A menudo me preguntan cuál es la cantidad y el tipo adecuados de metadatos para certificados. La respuesta es, por supuesto, diferente para cada empresa, y he visto entre 5 y 50 elementos de metadatos para empresas. Sin embargo, esos datos tienen algo en común que puede explicarse fácilmente.
Para asegurarnos de que todos estamos de acuerdo, repasemos qué son los metadatos de certificado y cómo se utilizan en la plataformaKeyfactor .
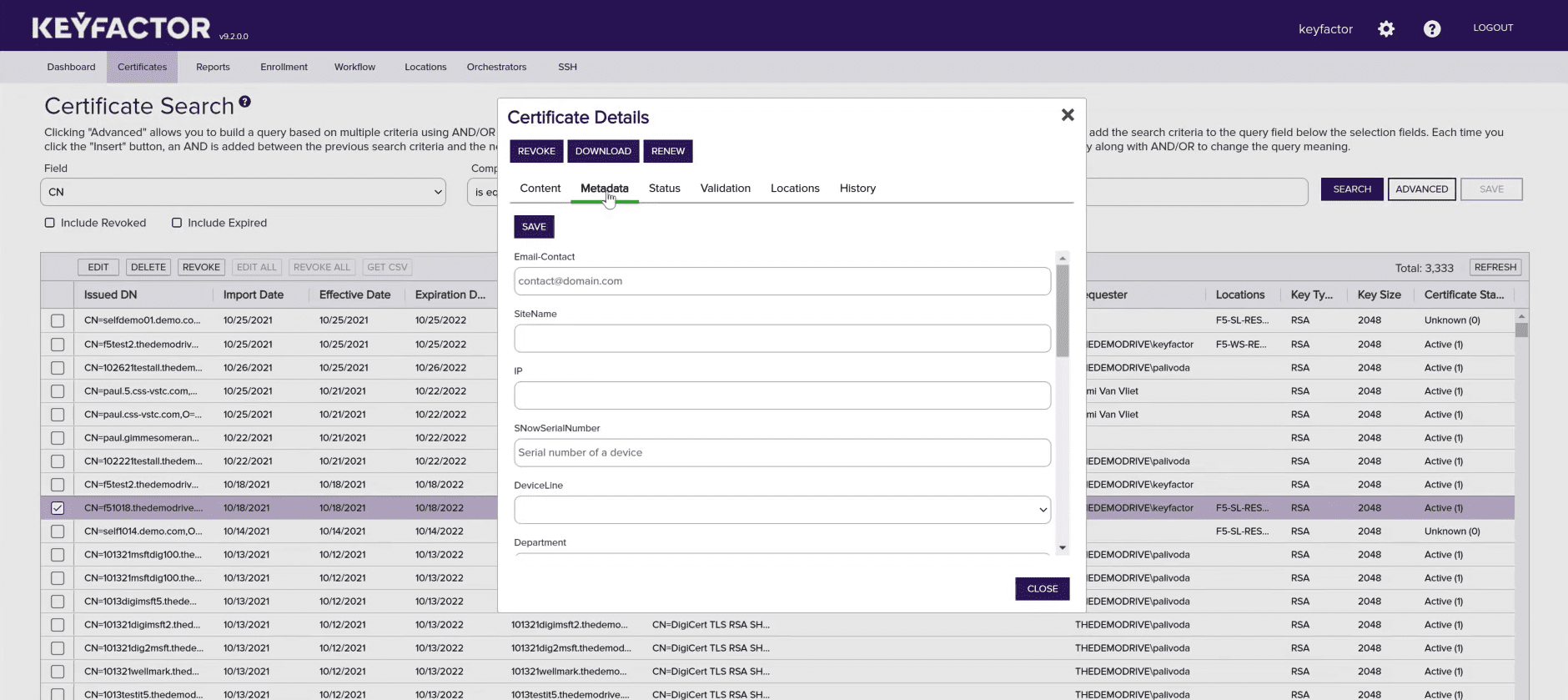
En pocas palabras, los metadatos son una potente función de Keyfactor que permite etiquetar certificados con atributos únicos, más allá de los datos estándar disponibles en formato X.509. Los campos de metadatos pueden incluir cualquier número de detalles importantes, como el propietario del certificado, la unidad de negocio y la información de facturación o contacto. Los campos de metadatos pueden incluir cualquier número de detalles importantes, como el propietario del certificado, la unidad de negocio y la información de facturación o contacto. Estos atributos se utilizan para crear colecciones, que le ayudan a definir y gestionar grupos de certificados a escala de forma muy eficaz.
