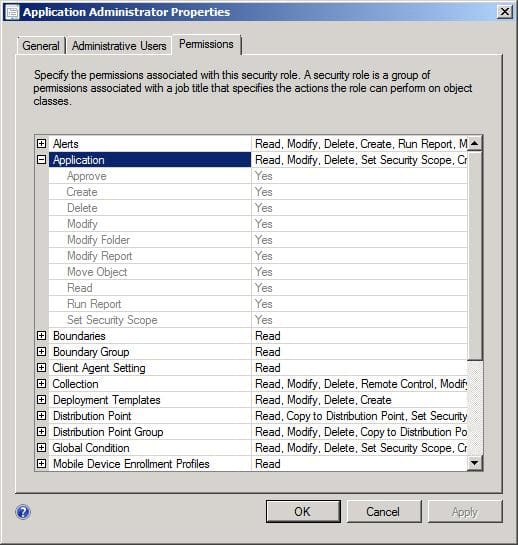
Die wohl leistungsfähigste Funktion von SCCM 2012 ist die rollenbasierte Sicherheit. Damit können SCCM-Administratoren anderen Personen nur Zugriff auf die Objekte gewähren, die sie benötigen. Merken Sie sich meine Worte, dass ganze Bücher über dieses Thema geschrieben werden, damit niemand versehentlich eine Maschine in der falschen Sammlung reimportiert. Indem Sie eine neue Sicherheitsrolle erstellen und die Sicherheitsbereiche richtig konfigurieren, können Sie den Dolch abwehren, der Ihnen in den Rücken fällt.
Unsere nächste Seele hatte ebenfalls gute Absichten, hat aber durch ihre Dummheit ganze Unternehmen in die Knie gezwungen und die falsche Aufmerksamkeit der Führungskräfte auf sich gezogen. Kein Dämon hat den gleichen Zorn wie ein Vizepräsident, wenn er einer Führungskraft auf C-Ebene erklärt, warum das gesamte Unternehmen am Boden liegt und Produktionsmittel verloren gehen. Wir nennen diese verlorene Seele:
Derjenige, der während der Geschäftszeiten große Dateien über das WAN verteilt hat:
Dies war besonders in SCCM 2007 ein Problem, als es keine Drosselung gab und Ihr Mitarbeiter für die Betriebssystembereitstellung beschloss, die neue WIM-Datei um 9:00 Uhr morgens an ALLE Verteilungspunkte zu senden. In jenen dunklen Tagen konnten Sie die Drosselung nur durch die Erstellung einer sekundären Site erreichen. In SCCM 2012 haben wir jetzt nicht nur die Möglichkeit, die Bandbreitendrosselung auf der Ebene der Verteilungspunkte festzulegen, sondern auch auf der Client-Ebene mit BITS:
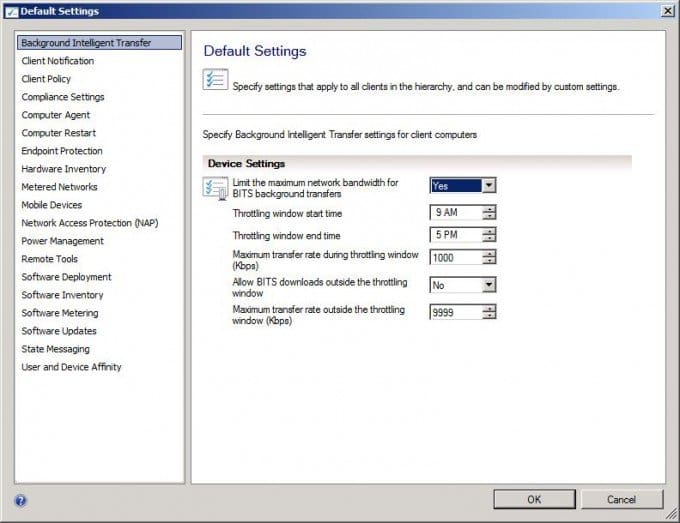
Gehen Sie in der SCCM 2012-Konsole zu Administration und klicken Sie auf Client Settings. Klicken Sie mit der rechten Maustaste auf Standard-Clienteinstellungen (oder die von Ihnen bevorzugte Richtlinie) und wählen Sie Eigenschaften. Intelligente Hintergrundübertragung sollte bereits ausgewählt sein, und im rechten Bereich können Sie die Bandbreiteneinstellungen aktivieren und Optionen auswählen, die für Ihr Unternehmen geeignet sind.
Ich denke, wir sollten unseren kleinen Danse Macabre hier beenden, denn es wird spät und der Mond ist voll. Obwohl wir in dieser Nacht nur drei gequälte Seelen besucht haben, seid versichert, dass es in unseren anderen Ringen noch mehr gibt. Wir haben sogar noch ein paar Plätze frei, falls Sie auf der falschen Seite des Abgrunds landen sollten, aber ich bin sicher, dass alle Ihre Systeme vollkommen sicher sind und Sie als SCCM-Administrator alle Best Practices befolgen. Achten Sie nicht auf das Wimmern und Stöhnen, das Sie im Hintergrund hören. Das sind keine Zombies, sondern nur arbeitslose SCCM-Administratoren, die die Warnungen nicht beachtet haben.