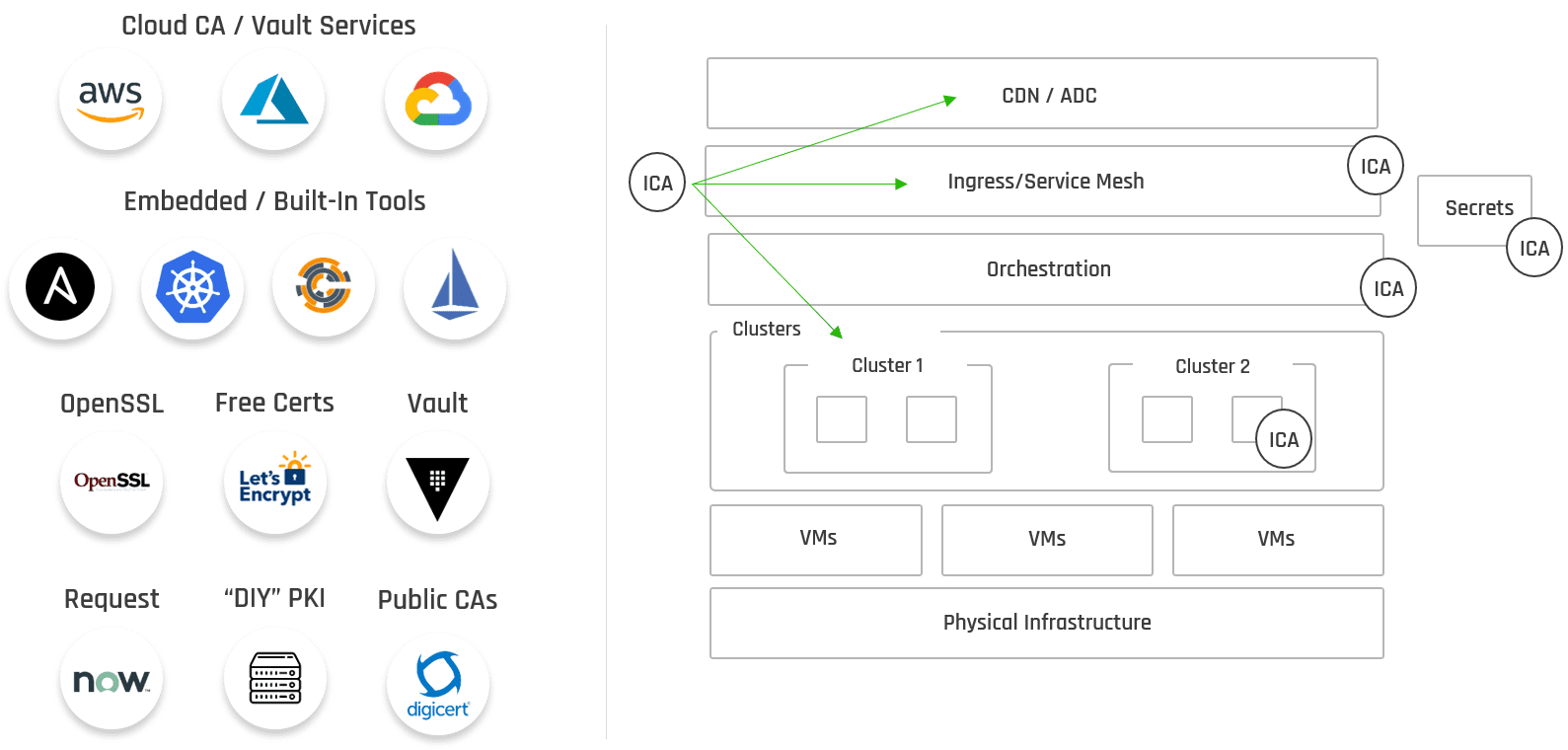
Digital certificates (e.g. SSL/TLS, X.509) can be issued and managed through many different tools in your DevOps tool-chain. However, the more tools you have for managing the issuance of these certificates lead to gaps in security governance and oversight.
Watch Anthony Ricci, VP of Engineering at Keyfactor, as he walks through a sample technology stack and the role certificates play in a development life cycle.
Full transcript below.
Building a Sample Technology Stack
How are you doing, folks? My name’s Anthony Ricci. I’m The VP of engineering at Keyfactor. Today we’re going to talk about the challenges of digital certificates within a DevOps environment.
Below is an example of a technology stack that we’re going to go through and explain maybe possibly what your organization may do to develop, or to deploy your applications.
Once we do that, we’ll then walk through how secrets and certificate management play a role in DevOps.
