CSS recently discovered and published information on a potential privilege escalation attack in SCEP-based Certificate Issuance Systems. After this discovery, CSS created the SCEP Validation Service, which aims to close this attack by validating the certificate contents before the Certificate Authority sends it to the requestor. CSS’ patent-pending solution ships today with our Mobile Certificate Management System (mCMS) v 1.1 software. CSS’ SCEP Validation Service is architected as a set of components that can also be integrated into 3rd-party Mobile Device Management (MDM) products.
3rd-party products that meet these requirements may be good candidates to integrate with CSS’ SCEP Validation Service:
- Utilize a Microsoft Certificate Authority (Standalone or Enterprise)
- Facilitate iOS devices to enroll for a certificate through a Microsoft NDES (SCEP) Server
- Built with .NET, or ability to integrate with WCF-based SOAP Services
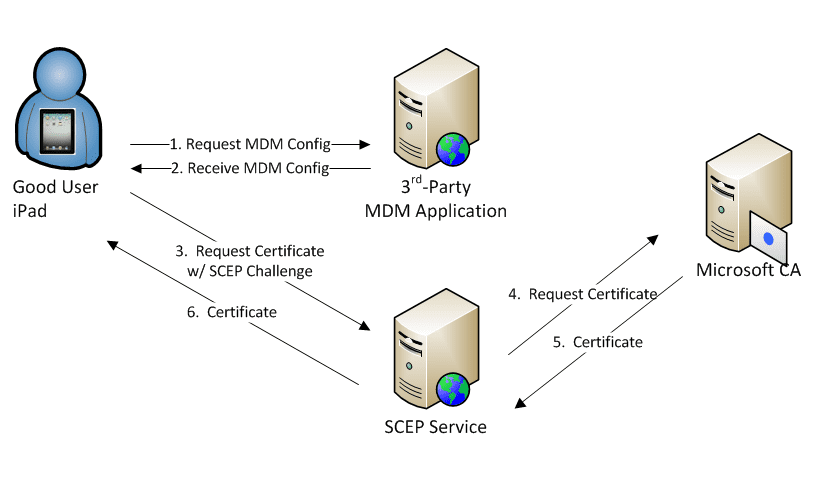
Normal User Scenario
Let’s take a look at the normal user scenario with NDES and the CA. In the diagram below, an honest user has requested a certificate. The MDM gives a configuration containing a SCEP Server URL and SCEP Challenge to the device. The device generates a key on the device and uses this configuration data to request a certificate from the specified SCEP Server. If successful, a certificate is issued.
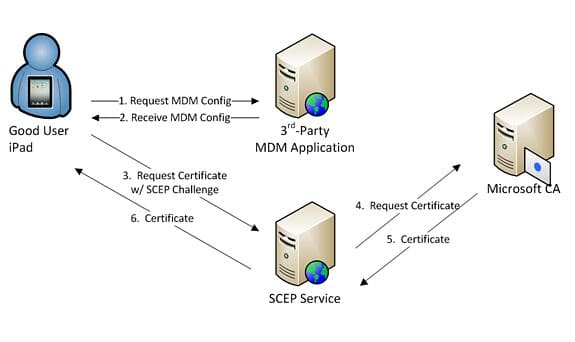
Malicious User Scenario
As noted in the CSS whitepaper SCEP and Untrusted Devices, if a valid but malicious user obtains a valid SCEP Challenge (regardless of it being a static or dynamic password), they may be able to use it to enroll for a certificate for a different identity or purpose than would be otherwise allowed.
In the diagram below, a malicious user has obtained a SCEP Challenge from his or her MDM system. Instead of allowing the device to generate a key and PKCS#10, the user crafts a PKCS#10 with a Subject Name field value that gives them a different (and potentially higher-privileged) identity.
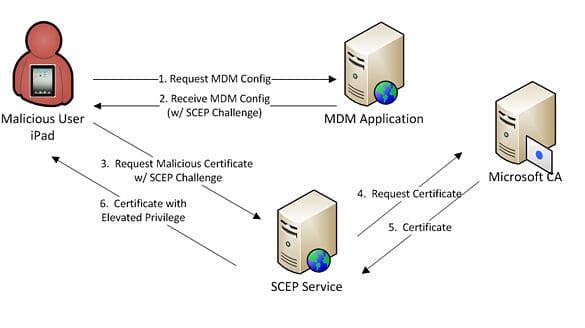
3rd-Party MDM with SCEP Validation Components
With the SCEP Validation Service integrated into an MDM Application, the scenario above can be prevented. CSS’ VSCEP solution adds two steps to the certificate issuance process.
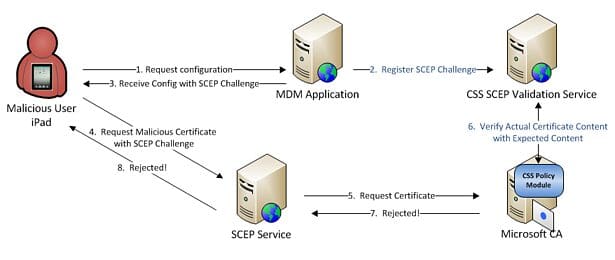
In the diagram above, Step #2 is the only source-level integration point between the MDM and CSS’ SCEP Validation Service. When a user enrolls a device with the MDM Application, the MDM registers expected certificate content with the corresponding SCEP challenge using the CSS SCEP Validation Service. This content includes information such as the expected subject, subject alternative name, template, key usage, and extended key usage values.
Step #6 above shows how the Policy Module validates the new certificate content directly on the Certificate Authority, well before the certificate is sent to the requestor. The Policy Module works with the Validation Service to verify the actual certificate content with the previously registered expected content from Step #2. If the Policy Module finds that all of the data matches the expected content, the request is approved and the certificate is sent to the requestor. If the user has malicious intent, the Policy Module would detect the information mismatch and deny the certificate request.
The SCEP Validation Service is an IIS-hosted service that can live anywhere inside your client’s infrastructure. It exposes a simple, one method WCF-based interface to allow the MDM to register the user’s expected set of content. MDM applications do not have to integrate with the Policy Module itself. The Policy Module is installed directly on a Certificate Authority and configured to talk to the SCEP Validation Service.
Summary
Incorporating CSS’ SCEP Validation Service Components into your product is simple and only requires minimal source-level changes. The expected SCEP Challenges and certificate content need to be registered with the SCEP Validation Service, as shown above in Figure 3. The CSS Policy Module validates and enforces that each certificate is issued for the actual identity of the user. In addition to this source-level change, your product install must be modified to include the CSS components. CSS is eager to work with you to integrate our SCEP Validation Service into your MDM product.
Visit the Validated SCEP resource center for more information: https://www.css-security.com/vscep/