Trust Infrastructure
for AI & Machines
Keyfactor puts you in control of the machine identities and cryptography that secure your data, machines, and AI—now and into the quantum era.
Trusted by 40% of fortune 500
AI and quantum are reshaping trust
Machine identities and cryptography encrypt data, verify trust, and authenticate every connection. They used to be background noise. Now they’re critical infrastructure.
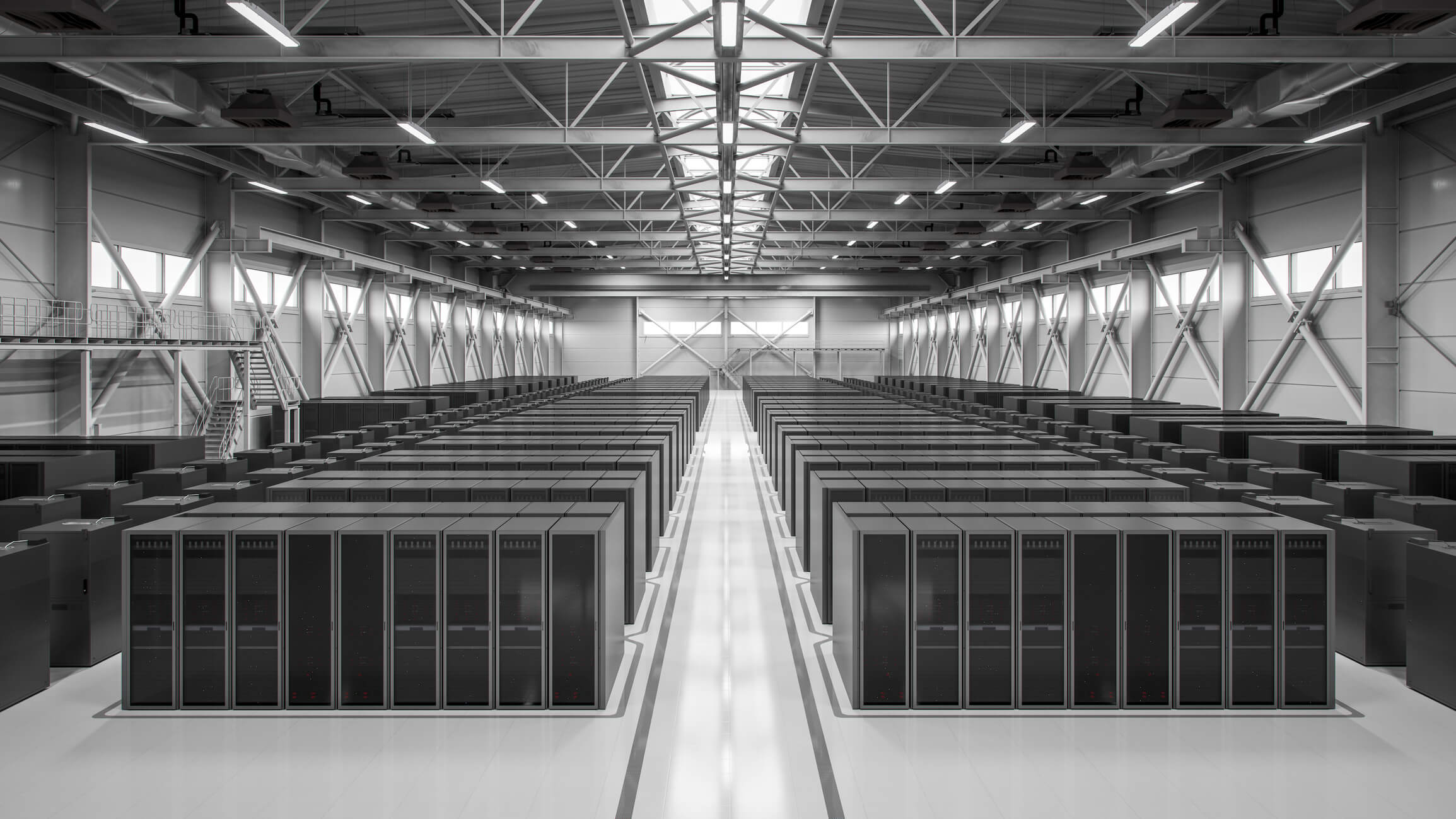
Machines
everywhere
Machine identities for every
human identity.
AI and machines are driving
a relentless need for more
cryptographic identities.
Lifecycles
accelerating
Increase in certificate renewals
with 47-day TLS lifespans.
