Le Digital Trust Digest est une synthèse de l'actualité de la semaine en matière de cybersécurité. Voici ce qu'il faut savoir cette semaine.

L'adoption de l'informatique dématérialisée entraîne une augmentation des menaces pesant sur la chaîne d'approvisionnement software
La pandémie a entraîné une transformation numérique radicale, intégrant davantage d'opérations commerciales à l'écosystème informatique. Désormais, tout ce qui touche au code dans le cycle de développement software constitue un point de défaillance potentiel.
Des événements tels que SolarWinds montrent à quel point la chaîne d'approvisionnement software peut être vulnérable. Les organisations de la région Asie-Pacifique (APAC) prennent des mesures pour atténuer la compromission de cette chaîne d'approvisionnement, à la fois par la législation et par des méthodes de développement sécurisées dès la conception ( software ).
Pour connaître les leçons que votre organisation peut tirer pour protéger votre chaîne d'approvisionnement software , rendez-vous sur ComputerWeekly.
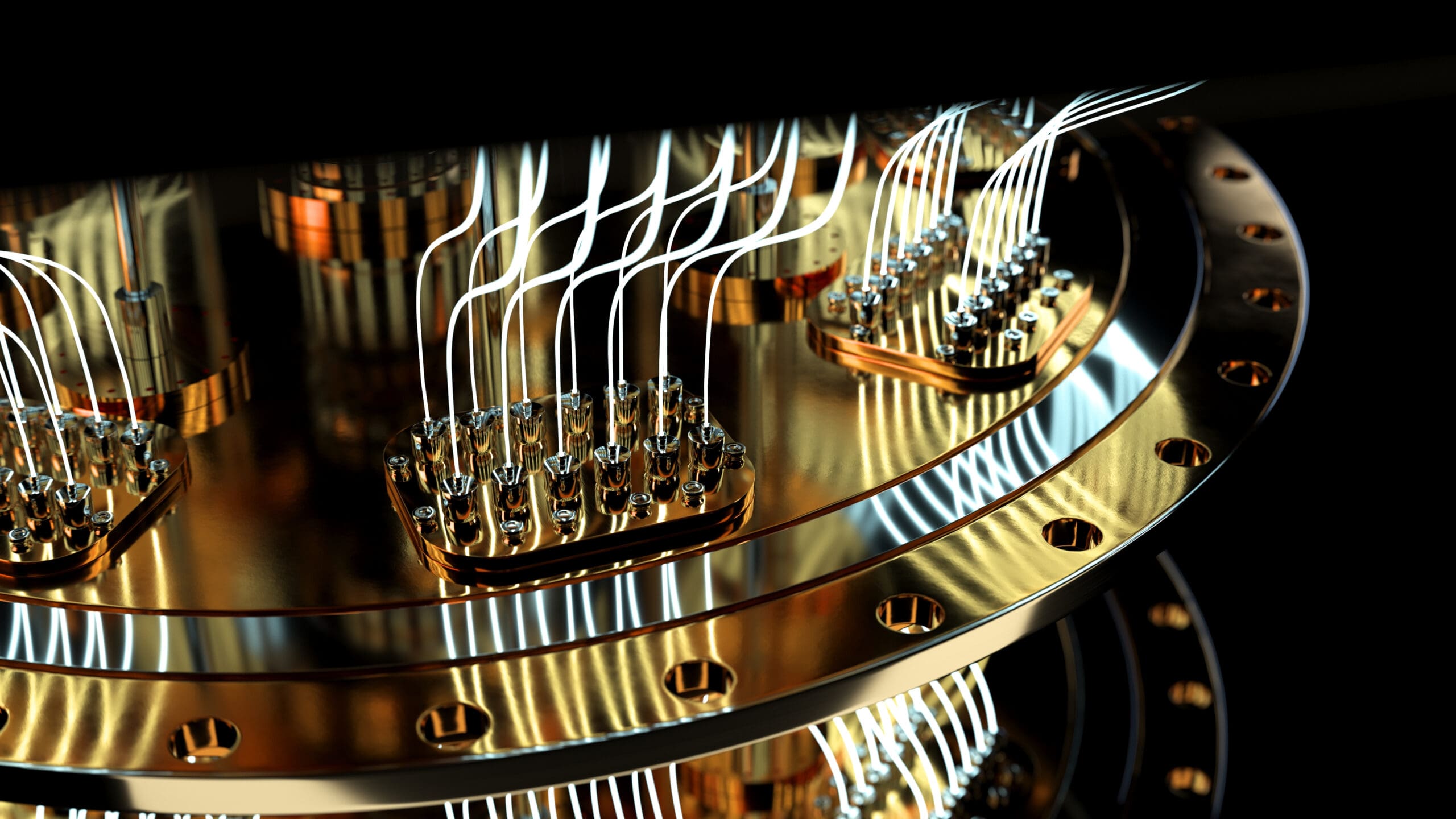
Quantum se rapproche. Serez-vous prêt ?
Les ordinateurs quantiques pourraient être à l'origine de la prochaine grande ère de transformation, mais la facilité avec laquelle ils peuvent briser les modes courants de cryptographie pose un problème de sécurité énorme - et mondial.
Relever les défis de la technologie quantique nécessitera un effort conjoint de la part des gouvernements, des secteurs public et privé. Alors que les gouvernements proposent des lois visant à normaliser et à moderniser nos systèmes critiques, les entreprises feraient bien de définir leurs propres plans pour la transition quantique.
Le Forum économique mondial propose trois approches de cette transition que les organisations peuvent commencer à explorer dès maintenant. Consultez l'article complet pour déterminer celle qui convient à votre organisation.

