In September 2021, digital security experts uncovered a widespread attack targeting Windows users. The attack used malware to launch a fake expired certificate alert on websites that prompted users to download an update, which actually contained malicious software giving hackers remote access to infected computers.
Here’s a look at how the attack was executed, what we know so far about its impact and tips for how to protect your organization from threats like this going forward.
Inside the Attack: How Hackers Created Fake Expired Certificate Alerts
The attack targeted Windows Internet Information Services (IIS), which is the Microsoft web server installed on all Windows versions since Windows 2000, XP and Server 2003.
When vulnerable users visited certain sites, they saw an error page with a note about a potential security risk and a recommendation to download an updated security certificate to proceed.
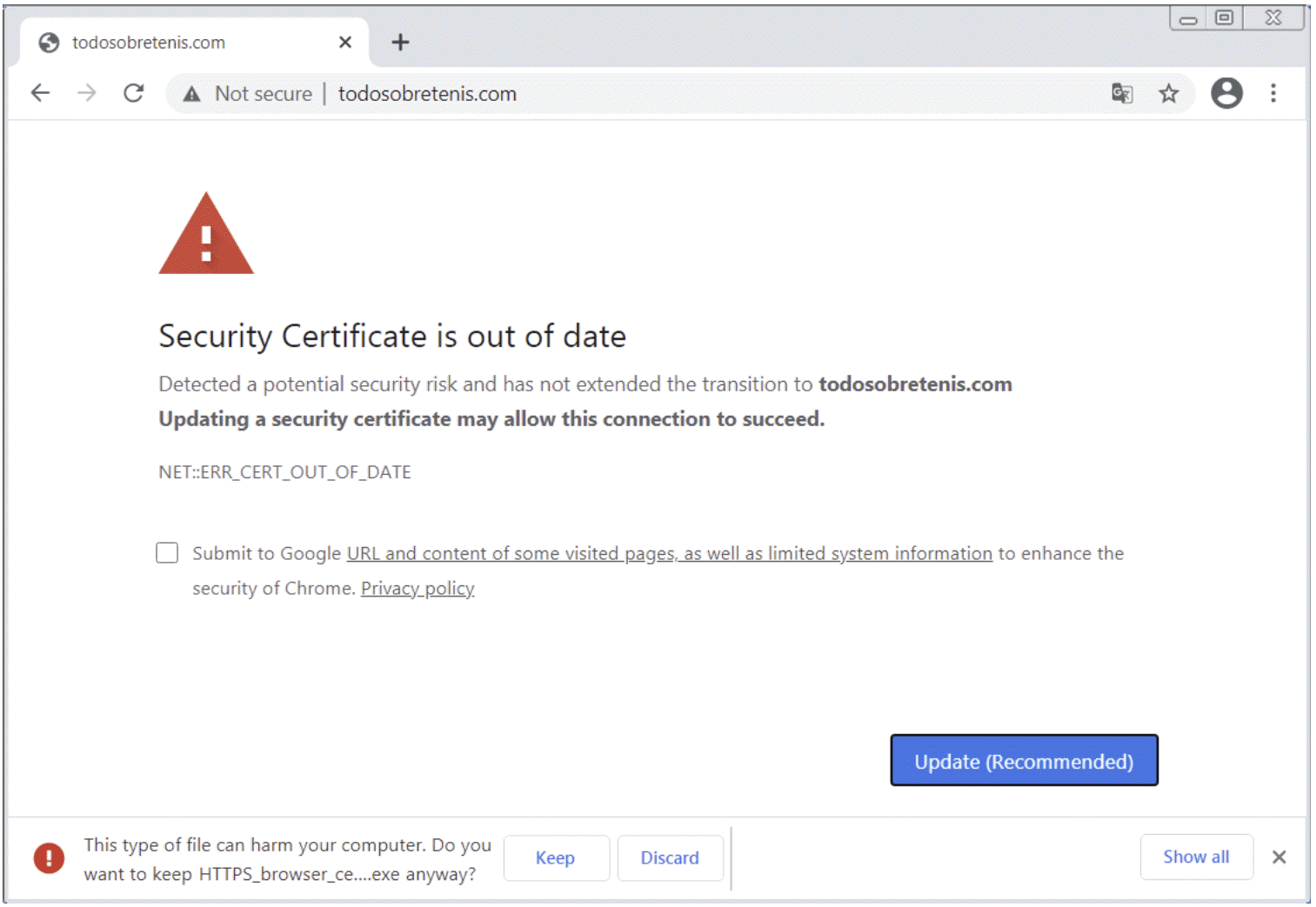
Clicking to make the update actually downloaded a fake update installer signed with a certificate from the Digicert root Certificate Authority. This update included malware known as TVRAT, which provides full remote access to any device on which it’s installed through TeamViewer remote control software. The TVRAT malware was also used in a 2013 attack involving Microsoft Office attachments.
Completing the installation triggered a notification to the hackers, who could then take control over infected devices.
The Impact of the Attack: What We Know So Far
Unfortunately, this attack is only the most recent example of a series of attacks targeted at Windows IIS.
Several other vulnerabilities on IIS have come about in the past few years, including two others in 2021: A wormable vulnerability for which Microsoft issued a patch in May and an advanced persistent threat based on a few exploits from a group known as Praying Mantis that targeted Windows IIS in August.
Overall, this series of attacks not only highlights certain vulnerabilities to be aware of, but also emphasizes the importance of regular security updates and overall user education.
Most importantly, the fake expired certificate attack sheds light on the importance of visibility into certificate lifecycle management to better understand potential risks like these.
Lessons Learned: Protecting Your Organization
Digging deeper, there are two critical lessons learned from this attack that can help security teams protect their organizations from threats like this going forward:
1) Don’t underestimate the importance of PKI management
Effective PKI management can provide the necessary visibility and reporting to get ahead of potential issues like what resulted from the fake expired certificate attack.
First, having proper scanning and detection capabilities in place can help security teams easily determine if a certificate has been installed on a server. It can also provide additional important details like when it was installed, who installed it and even the purpose of the certificate. This information can help teams stay in control of certificates across the entire organization.
Second, having a system that can provide a complete inventory of certificates can make it possible to quickly identify any anomalies — empowering security teams to investigate what’s going on early to avoid small issues growing into even larger issues.
2) Make end users a part of the solution with education
Additionally, it’s important to recognize that end users can be either a security weakness or a security asset depending on the education provided to them.
Ideally, teams should educate users on a variety of important security measures, including the fact that they should never accept or install a certificate that is not known to them. No matter how straightforward this might seem to security professionals who live and breathe this everyday, taking the time to educate end users on a variety of best practices can go a very long way toward decreasing human-driven vulnerabilities (such as users downloading a fake certificate).
What’s Next?
We can’t overlook the criticality of the September 2021 fake expired certificate attack. This attack used malware to create a highly realistic-looking alert, including a certificate signed by a well-respected root CA, with the purpose of downloading a malicious program to give hackers remote access to devices.
It may be the most recent example of a sophisticated attack, but it certainly won’t be the last. Security teams should stay up-to-date on the latest threats like these to understand how attacks are evolving and how they can continue to upgrade their security posture and educate users to protect their organizations going forward.




