If you’re not watching your PKI…who is?
As ominous as the title sounds, this blog will actually focus on the parties that should have eyes on your public key infrastructure (PKI), rather than the “bad actors” who shouldn’t. The latter is no less important, however, and that could easily be the topic of a future blog.
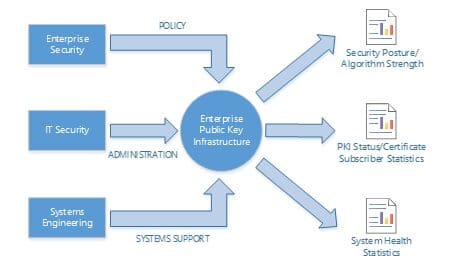
Figure 1: Enterprise PKI Inputs and Outputs
In line with the logical diagram shown above, common business and technical areas often include:
- Enterprise Security: Often in conjunction with corporate control and audit organizations, responsible for the definition of policy and the ability to audit against it.
- IT Security: IT Security teams are often tasked with the issuance and management of digital certificates as well as operational support of the PKI itself.
- Systems Engineering: PKI-dedicated systems are nearly always subject to the same local security administration, operating system patching, and maintenance window activities as all other systems in the enterprise. This is one of the key drivers of the need for well-defined and well-implemented security and auditing models within the PKI.
Among the common PKI pain points are adverse conditions that build over time such as general misconfiguration, security model degradation, non-compliance, and security vulnerabilities. Very often these conditions are attributable to a lack of visibility and proper monitoring by the appropriate parties. These conditions can, and often do, produce costly enterprise outages. So who should watch what? Some practical examples are outlined below.
- Platforms such as intranet web servers and network access control systems need consistent visibility on certificate states in order to stay operational. An unwatched RADIUS server authentication certificate, for example, could expire and disable authentication for an enterprise’s entire WiFi infrastructure. Certified Security Solutions’ automated digital certificate and PKI operations management platform, CMS Enterprise, allows you to configure certificate collections and attach metadata to alert your platform teams on impending expirations so that they can take action to prevent significant productivity and/or revenue losses.
- In light of numerous regulatory compliance requirements such as PCI, Sarbanes-Oxley, and Gramm-Leach-Bliley, corporate control and audit departments – as well as independent auditing bodies – increasingly rely on security posture reporting data, ranging from physical security to password policy to certificate signing algorithm strengths. As an example, CMS is frequently used to provide visibility into SHA1 certificates active within enterprise computing environments.
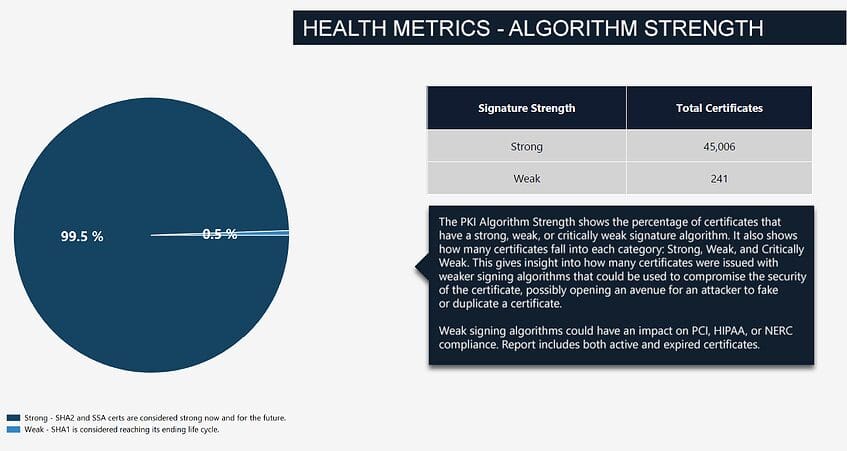
Figure 2: CMS Monthly Algorithm Strength Report
This blog has covered only a few examples of visibility requirements in relation to your enterprise PKI. CSS can work with you on an automated certificate and PKI management solution, CMS Enterprise, or a full scale PKI Managed Service, CMS Sapphire, to ensure that the right teams in your enterprise have eyes on the right data.