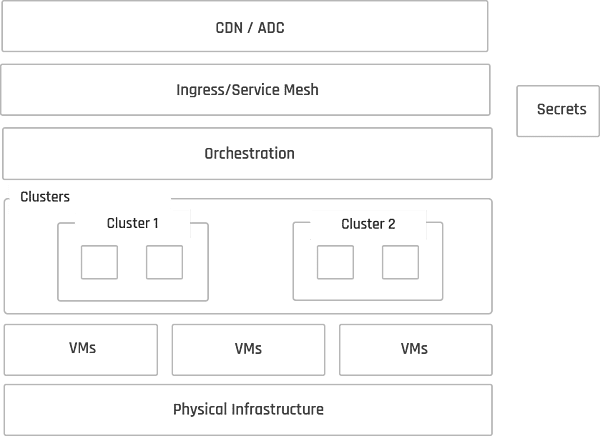
Infrastructure
As we start at the bottom, here’s your infrastructure. Essentially it could be bare metal. It could be a data center, or multiple data centers, for that matter. Maybe a cloud-based environment. It could be AWS, Google Cloud, Azure, but it doesn’t really matter. This is where it starts, and then we’ll focus on the deployment of your virtual machines within those environments.
And then once you got essentially your infrastructure configured, now let’s talk about your clusters.
Clusters and Service Mesh
You may have multiple clusters so in this example, we’ll have two clusters. Once you configure a cluster, you need an orchestrator to manage it. Most people are with deploying Kubernetes, and possibly using a service mesh like Istio.
Using a service mesh depends on the complexity of your environment or multi-environment. The service mesh gives you the capability for service-based discovery, DNS management of your different services, and pods within those environments. This allows everything to communicate appropriately. It also allows you to manage in an ephemeral environment, where you’ve got things spinning up and spinning down all the time.
Logical Ingress and Applications
You may also have a logical ingress here. So this will be an edge, where you have some kind of web server that’s going to be deployed, kind of serve us up. Whether it’s an API, or website, or application that you have certain people using. And of course, your application, or the number of apps, that you’re deploying. This is a very simple diagram where you started from the bottom, from infrastructure all the way to applications.
Now let’s start talking about security.
Adding in Secrets and Cert Management
Kubernetes comes on with onboard SED, where you can deploy things like credentials and secret information that you’re going to use. HashiCorp Vault is another product that has a very good interface and a lot of good features in there to manage application secrets at an enterprise scale.
The next thing is digital certificates. A lot of people just kind of leverage or think about SSL certificates as being the only digital certificates you use. However, there are lots more.
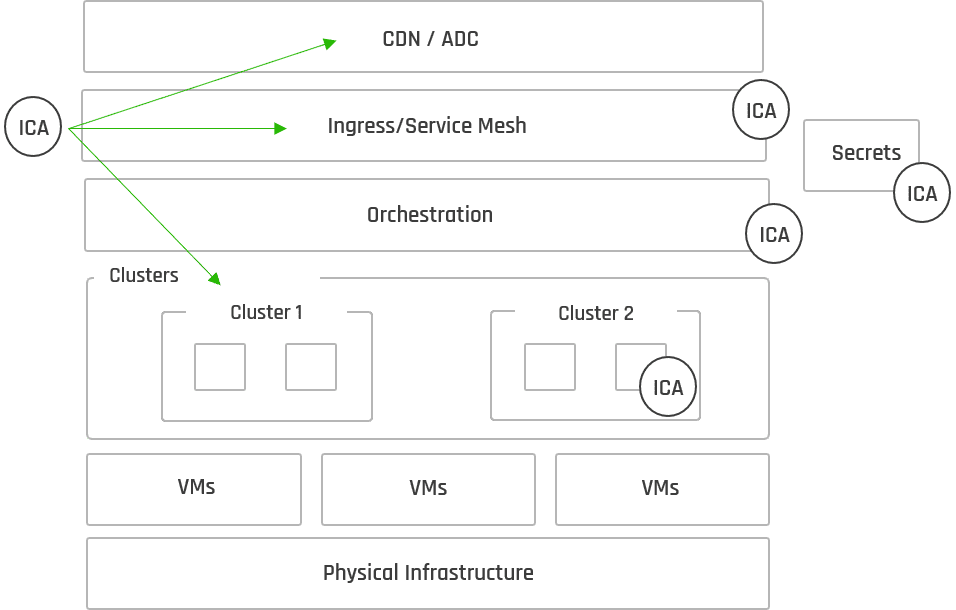
We have Client Auth in an environment like this. The ingress supports the use of SSL certificates. Your orchestrators or pods with services will need to deploy mutual authenticated certificates (MTLs). With all these tools and apps needing certificates, where are you going to get them?
Well, that’s a great question.
