Great companies trust Keyfactor.
When everything is connected,
everything has to be trusted.
More devices. More workloads. More transactions. Digital trust has never
been so vital—or so complex. But do it right, and you won’t just boost security;
you’ll get unmatched agility, control, and scalability. That’s where we come in.
IDENTIFY
Powerful, highly scalable
PKI for enterprise or IoT.
Seamlessly issue and manage trusted
identities—for every machine and person.
The easily scalable, open-source version
of Keyfactor’s PKI platform.
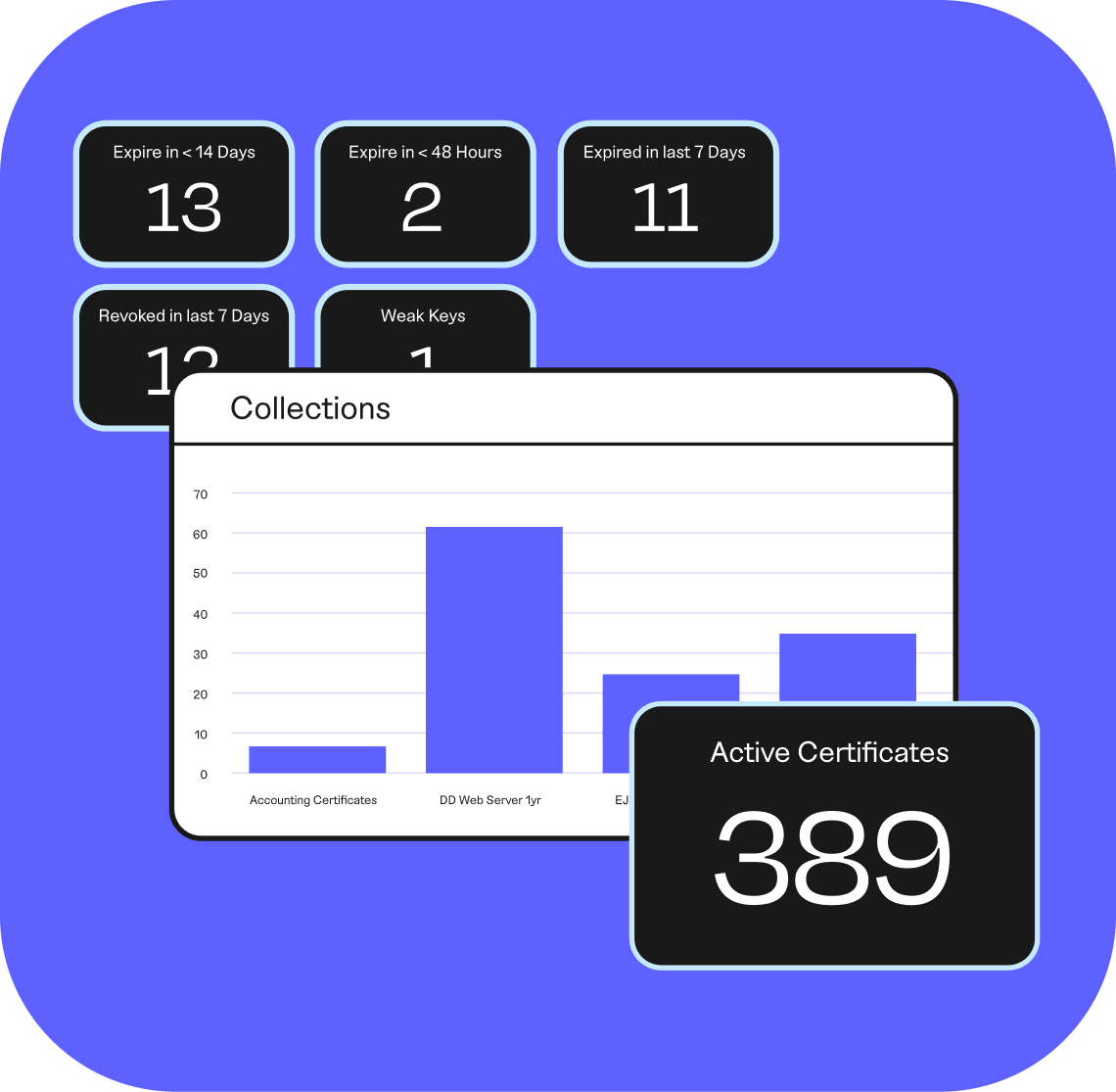
MANAGE
Visibility, control, and
automation for IoT and
machine IDs.
