Der Digital Trust Digest bietet einen Überblick über die wichtigsten Nachrichten der Woche im Bereich Cybersicherheit. Hier ist, was Sie diese Woche wissen müssen.

Digitales Vertrauen hat bei Unternehmen in Asien/Pazifik hohe Priorität
Ein neuer Bericht von IDC zeigt, dass die Bedeutung von digitalem Vertrauen zunimmt, ebenso wie das Vertrauen der Kunden in Cybersicherheit, Datenschutz und verantwortungsvolle KI.
Christian Fam, Research Manager für IDC's Asia/Pacific Cybersecurity Services, definiert digitales Vertrauen als das Vertrauen, das Nutzer und Kunden in die Schaffung einer sicheren digitalen Welt haben. Da Cybersecurity-Vorfälle weiterhin große und kleine Unternehmen gleichermaßen plagen, werden Servicepartner eine gute Sicherheitshygiene und Cyber-Resilienz fordern.
Der Bericht befasst sich mit hardware, software, Dienstleistungen und Personen auf dem Sicherheitsmarkt. Um den vollen Umfang der Ergebnisse des Berichts zu sehen, besuchen Sie IDC.
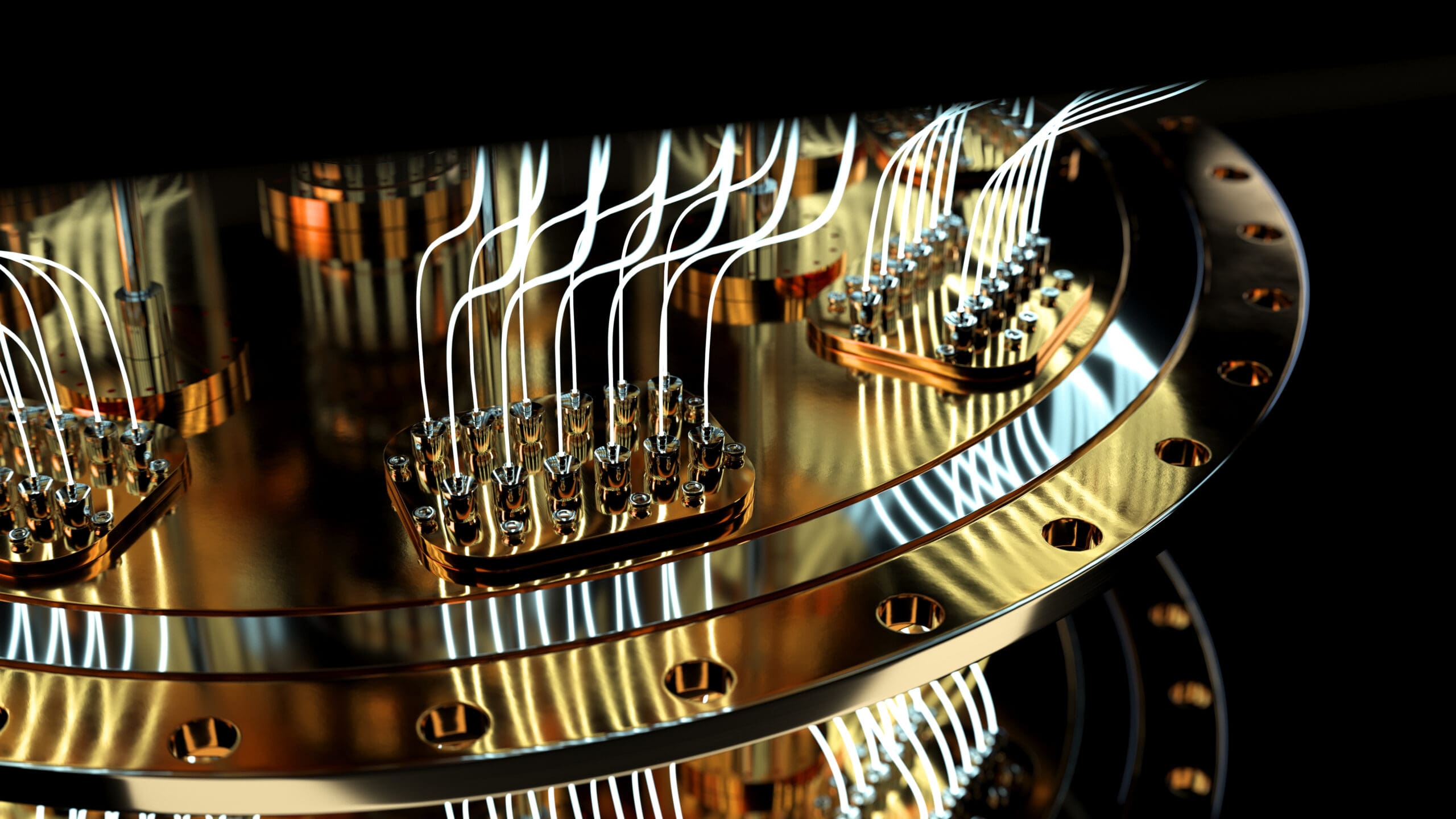
Quantum wird das gesamte Spiel der Datenverschlüsselung verändern
Wenn Sie sich mit der Quantenphysik befasst haben, wissen Sie inzwischen, dass die Quantenphysik die heute gebräuchliche symmetrische und asymmetrische Kryptographie brechen wird - und das ist ein Problem.
Letztes Jahr wählte das NIST vier potenziell quantenresistente Algorithmen aus, die es in seine Post-Quantum-Krypto-Standards aufnehmen will. Drei davon basieren auf strukturierten Gittern, der vierte verwendet Hash-Funktionen. Das NIST wird vier weitere Algorithmen prüfen. Drei davon basieren auf Codes, der vierte auf Isogenese.
Es gibt mehrere Alternativen zu den heute gebräuchlichen kryptografischen Verfahren. Tech Target hat eine gute Übersicht über diese Optionen und die Überlegungen des NIST.

