In this blog, Keyfactor experts explain how the ACME protocol works, why it is important for modern public key infrastructure (PKI) and certificate management deployments, and how it can help organizations achieve automation.
What is ACME?
ACME, or Automated Certificate Management Environment, is a protocol that makes it possible to automate the issuance and renewal of certificates, all without human interaction.
The Internet Security Research Group (ISRG) initially designed the ACME protocol for its own certificate service, Let’s Encrypt, a free and open certificate authority (CA) that provides domain validated (DV) certificates at no charge. Today, various other CAs, PKI vendors, and browsers support ACME to support different types of certificates.
ACME Versions
Introduced in 2016, the original ACME protocol, v1, offered a streamlined approach to obtaining SSL/TLS certificates, albeit limited to single domains. This foundational version laid the groundwork for automated certificate management.
A significant leap forward came with ACME v2 in 2018, expanding its capabilities to encompass wildcard certificates, a crucial feature for organizations managing multiple subdomains. Concurrently, the protocol’s security framework was fortified to enhance domain ownership verification and deter unauthorized certificate issuance.
Recognizing the protocol’s importance, the Internet Engineering Task Force (IETF) formalized ACME as a standard in RFC 8555 during 2019. This standardization spurred widespread adoption, with numerous clients integrating ACME support.
It’s essential to note that ACME v2 is incompatible with its predecessor. As a result, ACME v1 was phased out in June 2021, marking a complete transition to the enhanced v2 standard.
How does the protocol work?
By leveraging ACME, organizations can streamline and automate otherwise time-consuming processes, such as CSR generation, domain ownership verification, certificate issuance, and installation.
ACME is primarily used to obtain domain validated (DV) certificates. This is because DV certificates do not require advanced verification. Only the existence of the domain is validated, which requires no human intervention.
The protocol can also be used to obtain higher-value certificates, such as organization validated (OV) and extended validation (EV), but these cases require additional support mechanisms alongside the ACME agent.
The objective of the ACME protocol is to set up an HTTPS server and automate the provisioning of trusted certificates and eliminate any error-prone manual transactions. To use the protocol, an ACME client and ACME server are needed, which communicate with JSON messages over a secure HTTPS connection.
- The client runs on any server or device that requires a trusted SSL/TLS certificate. It is used to request certificate management actions, such as issuance or revocation.
- The server runs at a Certificate Authority (CA), like Let’s Encrypt, and respond to the requests of authorized clients.
There are many different ACME client implementations available for the protocol. It is designed to allow businesses to choose the CA they want, as long as the CA supports ACME.
Let’s Encrypt recommends using the certbot client, because it’s easy to use, it works on many operating systems, and it has helpful documentation. Other popular ACME clients can be found on GitHub, such as ACMESharp, acme-client, GetSSL, and many others.
Setting up an ACME client
Once you’ve selected a client, the next step is to install it on the domain/server where the certificates need to be deployed. ACME clients can run in almost any programming language and environment, and the setup process consists of just 5 straightforward steps to complete:
- The client prompts to enter the domain to be managed.
- The client offers a list of Certificate Authorities (CA) supporting the protocol.
- The client contacts the selected CA and generates an authorization key pair.
- The CA issues DNS or HTTPS challenges for the client to demonstrate control over their domain(s).
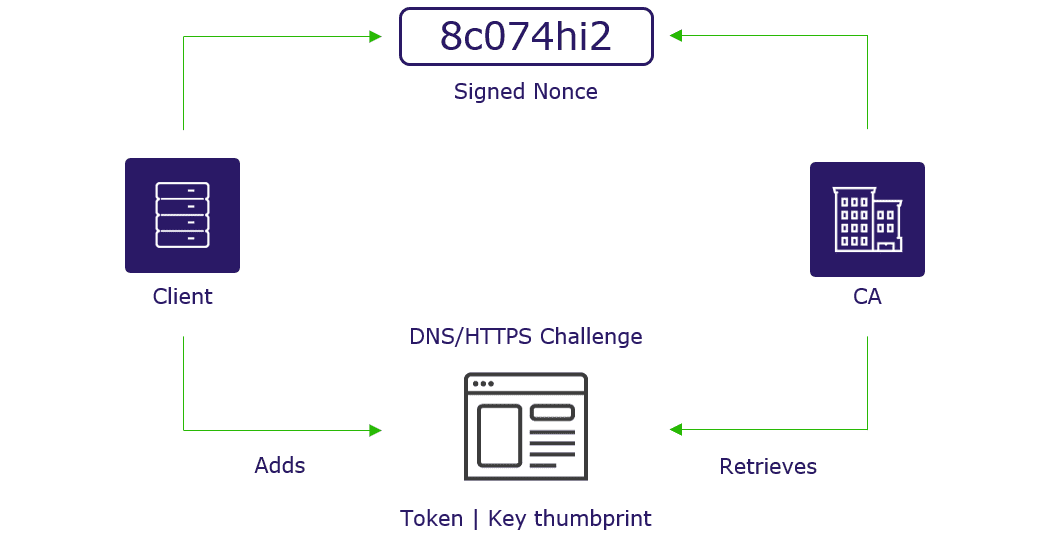
- The CA sends a nonce – a randomly generated number – for the agent to sign with its private key to demonstrate ownership of the key pair.
Figure 1: ACME client initial configuration process.
Once the CA verifies that the client is authentic, the ACME client is ready to request certificates on behalf of the validated domain(s).
