Whether you are managing keys and certificates supporting secure shell (SSH), SSL/TLS, and other public key infrastructure (PKI)-related systems and operations, you likely have a crypto-mess on your hands.
Why?
Like many enterprises, decisions around cryptography management are made by disparate groups. Each ECM function will have different teams dealing with challenges around their specific cryptography management.
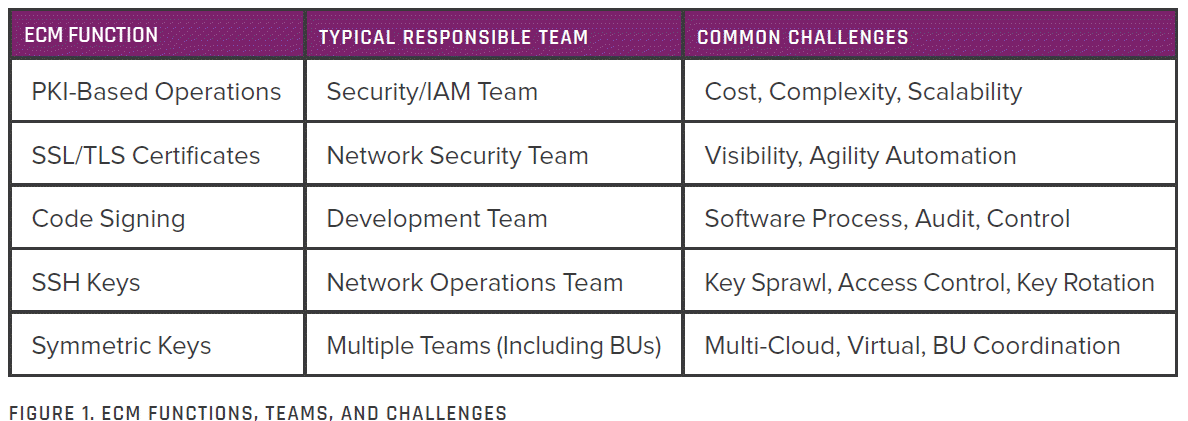
What's Needed to Clean Your Crypto-mess
What CISOs and security leaders look to help manage the security of keys and secrets is seamless orchestration across business units. This orchestration makes sure their systems are protected, and their employees can do their work efficiently without introducing vulnerabilities.
A new report published by TAG Cyber, give a practical methodology for managing the end-to-end cryptographic life cycle, is set forth for enterprise teams.
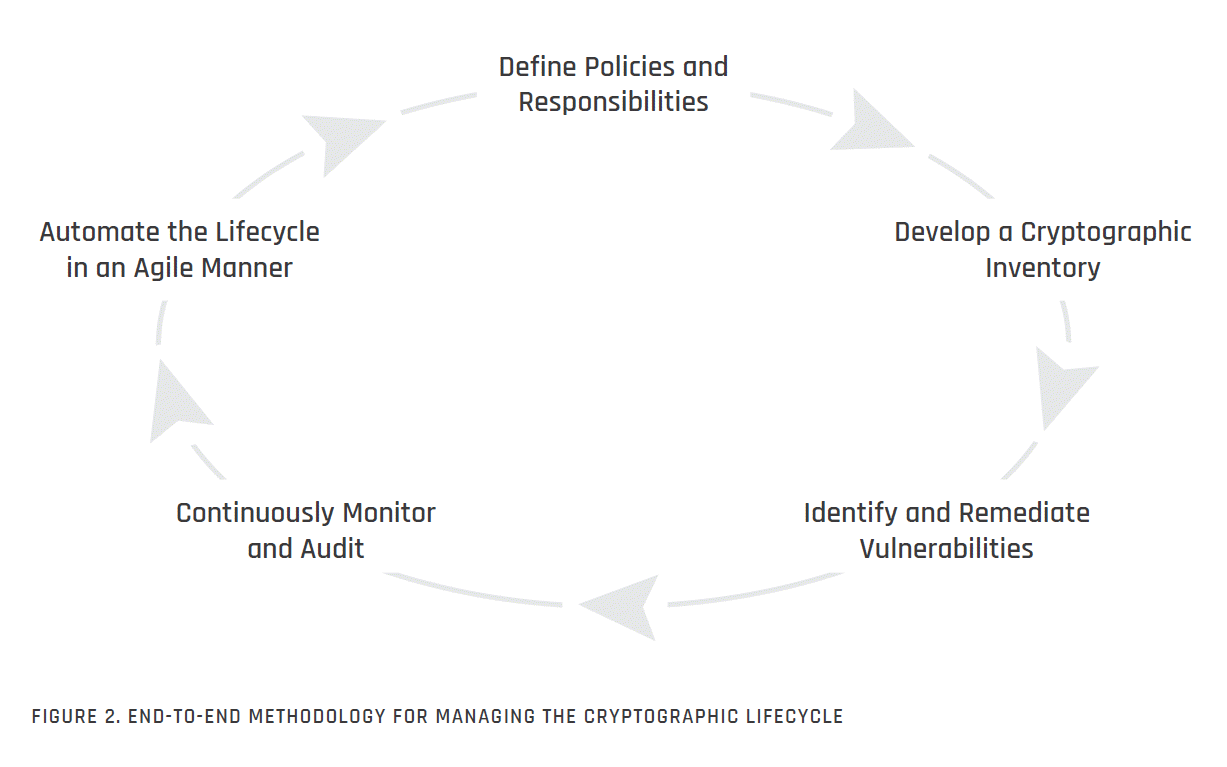
Step 1: Define Policies and Responsibilities
Like any other IT or cybersecurity policy, ECM’s defining policies and responsibilities must streamline the component tasks to achieve security objectives and business goals.