Certificates expire in weeks,
not years. Outages take
down critical systems.
Cryptography
at risk
Traditional cryptography will be
rendered unsafe to use.
Cryptography is everywhere.
Most of it is untracked.
Much of it is vulnerable.
Regulations
tightening
Don’t have a complete inventory
of their cryptography.
New requirements for
cryptographic inventory and
management are here.
INTRODUCING THE KEYFACTOR PLATFORM
Meet the control plane for
your trust infrastructure
Keyfactor gives security teams visibility and control over the identities and cryptography that secure every digital interaction, so your business keeps running—uninterrupted.
Visibility & Context
See everything.
Understand your risk.
Continuously discover and observe cryptographic assets across your environment—all in one place. Identify vulnerable and out-of-policy assets in real time, so you can assess risk and take action before it impacts your business.
Trust & Identity
Establish trust.
Secure AI & machines.
Issue trusted identities for every machine, workload, and AI agent with a modern, quantum-ready PKI. Verify the integrity of your software and systems with secure code signing.
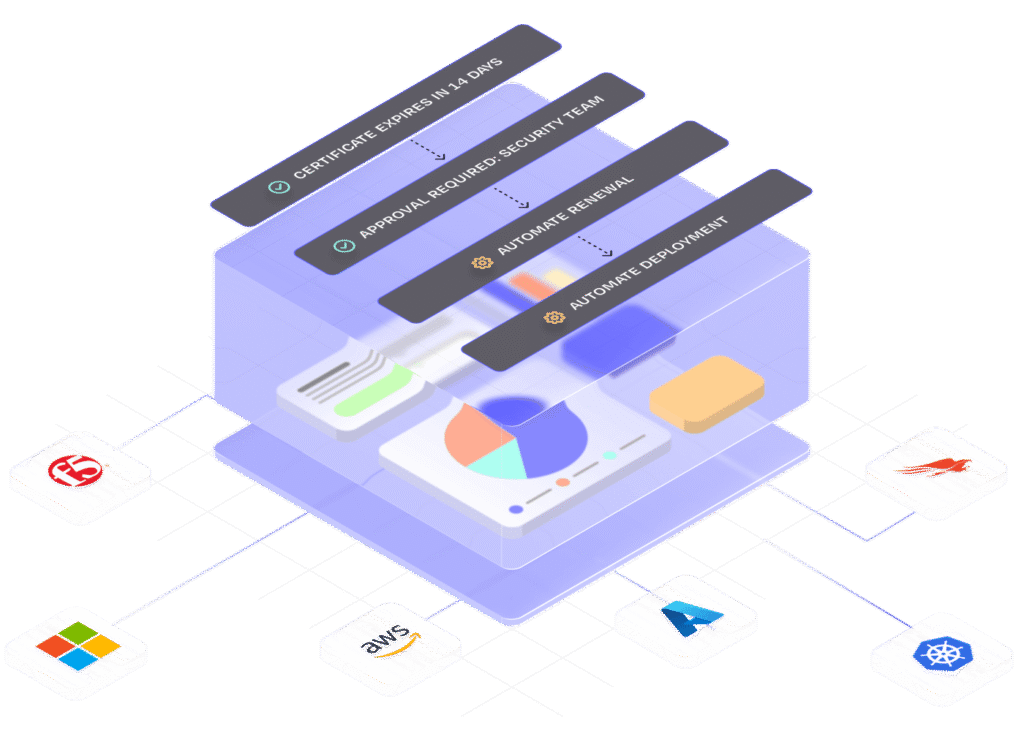
Lifecycle Automation
Automate at scale.
Reduce risk.
Orchestrate certificate lifecycles with end-to-end automation to reduce manual effort and prevent outages. Maintain control at scale while proactively identifying and remediating cryptographic risk.
Resilience & Agility
Adapt to change,
without interruption.
Transition to post-quantum cryptography and stay ahead of evolving threats and standards. Ensure continuous compliance and clear insight into your cryptographic posture—while keeping your business running.
Industry leaders ensure digital trust in a post quantum world
Trust in action
See what Keyfactor’s Trust Control Plane can do for you.
Industry recognition
Keyfactor delivers 356% ROI over three years
Forrester TEI Study reveals that Keyfactor delivers significant ROI
Keyfactor ranked number one in Enterprise PKI
ABI Research PKI Vendors Report named Keyfactor the best PKI solution
Security and privacy trusted by the Fortune 500 and government agencies worldwide
Keyfactor maintains certifications and compliance with the world’s leading regulatory and security frameworks.