Automotive IoT Security for Next Gen Connected Vehicles
It’s Just the Beginning: The Promise of Connected Vehicles
Connected vehicles represent the future of transportation for good reason. They offer numerous benefits to consumers and manufacturers, and many of these promises are already available on the market.
Some of the most notable benefits of connected vehicles include:
Enhanced Safety
Features like the ability to share telemetry information across vehicles can help drivers avoid accidents, while the ability for cars to self-identify ways to reduce emissions can help lower pollution rates.
Improved Maintenance
Connected vehicles can communicate with their manufacturer to provide information on wear patterns and usage that allow for better, more predictive maintenance (consider the case of fixing a problem before it becomes a problem). Manufacturers can also use this feature to connect with car owners and enable more direct notifications for important updates, such as warranty recalls or new service offerings.
Greater Mobility
Remote access and controls, like the ability to use an app to pinpoint a car’s location or determine if the doors are locked, provide vehicle owners with more control over their cars. At the same time, infotainment centers that link directly to navigation systems and receive regular updates for new features turn these vehicles into a platform for apps and content distribution that provide increasing value to their owners.
Complete Automation
Long term, one of the biggest goals of connected vehicles is to create truly autonomous vehicles, like a car that drives itself. This idea can not only save time, but also facilitate numerous use cases like car sharing.
Coordinated Automation
Building on the idea of automation, coordinated automation would allow vehicles to speak with one another and with traffic infrastructure, for example to share information like wind resistance and even location so that cars can route each other to avoid slow downs and coordinate with infrastructure like traffic lights. This state of coordinated automation could lead to tremendous efficiencies in terms of fuel savings, energy savings and so forth.
For these promises to reach their full potential though, security must be present, because without the right security measures in place these capabilities will present more danger than anything else.
The Security Risks of Connected Vehicles
If not properly secured, connected vehicles can easily become weapons, and we’ve already seen what attractive targets these vehicles are to hackers.
For example, in a 2015 hacking experiment, researchers remotely took over a Jeep by gaining access to install new software through text messages sent to the vehicle and then proceeded to crash the car on the side of the highway. This famous example is just one of many though, as no automaker is immune to this risk. Hacks targeted at connected vehicles have also managed to clone keys to Toyota, Hyundai, and Kia cars, take control remotely over Mercedes-Benz vehicles, and gain access to Nissan’s in-car systems via insecure APIs.
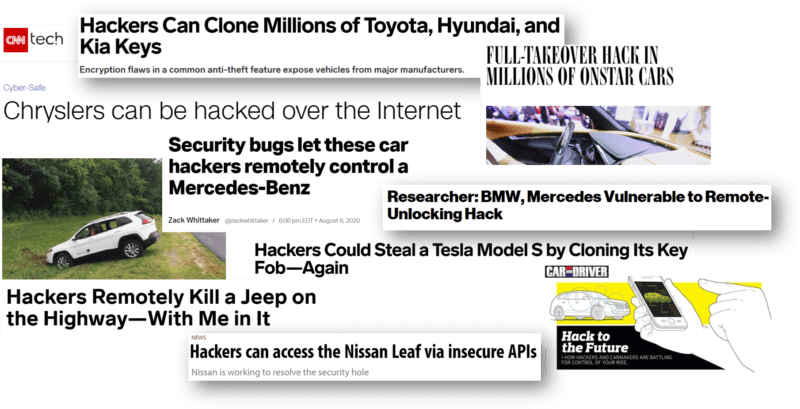
Notably, many of these hacks were executed by security researchers (versus malicious hackers) who are actually working to identify vulnerabilities and point them out to manufacturers. However, they’ve proven that these hacks are not only possible, but also very practical and feasible for malicious parties to execute — often with very modest resources, as many of the hacks were run with inexpensive equipment.
Additionally, most of the security exploits we’ve seen to date were executed remotely, meaning that the hackers have not needed to be inside of the vehicle or even near it. This situation makes it impossible for vehicle owners to defend against these attacks, putting the responsibility of protection completely in the hands of vehicle manufacturers.
Faced with this responsibility, vehicle manufacturers now have the imperative to identify and fix vulnerabilities quickly. In response, many have launched bug bounty programs that offer rewards for white hat hackers who find vulnerabilities and share them with the manufacturer.
Why Securing Vehicles is Hard
The security weaknesses that have plagued the first generation of connected vehicles are not due to negligence. Rather, they’ve surfaced because securing connected vehicles is particularly challenging, even in comparison to securing other IoT devices. Some of these challenges are inherent to automotive IoT security, but some are specific to vehicles.
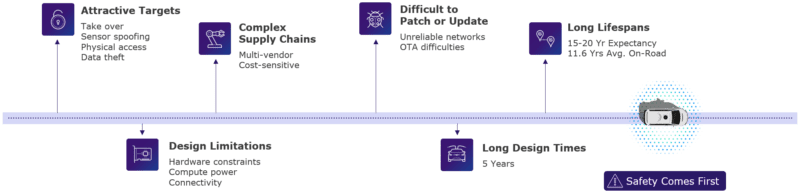
The biggest challenges include:
- Attractive Targets: Connected vehicles have proven particularly attractive targets for hackers, in large part thanks to a long-held desire to tinker with cars. Additionally, a variety of options exist for targeting these cars, including taking over vehicles remotely, sensor spoofing, gaining physical access and stealing data.
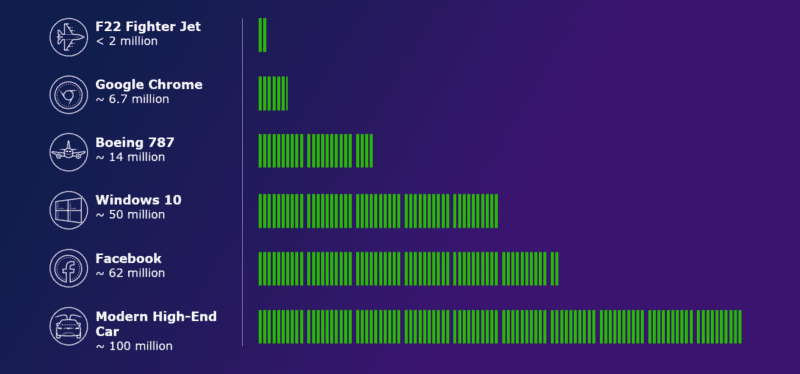
- Complexity: Vehicles have highly complex supply chains that include multiple vendors ranging from equipment manufacturers to tech startups. Each vehicle has roughly 1,800 components and about 150 electronic control units (ECUs). That’s essentially 150 different computers inside of every car, each of which comes from different suppliers and is incredibly complex on its own. Additionally, many security vulnerabilities exist in the boundaries between these components, as there are gray areas that don’t fall entirely into the domain of one unit or another. Beyond the sheer number of components, the modern connected vehicle runs on about 100 million lines of code. That’s twice the amount of a Windows 10 laptop and 50x the amount of an F22 fighter jet, and McKinsey estimates that number will triple to reach 300 million by 2030. These ever-increasing millions of lines of code require their own set of security protocols and only add to the already high complexity of vehicles.
- Design Limitations: Hardware constraints, computer power, and overall connectivity present design limitations for manufacturers when it comes to embedding automotive IoT security in connected vehicles. For example, all vehicles use a Controller Area Network (CAN bus) to allow all the devices within the vehicle to communicate with one another and work together to power the car. This system was designed in 1983, meaning it predates the internet and, with it, modern security protocols, such as the ability to authenticate devices to verify their legitimacy. Although manufacturers are aware of and concerned about this vulnerability, they are bound by regulations in what they can update.
- Automotive Regulations: Several regulations exist that limit areas of information vehicle manufacturers can lockdown for security purposes. For instance, onboard diagnostics (OBD) is a port on the dashboard that provides information about the vehicle (e.g. engine health) and has been mandated to be in every vehicle since 1996. Part of that mandate is a restriction against encoding, encrypting, or obfuscating the information on the CAN bus so that anyone can read those codes. Additionally, many states in the US have regulations around the “right to repair,” or the idea that anyone has the right to fix cars (dealers, vehicle owners, third party auto shops, etc.), which means that anyone needs to be able to access certain vehicle information and auto parts. Ultimately, these regulations protect the idea that anyone can do what they want with their vehicle and require open access to vehicle components that make them vulnerable security targets.
- Patching and Updating Difficulties: Even in cases where manufacturers identify vulnerabilities and can legally make security updates to fix them, unreliable networks and difficulty delivering over-the-air (OTA) updates as vehicles frequently go on and offline make it extremely challenging for manufacturers to deliver these patch updates.
- Long Design Times: Vehicles typically take about five years to design, which presents manufacturers with a long stretch of time in which technology changes rapidly. This timing makes it difficult to account for advances in technology that can help improve security and that might create new areas of vulnerability to hacking.
- Long Lifespans: Vehicles have a 15-20 year life expectancy, spending an average of 11.6 years on the road. Technology will change tremendously during that time, and if manufacturers can’t reliably deliver patches and updates to connected vehicles, any protection they do have when they’re first released will quickly become out of date.
The Path to Securing Connected Vehicles
Clearly, the risks of connected vehicles are high and the challenges around mitigating these risks through stronger security are very real. However, the promise of connected vehicles and the momentum around innovation in the market are too large to ignore. Connected vehicles are not only here to stay, but they’ll also continue to become more complex, and this reality requires us to solve the security challenges that exist no matter how difficult they might be. So what does the path forward look like?
Security Practices
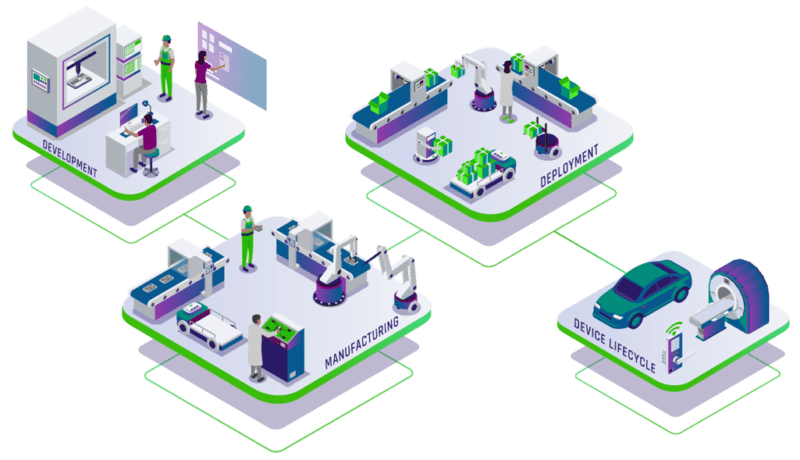
The path forward for automotive iot security and securing connected vehicles starts with recognizing that these vehicles have essentially become driving data centers. A lot of the characteristics of connected cars mirror what we see in modern data centers, from internal subnets of ECUs and domain control units (DCUs) to application ecosystems and external connections back to the manufacturer or street-level infrastructure like traffic lights.
This recognition leads us to introduce several security practices that enterprises commonly use in modern data centers, such as:
- Defense in Depth: Establish defensive mechanisms layered to protect sensitive data and integrity. Essentially, this means not putting all your eggs in one basket so that if one component fails, there are other ways the system can defend against an attack.
- Fail Safely (and Securely): Take responsibility for security by designing individual systems to fail without compromising the safety or security of the entire vehicle.
- Zero Trust/Least Privilege: Embrace the approach of “never trust/always verify” when providing access to and communication with other machines, and reduce privileged access for any points of connection to the minimal amount required to work. One way to accomplish this is by requiring authentication of updates and communications through elements like code signing, digital certificates, and cryptographic keys to confirm the source is legitimate. This prevents instances in which ECUs automatically install firmware updates without checking the source, which has happened in previous hacks.
- Separation of Duties: Minimize risk impact with the segmentation of privileges and access across humans and machines. For example, there’s no reason why the brakes and the radio need to talk. The two should be entirely separated so that if something happens to one element it doesn’t compromise the other.
