It goes without saying that hybrid and multi-cloud are the new norm. What’s not so obvious is how organizations adapt their public key infrastructure (PKI) and certificate management strategy to this new reality. In this blog, we’ll explore how IT and security teams can leverage Google’s cloud-native PKI, known as Certificate Authority Service (CAS), integrated with their existing Active Directory (AD).
PKI and digital certificates are key ingredients to security in a multi-cloud environment. As the foundation for authenticating and encrypting machine-to-machine connections, digital certificates help teams to establish digital trust in this highly distributed and untrusted environment.
Behind every certificate is a certificate authority (CA). Microsoft’s Active Directory Certificate Services (ADCS), also known as Microsoft CA, has long been the de facto choice to support traditional PKI use cases. However, as companies make the shift to the cloud, the PKI landscape has changed.
Cloud-native applications, micro-services architectures, and ephemeral workloads simply cannot be supported by a traditional on-premises CA, like Microsoft ADCS. The reality is that PKI no longer consists of just one or two CAs behind the firewall – it’s built with a mix of public, private and cloud-based CAs. In this new “decentralized” PKI model, organizations need a way to effectively discover certificates across their infrastructure, monitor compliance and expiration, and automate the lifecycle of certificates to reduce the risk of human error and outages.
Keyfactor and Google CA Service
Today, Keyfactor integrates with Google CA Service, making it easy for organizations to manage their GCP-issued certificates, as well as those issued from any other CA. It allows teams to leverage cloud-native capabilities, while providing real-time monitoring and workflows to automatically provision certificates to cloud workloads, such as Google Cloud Load Balancer.
In some cases, organizations prefer to leverage Google CA Service in place of their traditional on-premise CAs, allowing them to retire their legacy AD CS infrastructure. The challenge is that they still need to integrate with their existing Active Directory users to support auto-enrollment.
Autoenrollment with Keyfactor Command
Keyfactor’s auto-enrollment solution leverages the power of Keyfactor Command to integrate Google CA Service with an organizations on-premise Active Directory. The solution effectively serves as a Registration Authority (RA), routing certificate enrollment for user and device certificates through Google CA Service, instead of AD CS.
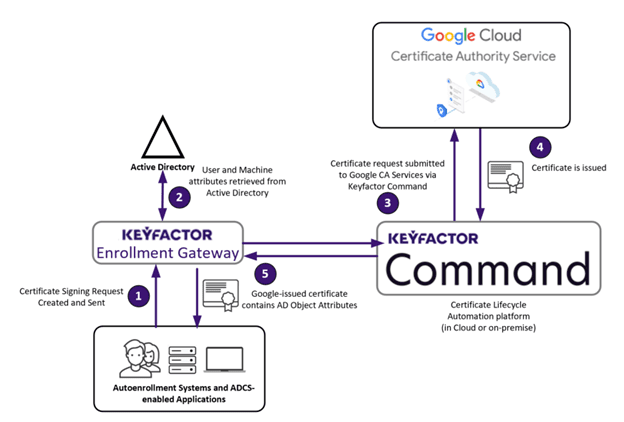
With General Availability expected in Q3 2022, this solution will allow customers of Google and Keyfactor to handle ADCS use cases such as Windows Autoenrollment with ease – and without needing a Microsoft CA.