Internal CAs (Certificate Authorities)
Kubernetes has what we call an onboard CA. Istio has an onboard CA. And, you guessed it, Vault also has an onboard CA.
From a DevOps perspective, you perceive that you do have security, which you do. However, the problem is the management of that security. What we’re trying to do with these DevOps environments or the flow of your applications and deployment, is to minimize the total cost of ownership (TCO).
In this case, you’re actually increasing your TCO. You have four different implementations with different CAs that you’re deploying within that environment. The challenges arise when you implement these CAs, policy enforcement and how you handle that, can be significantly different from one technology to another.
This is a big problem in the digital space. It’s always been a big problem, but what if we had a solution for you to be able to kind of solve that?
Certificate Automation for DevOps
Well, we do, and it’s called Keyfactor.
We have a PKI as-a-Service, or public key infrastructure, as a service, which allows you the capability to alleviate the management of those digital certificates from your environment. And it allows us to do it on your behalf.
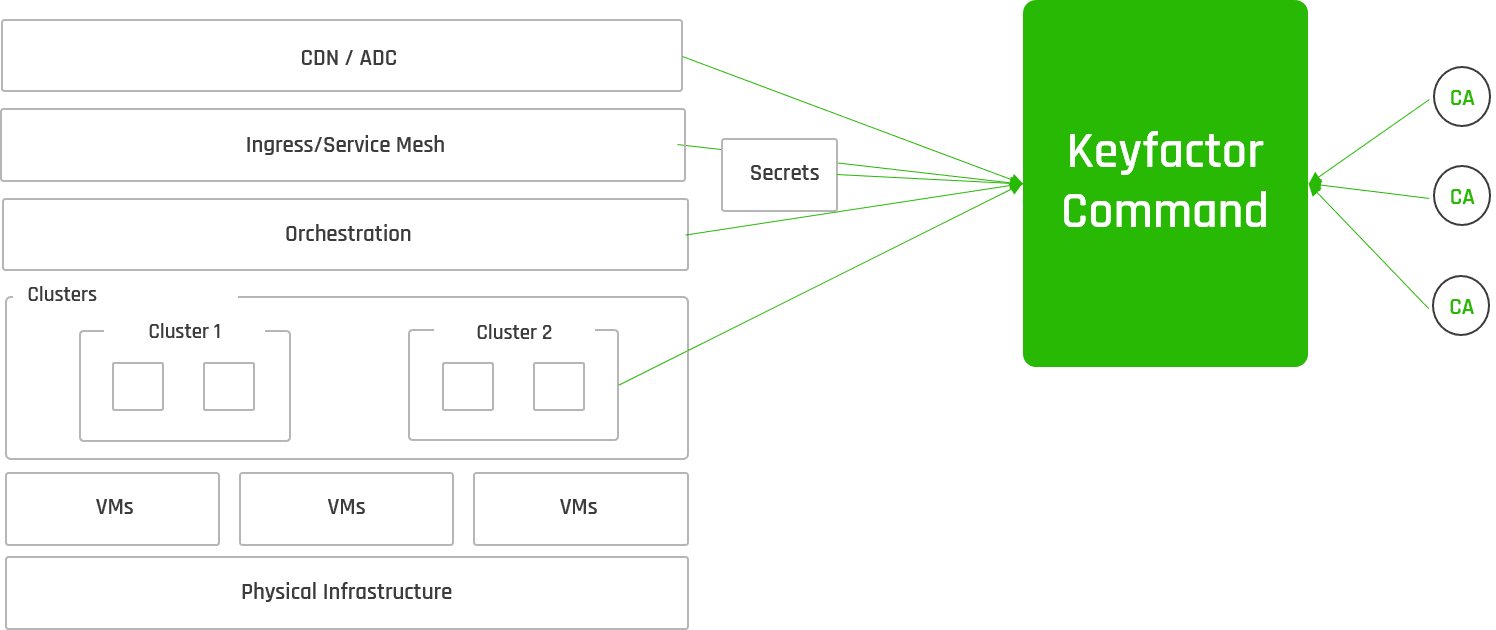
In this case, what we try to do is eliminate the issuance of these CAs from these onboard, or these technology stacks, and then create what I call the last mile integration points into Key factor. This gives you a unified approach to the management of certificates within the environment. Now you have interoperability between the different technology stacks and the capabilities for Keyfactor to manage those CAs behind the scenes.
What does that really give you? From the DevOps perspective, what that gives you is control, and visibility, and autonomy between all your different CAs. We give your InfoSec group the ability to do policy enforcement, audibility of those CAs, and ensure that you’re staying consistent or compliant within your industry, as well as your organization.
And then allow you as a DevOps expert or application developer to focus on features and functions of your application, and make sure the deployment of that in the stack.