Cuando me preguntan por los metadatos, suelo señalar tres áreas clave que toda empresa debería tener en cuenta:
- Aspectos que el equipo de PKI debe conocer sobre un certificado
- Cosas que es importante saber sobre un certificado desde el punto de vista operativo
- Cosas que es importante que la empresa sepa sobre un certificado
Aunque a menudo estas tres áreas se solapan, tener unos ámbitos claramente definidos ayudará a garantizar que siempre se capturan los elementos correctos.
Analicemos cada uno de ellos más detenidamente.
Aspectos importantes para el equipo de PKI
Los administradores de PKI suelen tener la mayor carga a la hora de gestionar certificados en un entorno empresarial. El mayor reto es saber a quién pertenece cada certificado (propiedad), para qué aplicación se utiliza (ubicación/uso) y cuándo caduca (validez).
Por supuesto, hacer un seguimiento de cuándo caducan los certificados es un primer paso importante, pero no le ayudará a tomar medidas cuando llegue el momento de renovarlos. El uso de metadatos vincula el certificado al propietario de una aplicación y a su ubicación, lo que simplifica mucho el seguimiento de los servidores, los nombres de DNS y los datos de contacto de cada certificado emitido.
Cosas importantes para las operaciones informáticas
Saber quién es el propietario de la aplicación en un servidor es una cosa, pero es igualmente importante capturar los detalles operativos. Algunos ejemplos incluyen qué servidores protege el certificado, el sistema operativo que se utiliza o cuáles son las distintas DNS o SAN para el certificado. En algunos casos, he visto que esto va tan lejos como capturar para qué rack de servidores, host virtual o clúster Kubernetes se utiliza un certificado en particular.
Cosas importantes para la empresa
Por último, pero no por ello menos importante, hay que recopilar información importante para la empresa. A menudo se trata de datos específicos del funcionamiento de la empresa. Puede tratarse de información como los códigos de facturación o los departamentos, que se utilizan con fines contables. También podría incluir perfiles de riesgo asociados o categorías de cumplimiento para los auditores. Esta categoría en concreto es muy específica de cada cliente.
En definitiva, los metadatos son una función muy potente de la plataforma Keyfactor que todos nuestros clientes utilizan. Sin embargo, gracias a la flexibilidad de los metadatos, cada organización puede decidir qué datos le conviene capturar. Cuando se combinan con la potencia de las colecciones de certificados, los metadatos pueden ofrecer una perspectiva y una visión únicas del uso de los certificados en una organización y aumentar la capacidad de los administradores para convertirse en ninjas de la gestión del ciclo de vida de los certificados.
Estos son algunos de los campos de metadatos más comunes:
- Correo electrónico del propietario del certificado
- Correo electrónico de distribución del equipo del propietario del certificado
- Producción (T/F)
- Nombre de la aplicación
- Número de billete/ID de referencia
Vea el poder de los metadatos en acción
Visite ahora mismo el Centro de demostraciones de Keyfactor para ver cómo puede aprovechar el descubrimiento de certificados, los metadatos y la automatización para gestionar eficazmente los certificados a escala y eliminar el tiempo de inactividad causado por interrupciones inesperadas.