Discover and automate your PKI and
digital certificates from one platform.
Manage all of your IoT device identities—
at scale—from a single place.
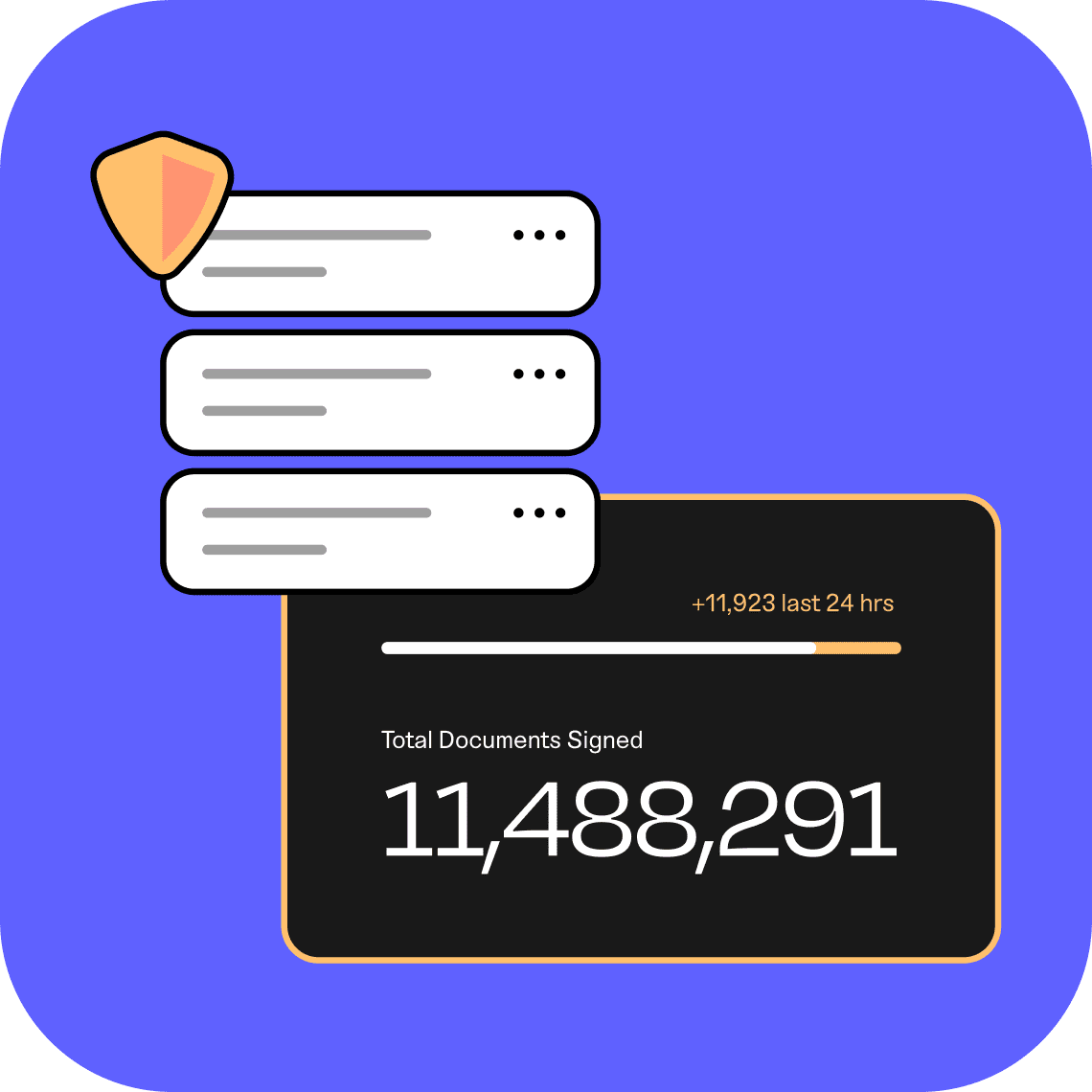
SIGN
Fast, secure, and flexible
signing solutions.
Easily protect keys and sign code with
native tools.