A thorough policy should start with high-level strategy and proceed to more tactical details, including generation, distribution, accounting, storage, use, and destruction of keys and authorization guidelines and security controls for keys.
Important steps in the creation of an organizational ECM lifecycle process include the following tasks:
- Define ECM Goals and Strategy: Develop and document the organization’s key and certificate management goals and strategy, including whether the program will be centralized or de-centralized, who will be responsible, where policies will be stored, and how they will be maintained.
- Document Existing ECM Architecture: Develop and document the organization’s current key and certificate management architecture. This requires early attention to inventory for the relevant ECM tasks that are ongoing.
- Identify Relevant Encryption Requirements: Validate present and future encryption requirements, including any audit or regulatory mandates from external bodies.
Step 2: Develop a Cryptographic Inventory
Automated cryptographic inventory tools locate, identify, and report configured keys and certificates. These tools help administrators track cryptographic usage, and help limit key sprawl, validate access controls, and ensure the timely rotation of SSH keys.
Some common methods of discovery that are critical to gaining complete visibility using tool support include the following:
- CA Integration for SSL/TLS: Direct integration with certificate authorities helps to identify every certificate issued.
- Network-based Discovery for SSL/TLS: Tools can scan IP ranges, subnets, and ports to find SSL certificates.
- On-Device Discovery of SSH and SSL/TLS Keys: This includes agent-based or agentless discovery of key stores and file systems.
- IaaS for Cloud-Issued Certifications: New protocols such as the Key Management Interoperability Protocol (KMIP) from OASIS help different cloud providers discover certificates and provide bring-your-own-key (BYOK) capabilities.
Step 3: Identify and Remediate Vulnerabilities
The use of cryptography can include vulnerabilities that might threaten the confidentiality, integrity, or availability of the data or systems which it is meant to protect.
Some of the more common vulnerabilities enterprise teams might identify in their deployed cryptographic algorithms, protocols, tools, and systems include the following:
- Algorithms: Weak algorithms that may be vulnerable to present and future attacks
- Storage: Improper key storage and management which can lead to lost data
- Configuration: Poor configuration management which complicates administration
- Rules: Lax rules for key generation, authorization, and authentication
- Visibility: Lack of visibility into digital signing and other cryptographic tasks
Step 4: Continuously Monitor and Audit
Management practice in any organizational use of cryptography should involve technology and processes for continuous monitoring and regular auditing. Continuous coverage implies having an accurate and ongoing understanding that approximates real-time visibility to the greatest degree possible. To do this, an organization must have defined plans for all aspects of ECM review, data collection, monitoring, and assessment. A sample checklist may include:
- Audit: ECM teams should regularly audit access and use of code-signing certificates, with attention to signers, approvers, and signing times.
- Monitor: Monitoring certificate authority-related activity will help ensure that certificate issuance remains within defined thresholds.
- Time Stamps: ECM teams should be continuously reviewing time-stamp code for issues or anomalies.
- Expiration: Teams should identify and remediate expired or out-of-policy certificates as policies evolve (e.g., self-signed, unauthorized, or weak).
- Authorization: It is important to audit processes for authorization and verification of trustworthiness of trust anchors.
- Signing: Review of the code signing submission and approval process can prevent the signing of unapproved or malicious code.
- Revocation: The monitoring process should include repeat audit of certificate revocation processes.
Step 5: Automate the Lifecycle in Agile Manner
Each of the four steps described above include references to the use of automated tools. This is driven by the desire to scale the ECM process, and to provide continuous visibility into inventory, usage, and vulnerabilities.
The goal of this fifth step—which can be performed in parallel with the other steps of the process—is to unify the automation into a common architecture to streamline usage and minimize both risk and costs.
The challenge in this automation design and development task is to select a suitable end-to-end platform that works seamlessly across all aspects of the environment and that integrates with development and deployment lifecycles. Enterprise security teams are thus advised to do their homework to select the best commercial ECM partner that can help automate the process in an effective manner.
Start Cleaning Your Mess
Enterprise security teams will continue to struggle with keeping control over their entire crypto process until the prioritize a unified strategy. Keyfactor simplifies and unifies the crypto process as a whole, allowing our customers to gain visibility, set procedures, and use automation to get themselves out of a crypto-mess.
To read the entire report and see how you can start with a self-assessment of how cryptography is being used and managed in your enterprise today, download it here.
And to learn even more, register for our upcoming webinar, How to Approach Your End-to-End Cryptography Strategy: