The following is an excerpt from Keyfactor’s 2022 Emerging Trends in Cryptography. For all six trends, download your free copy today.
Manual certificate management processes have not kept up with the evolution of IT environments. As enterprises continue to deploy new PKIs for new use cases, PKI governance inevitably becomes siloed.
Enterprises can facilitate the management of their PKI by performing PKI consolidation and migrating several disparate PKIs into a single multi-tenant PKI solution (such as EJBCA). Another trend in this area is using PKI as a Service (PKIaaS).
However, even though PKI consolidation and PKIaaS are gaining popularity and it’s easy to believe either is a one-stop-shop. The reality is that large organizations will continue to have several PKI silos.
For bad and sometimes for good, PKI silos occur everywhere.
Different Providers for Different Needs
Identity management and access control are crucial for a zero-trust security strategy.
PKI is vital to implementing zero trust because it ties assigned permissions to an entity’s identity and provides strong user authentication.
However, the evolution of IT environments means that PKI certificates are applied in many ways and in various environments. Web servers need certificates from a public certificate authority (CA) to prove their identities, while internal identity management is under a private CA.
Digital certificates used in DevOps practices have short lifecycles compared to longer-lived SSL certificates for websites. On-prem and cloud-based infrastructure both have their preferred root CAs.
Meeting the needs of all PKI users requires support for a dizzying number and variety of digital certificates. However, allowing these various PKI applications to become siloed places the organization at risk.
The Need for a Common PKI Platform
As companies pursue their zero-trust security goals, overhauling their PKI governance is a must.
Centralized visibility and control over an organization’s various applications of PKI are crucial to achieving the access control required for regulatory compliance and enterprise cybersecurity.
The diversity of PKI used in the modern enterprise is driving a shift to vendor-agnostic PKI platforms with the ability to monitor and manage digital certificates from different root CAs, in different environments, and with different lifecycles and applications.
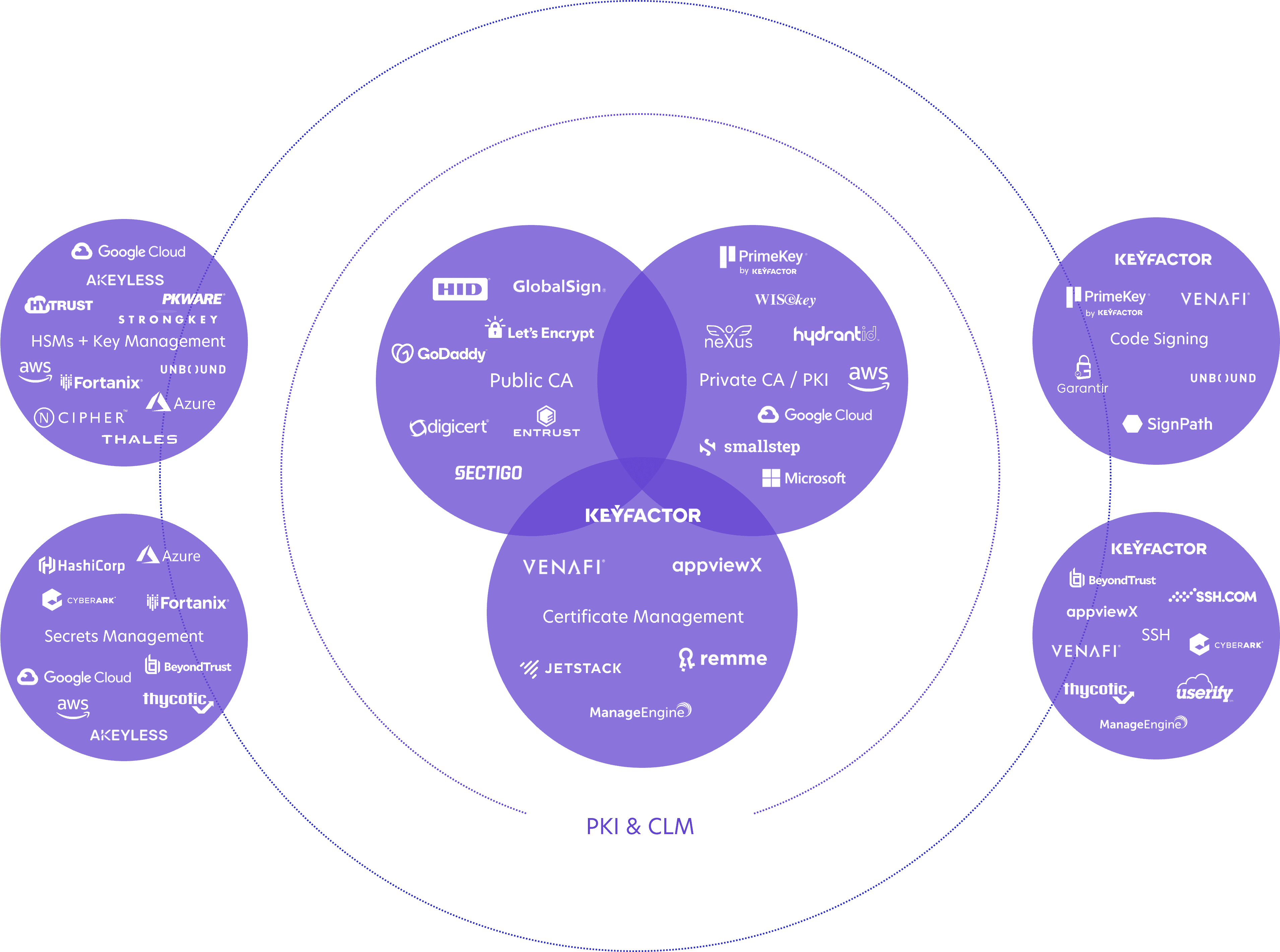
The convergence of machine identity management tools
Now that’s a lot of tools.
Use this graph and take an audit of your existing machine identity management practices (PKI, certificate management, secrets, etc.) to determine where the gaps are.
This will help you find the tools and processes that fit the unique requirements of the various teams within your company.