Using ACME to deploy and manage certificates
Issuing and renewing certificates using the ACME protocol is simple. The client simply sends certificate management requests and signs them with the authorized key pair.
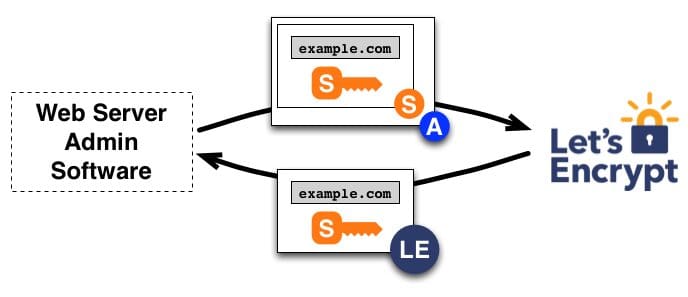
Issuance/renewal: a web server with the ACME agent installed generates a CSR, sends it to the CA, and the CA issues it. The process for issuance and renewal works similarly:
- The agent sends to the CA a Certificate Signing Request (CSR) requesting the issuance of a certificate for the authorized domain with a specified public key.
- The CSR is signed with the corresponding private key and the authorized key for the domain.
- When the CA receives the request, it verifies both signatures, issues a certificate for the authorized domain with the public key from the CSR, and returns it to the agent.
Figure 2: Certificate issuance/renewal. Source: Let’s Encrypt.
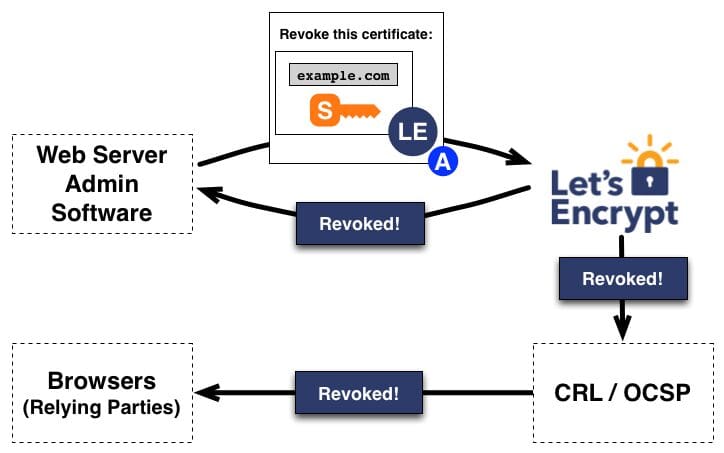
Revocation: to revoke a certificate, the agent signs the revocation request with the authorized key pair for the domain, and the CA validates the request. The CA then publishes the revocation information through CRLs or OCSP to prevent the acceptance of the revoked certificate.
Figure 3: Certificate revocation. Source: Let’s Encrypt.
How is the ACME protocol used?
In the 2024 State of Machine Identity Management Report, 40% of respondents revealed that their organizations still use spreadsheets to manually track certificates. On average, these organizations experienced roughly three unexpected outages caused by expired or misconfigured certificates within two years.
Despite the increasing use of modern, agile computing environments, many businesses continue to deploy and manage certificates using outdated techniques which are not adequate to meet the increased demands of today’s fast-paced environments. The manual management of certificates in spreadsheets or databases introduces inefficiency and risk of outage or non-compliance due to human error.
That’s exactly what the ACME protocol documentation highlights: “Existing Web PKI certification authorities tend to use a set of ad hoc protocols for certificate issuance and identity verification. These ad hoc procedures are accomplished by getting the human user to follow interactive natural-language instructions from the CA rather than by machine-implemented published protocols. In many cases, the instructions are difficult to follow and cause significant frustration and confusion.”
Using ACME to automate certificates
The expanded use of TLS server certificates to secure applications and data increases the likelihood of outages, since there are more certificates to track and more certificates per business application that can impact operations. Certificate requests, renewals, and provisioning using manual methods and spreadsheets take hours or days. In addition to being time-consuming, it is an error-prone process which might lead to painful outages.
ACME helps alleviate this troublesome situation by enabling IT administrators to prove to the CA in an automated manner that they control the domain, issue a trusted certificate, and keep track of the certificate expiration. Furthermore, they can automatically renew or revoke the certificate whenever this is required.
ACME brings automation into complex PKI deployments. Or as the protocol documentation states, ACME provides an “extensible framework for automating the issuance and domain validation procedure, thereby allowing servers and infrastructure software to obtain certificates without user interaction. Use of this protocol should radically simplify the deployment of HTTPS and the practicality of PKIX-based authentication for other protocols based on TLS.”
The importance of CA agility
CA agility is the ability to add/remove or switch from one CA to another is critical for business agility to avoid CA lock-in. It is an industry best practice to avoid creating a lot of dependency on a single CA. We should be able to switch CAs transparently, whenever it is required with zero business impact.
If an organization is locked in a single CA and something happens to them, such as a compromise or a service outage, it could have a big impact on the availability of online operations. For that reason, being able to switch to a backup CA is a best practice.
ACME makes the process of choosing a backup CA straightforward. There are currently many CAs supporting the ACME protocol and choosing one is only a few clicks away during the configuration stage.
Keyfactor + ACME
The Keyfactor platform supports automation and self-service using robust built-in functionality, in addition to open protocol-based certificate automation using ACME.
The platform can operate as an ACME server, helping you reduce manual, time-consuming processes, and human error with end-to-end certificate lifecycle management, and makes it easy for teams to get security-approved certificates.