- Update Capabilities: Ensure all software and firmware can be updated to allow for security patches to be delivered, particularly via OTA updates, as vulnerabilities get identified throughout the vehicle’s lifespan.
While these are new practices for connected vehicles, they all rely on already existing technologies and practices, like OTA updates, data encryption, digital certificates and hardware key storage.
Where PKI Fits In
“IoT solutions often have no security, and from a cryptographic perspective, they often share the same keys or default passwords… Certificates are powerful trust anchors and are a natural fit for the IoT.” – Gartner Research
The security practices for connected vehicles require a multi-faceted approach, making it a perfect fit for public key infrastructure (PKI), which has been foundational to internet security for decades and has most recently proven an ideal solution for securing the IoT.
In fact, we’ve already even seen the value that PKI can bring to securing connected vehicles. In 2016, researchers compromised a Tesla Model S from 12 miles away using a malicious wifi hotspot and a series of vectors. Eventually, they replaced the CAN bus gateway with their own software. Tesla responded quickly to patch the vulnerability and announced that firmware updates moving forward would all be signed and verified at the vehicle before running. This is just one example of how PKI practices, whether that’s certificates to authenticate connected components or code signing for OTA updates, have proven to be a useful and practical way to embed stronger identity and security practices into connected vehicles.
At the simplest level, having Roots of Trust is an important starting point for introducing PKI to connected vehicles. This setup creates a quick way to provide a seal of approval to communications going on in and around connected vehicles, such as authenticating digital identities and ensuring firmware is secure because it’s been signed by a Root of Trust.
Overall, this authentication can come into play in several different communication scenarios for connected vehicles:
- Vehicle to Manufacturer: Protect vehicle data, infotainment systems and onboard vehicle assistance by allowing manufacturers to verify that communications are indeed coming from one of their vehicles through certificate authentication.
- Manufacturer to Vehicle: Secure firmware updates, new features and content and vehicle instructions by setting up the vehicle systems so that they will only trust and accept updates that are signed from specific Roots of Trust tied to the manufacturer. (Note: This type of verification is how all Apple and Windows updates work today.)
- Crash Avoidance (V2X): Authenticate vehicle-to-infrastructure (V2I) and vehicle-to-vehicle (V2V) communications using certificates signed by designated Roots of Trust to prevent hackers from sharing inaccurate telemetry information (e.g. I’m a car, heading in this direction, at this speed) that can lead to crashes.
- Inter-ECU Communications: Protect the authenticity and integrity of inter-ECU communications to ensure that the messages transmitted on a vehicle’s CAN bus (which is currently unauthenticated due to regulations) come from a legitimate component inside the vehicle and not third party who gained access to that component.
Importantly, many of these use cases and security practices are already here. For example, V2X communications are present in a handful of higher-end vehicles today, and while it’s not widely used yet, it bears a lot of promise for coordinating traffic through bi-directional communications between vehicles (V2V) and infrastructure like smart traffic lights and automated tolls (V2I). These communications will become widespread in the near future and will have a direct impact on passenger safety, making security of utmost importance. On a positive note, we’ve seen manufacturers putting in significant effort to secure these communications and ensure a level of anonymity around the data, such as vehicle occupants and their destinations.
Ongoing Challenges
PKI for IoT offers enormous potential to improve the security challenges around connected vehicles, but it also creates a new set of challenges. That’s because security does not simply begin and end with the installation of a key or certificate in the connected vehicle at the time of manufacturing.
Lessons from enterprise PKI tell us that cryptographic keys are not set and forget. In fact, they don’t age well, as nothing in security is static. Consider the following chart, which looks at a combination of hash algorithms and asymmetric cryptographic algorithms, both of which are commonly used in PKI.