NIST sucht Teilnehmer für ein Projekt zur Sicherheit von Lieferketten und DevOps
Nach den schlagzeilenträchtigen Einbrüchen in Entwicklerumgebungen und der Ausnutzung von Schwachstellen in der Lieferkette software , hat das NIST ein Projekt initiiert, um einen risikobasierten Ansatz auf diese Schwachstellen anzuwenden.
Das Projekt Software Supply Chain and DevOps Security Practices zielt darauf ab, Entwicklungspraktiken, Tools und Frameworks aufzuzeigen, die zur Bewältigung von Cybersicherheitsproblemen beitragen können. Diese Art von Projekt ist ein Beispiel für die Zusammenarbeit zwischen der Regierung und dem privaten Sektor, die in der nationalen Cybersicherheitsstrategie des Weißen Hauses, die Anfang des Jahres vorgestellt wurde, beschrieben wird.
Möchten Sie teilnehmen? Bewerber können bis zum 14. Juni eine Interessenbekundung einreichen. Erfahren Sie mehr über das Projekt unter ExecutiveGov.com.
US-Apothekenriese gehackt, Millionen von Patientendaten offengelegt
Der Apothekendienstleister PharMerica, der mehr als 2 500 Einrichtungen in den USA betreibt, meldete im März eine Datenschutzverletzung. Eine Untersuchung ergab, dass ein ungenannter Dritter einige Tage zuvor auf die Systeme des Unternehmens zugegriffen und die persönlichen Daten von fast sechs Millionen aktuellen und verstorbenen Personen gestohlen hatte.
Die neuartige Ransomware-Gruppe Money Message übernahm die Verantwortung für den Angriff, nachdem die gestohlenen Daten auf ihrer Dark-Web-Leak-Site erschienen waren. Dieser Vorfall ist die bisher größte Datenschutzverletzung im Gesundheitswesen im Jahr 2023, gefolgt von der Regal Medical Group und dem Telemedizin-Startup Cerebral.
Laut dem IBM-Bericht "2022 Cost of a Data Breachhatte die Gesundheitsbranche in den letzten 12 Jahren die höchsten durchschnittlichen Kosten für Datenschutzverletzungen. Einzelheiten zu dem Angriff finden Sie bei TechCrunch.


Wissenswertes über Identitätssicherheit im Jahr 2023
Untersuchungen von Gartner und Verizon zeigen, dass das menschliche Element bei den meisten Sicherheitsverletzungen immer noch eine wichtige Rolle spielt. Sicherheitsverletzungen bei großen Unternehmen wie Chick-Fil-A, T-Mobile, MailChimp und Activision waren direkt auf menschliches Versagen zurückzuführen.
Insbesondere die Passworthygiene ist ein großes Problem, weshalb Unternehmen andere Formen der Authentifizierung nutzen, um die Identität von Benutzern zu überprüfen. Die Integration von KI und maschinellem Lernen in das Identitätszugriffsmanagement kann die Validierungsmaßnahmen über die Anmeldedaten hinaus erweitern, indem das Verhalten bewertet und adaptive Zugriffskontrollrichtlinien ermöglicht werden.
Passwörter könnten bald out sein. RT Insights erforscht, wie Unternehmen die Sicherheit verbessern und Sicherheit und das Benutzererlebnis durch einen mehrschichtigen Ansatz zur Identitätssicherheit.




