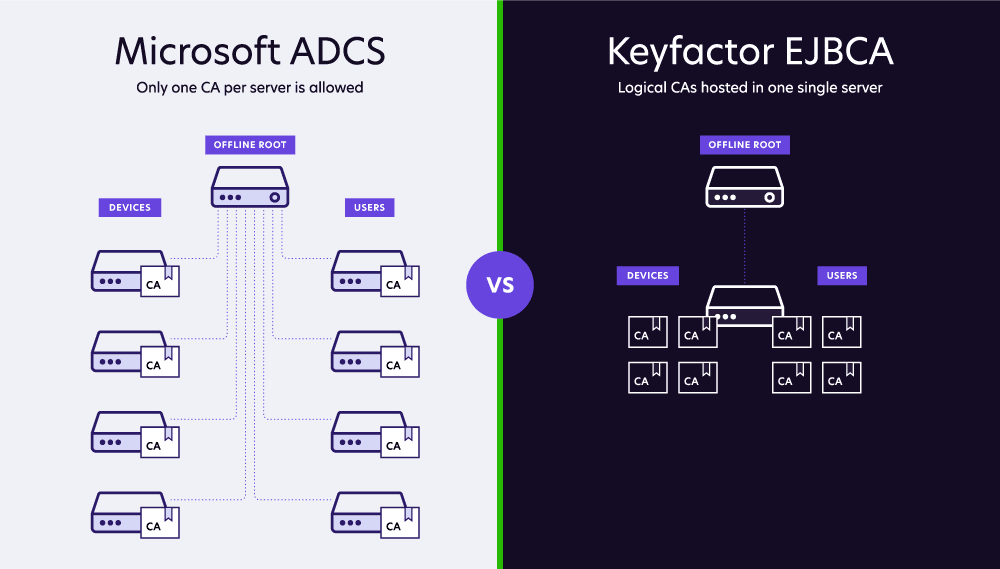
Behind every certificate is a public key infrastructure (PKI). Microsoft Active Directory Certificate Services (ADCS), often referred to as Microsoft CA, has long been the de facto PKI for organizations. It’s well integrated with Microsoft infrastructure and it supports standard use cases.
However, the path to the cloud introduces new challenges. For starters, traditional PKI wasn’t built to handle the volume and velocity of certificate usage today. Not to mention a lack of out-of-the-box integrations and easily overlooked misconfigurations that create serious risks.