Automatically sign code and documents
fast with APIs.
Find Your Digital Trust
loT
Embed each device with a trusted and unique identity at design, then keep it secure throughout the product lifecycle.
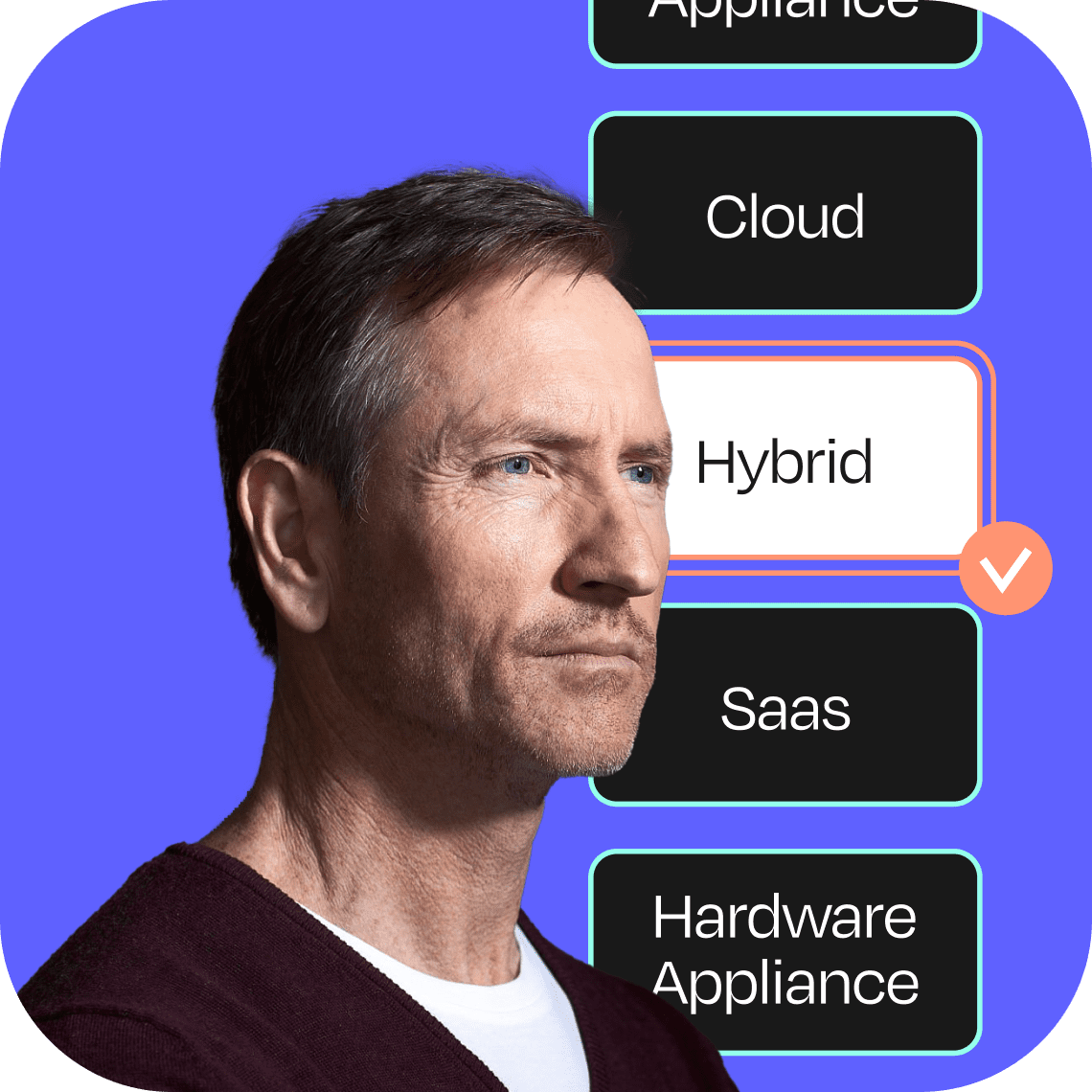
Enterprise IT
Establish digital trust across enterprise and multi-cloud environments with trusted PKI and machine identity automation.
Keyfactor by the Numbers
1500 +
Global Customers
95 %
Customer Retention
90 %
Support Satisfaction
4.6

G2 Reviews