Le gouvernement néerlandais passe à la nouvelle norme PKI
Le Standardization Forum des Pays-Bas, un organisme de recherche et de conseil au service du secteur public pour l'utilisation de normes ouvertes, a annoncé que tous les appareils de communication (TIC) gérés par le gouvernement néerlandais doivent utiliser la norme RPKI. appareils de communication (TIC) gérés par le gouvernement néerlandais devront utiliser la norme RPKI d'ici 2024.
Les réseaux qui mettent en œuvre la RPKI peuvent être sûrs que le trafic internet est acheminé uniquement par des voies autorisées, ce qui élimine les risques d'attaques de type "man-in-the-middle" ou d'autres attaques de détournement et d'interception de données.
Alors que l'adoption de RPKI est élevée aux Pays-Bas, elle est plus lente dans d'autres pays. Bleeping Computer vous montre comment cela se passe.
Pourquoi les systèmes IAM sont cruciaux pour sécuriser les architectures multi-cloud.
Les écosystèmes en nuage deviennent de plus en plus complexes, et chaque nouvelle connexion élargit la surface d'attaque. La protection des données et la gestion des risques dans l'informatique dématérialisée nécessitent une coordination entre plusieurs plateformes, dont aucune n'est identique à l'autre.
L'identité peut contribuer à atténuer les risques en recentrant la sécurité sur le risque par rapport à la sensibilité, plutôt que sur le réseau par rapport à l'informatique en nuage. Les stratégies IAM peuvent permettre la centralisation et la surveillance des systèmes multi-cloud, ainsi qu'une meilleure adaptation des autorisations d'accès.
Les capacités d'enregistrement automatique des systèmes IAM deviendront des enjeux de taille à l'avenir, car de plus en plus de législations exigent l'audibilité des systèmes. ComputerWeekly peut vous montrer comment comment intégrer l'IAM dans votre propre stratégie de sécurité.


De nouveaux rapports révèlent que la grande majorité des composants de open-source sont "intrinsèquement risqués".
Aujourd'hui, la société Lineaje, spécialisée dans la gestion de la sécurité de la chaîne d'approvisionnement ( software ), a publié un nouveau rapport intitulé "What's in Your Open-Source Software ?" qui révèle que 82 % des composants de open-source software sont "intrinsèquement risqués" en raison d'un mélange de vulnérabilités, de problèmes de sécurité, de qualité du code ou de problèmes de maintenabilité.
Le rapport a révélé que 70 % de software dans l'entreprise est open source, juste une semaine après que la CISA ait appelé les fournisseurs de software à mettre en œuvre des pratiques qui leur permettent de livrer un code sécurisé "prêt à l'emploi". Il s'agit notamment d'être plus proactif dans la gestion du risque open-source .
Open source n'ira nulle part. Peut-on le sécuriser ? La réponse se trouve dans VentureBeat..