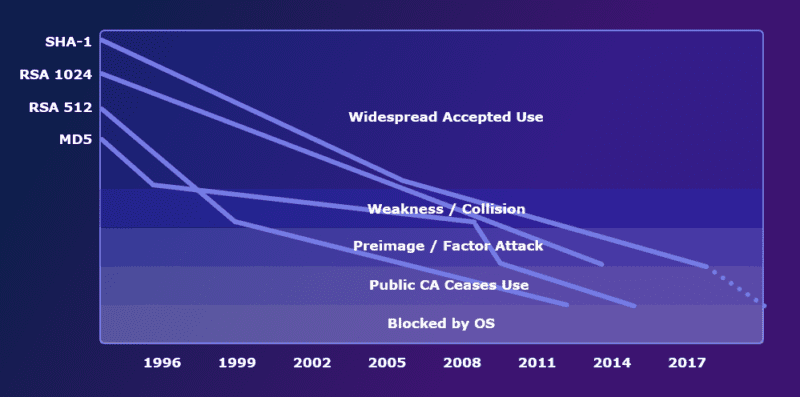
A natural progression occurs overtime in which these algorithms are no longer accepted, either due to a mathematical breakthrough or a computing breakthrough (or a combination of both) that renders the size of the key does not secure enough. For example, 10 years ago it was perfectly acceptable to use RSA-512 and an MD5 hash, but today any operating system that’s up to date will not accept anything signed by algorithms of that type or size.
As a result, any system that will be in the field for a long period of time (as vehicles are), must be built with crypto-agility in mind to enable updates to any keys, certificates, and even Roots of Trust as algorithmic standards evolve. Guaranteeing this ability to update is difficult, but it’s still a requirement because without it vehicles will have to authenticate back to sensitive, internal systems that will be left exposed to risk due to weak cryptography.
Some of the biggest challenges in planning for crypto-agility for end-entity certificates and keys as well as Roots of Trust include:
- Hardware Constraints: Certificates and asymmetric keys are ideal, but they won’t fit everywhere, so PKI strategies for connected vehicles need to include a combination of symmetric and asymmetric encryption. Part of this involves making sure manufacturers have systems that can couple asymmetric and certificate-based cryptography with more traditional symmetric cryptographic algorithms.
- Massive Scalability: Manufacturers will need to manage hundreds of millions (if not billions) of keys, certificates, and identities across their fleets to account for everything in and around each vehicle. As a result, massive scalability is critical to ensure keys and certificates get carefully issued, managed and renewed throughout their lifespan.
- Sporadic Connectivity: Protocols and approaches for issuing updates and communicating with vehicles must be able to handle unreliable connections and vehicles that are offline for extended periods of time. For instance, imagine being in the middle of an update as a vehicle goes through a tunnel — the system needs a way to easily recover from that situation. Or consider cases where people don’t drive their cars for months at a time and therefore no communication can happen during that time period.
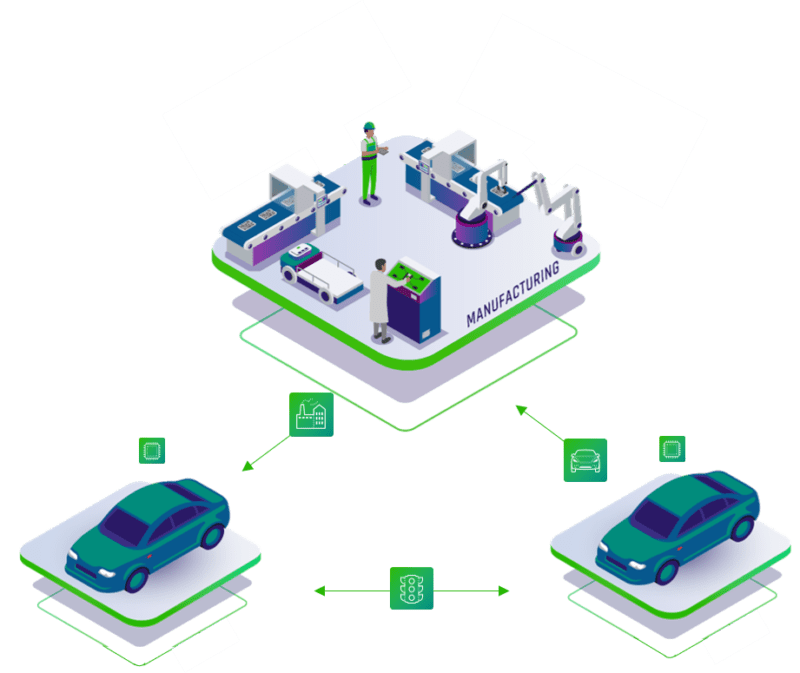
- Key Sharing and Supply Chains: A big challenge in vehicle supply chains is that most Tier 1 suppliers manage cryptographic keys for several vehicle manufacturers. So a manufacturer like GM needs to be able to distribute cryptographic keys to the numerous Tier 1 suppliers that make the components for GM vehicles. But those suppliers have cryptographic keys from a variety of manufacturers because they make components not just for GM, but also manufacturers like Honda and Toyota. This means those suppliers have a very large number of keys that they need to keep separate from one another while also keeping them readily available to install on specific ECUs and firmware for each manufacturer. This situation creates significant and highly unique key management challenges for suppliers.
As manufacturers begin to focus heavily on PKI-based solutions to better secure connected vehicles, these new sets of challenges — and potential ways to solve them — will need to remain top of mind.
Industry Groups and Emerging Regulations
While a good amount of responsibility sits with vehicle manufacturers, the industry at large is also accountable for overall security in the form of regulations.
The good news in all of this is that the automotive community is very good at collaborating and cooperating with one another, even competitors, in places where it’s important and makes sense to do so. They’ve been doing so for decades when it comes to vehicle safety, such as collaborating on safety standards and tests to make all vehicles safer from a crash perspective.
Most recently, industry groups have had numerous discussions about security for connected vehicles, with a lot of great work happening across the board to develop best practices and standards that can span geographies and manufacturers.
Some of the key groups involved in these discussions include:
- SAE (Society of Automotive Engineers)
- ISO (International Standards Organization)
- UNECE (UN Economic Commission for Europe)
- WP.29 (UN Harmonization of Vehicle Regulations)
- IEEE (Institute of Electronics Engineers)
- NIST / AIAG (Automotive Industry Action Groups)
- CAMP (Crash Avoidance Metrics Partners)
Importantly, these groups have already made measurable progress. In 2020, the UN’s World Forum for Harmonization of Vehicle Regulations introduced the first international regulations around vehicle cybersecurity, three of which went into effect in early 2021.
These regulations govern and audit cybersecurity, imposing requirements like the obligation to monitor and report on incidents. Some manufacturers are even getting ahead of this requirement with things like bug bounty programs. They also focus on software updates and update management systems for OTA updates, including making sure that all vehicles have fail-safes in the case that they can’t properly complete an update.
Additional regulations are looking at the supply chain, focusing on attacks where code-signing certificates get stolen or update infrastructure gets breached. When this happens, inauthentic code can get deployed without detection, so regulations in this area will look to provide checks and balances before the code ever gets signed.
In the EU, new regulations like these will be mandatory for all new vehicles produced from July 2024 onwards. When you factor in the long lead time for design, vehicles produced by 2024 are already in design today, so preparing to meet these security regulations starts now.
Key Takeaways for Automotive IoT Security
There’s no getting around it: Securing connected vehicles is extremely challenging, even more so than securing other IoT devices due to unique circumstances that apply only to vehicles, such as the high level of complexity, the massive scale required across suppliers and existing regulations that require more open information.
Fortunately, several solutions do exist to improve the security of connected vehicles, and both manufacturers and industry groups are working hard to put these solutions into place. Many of these solutions center around PKI, borrowing practices from modern enterprise data centers. Some of the most promising solutions include introducing the concept of zero trust and requiring all communications to be authenticated via code signing, digital certificates and cryptographic keys; however, these solutions do create ongoing challenges around crypto-agility and PKI management.
Overall, it’s important to remember that while all of this work to introduce better standards for making the next generation of connected vehicles highly secure is taking place now, it will take time to see real improvements. But the right activities are underway, with industry groups and manufacturers working together to arrive at standards and introduce new solutions to protect these vehicles and their passengers.
Secure Devices. Control Your Future
Vorem ipsum dolor sit amet, consectetur adipiscing elit. Nunc vulputate libero et velit interdum, ac aliquet odio mattis. Class aptent taciti sociosqu ad litora torquent per conubia



