Everything is going digital. No business, no matter how much they rely on a physical presence (think: landscaping, maintenance), is immune to this shift.
And as COVID-19 accelerated the transformation to digital, many organizations have realized how much they rely on decades-old programs that need updating.
Going forward, the biggest area that requires attention as we continue the shift to digital is security. Specifically, as more digital entities continue to crop up and create data, how can we trust that data?
That was the premise behind our recent discussion with David Mahdi, Vice President and Analyst of Security and Privacy at Gartner. Click here to watch the full webinar, or read on for key takeaways.
How We Got Here: A Paradigm Shift in Digital Development
We’re currently in the midst of a paradigm shift around digital development that will require important changes to how organizations approach security.
This shift centers around the rise of digital applications, including the volume of applications, the velocity at which they’re created and the variety of people creating those applications and the associated data. Everyone from developers to business leaders (thanks to low and no-code interfaces) are now contributing to digital development, and all of these outputs will require security measures.
Overall, the rise of digital development has serious implications for everything from the consumption of cryptographic key material (organizations need to provide quick and easy access to keys in a secure and manageable way) to where all of those applications will live (on-premise vs. hybrid cloud vs. multi-cloud).
Against this backdrop, the idea of a protected network is gone. Now, networks are much more software-defined and much more dynamic. Additionally, identities now play a major role in security access. This means that in the world of hybrid clouds and remote work, organizations can no longer trust any entity on the network.
Today, instead of the network acting as the perimeter, identity is the new perimeter. We’ve seen the importance of this through social engineering attacks, like phishing, that use identity as the entry point. Previously, organizations would operate under the assumption that if someone had access to the application, they had access to the data. But we can’t rely on that approach anymore. We’re now in a zero trust world in which access is more fluid and we have to understand who and what is accessing data. This requires mutual authentication in which the data authenticates the user and vice versa.
Focusing on What Matters: Data and Identities
The shift to digital, and particularly the shift to the cloud, requires a new approach to security and focuses attention on what matters most going forward: Data and identities. Importantly, identities cover both human identities and machine identities — the latter of which will only continue to explode in the enterprise and require scalable, consistent security measures regardless of how innocuous they might seem.
Ultimately, this situation creates layers of dependency, because you can’t have a digital business without digital trust. In turn, achieving digital trust requires an understanding of digital identities, and cryptography is the critical infrastructure that underpins those digital identities.
Consider the following situation: Your business needs to send a contract to a new partner. How do you know that your contact at that company is actually the one on the other side signing that document? To trust in this digital business transaction, you need a way to verify their digital identity, and the most secure way to do so is through cryptography.
To date, access has largely been controlled by passwords, but this approach can be weak for humans and is even more dangerous when you add hard coded passwords for machines into the mix. That’s why going forward, well-managed cryptography should be the lifeblood of every digital business. It largely already is, as everything from online banking to booking flights rely on cryptography.
Key Challenges: Effectively Managing a Widespread PKI Program
Fortunately, PKI and cryptography are now common in a variety of use cases, most notably secure access, device security, user authentication, digital signatures, digital identities and digitalization around hyper-automation and DevOps.
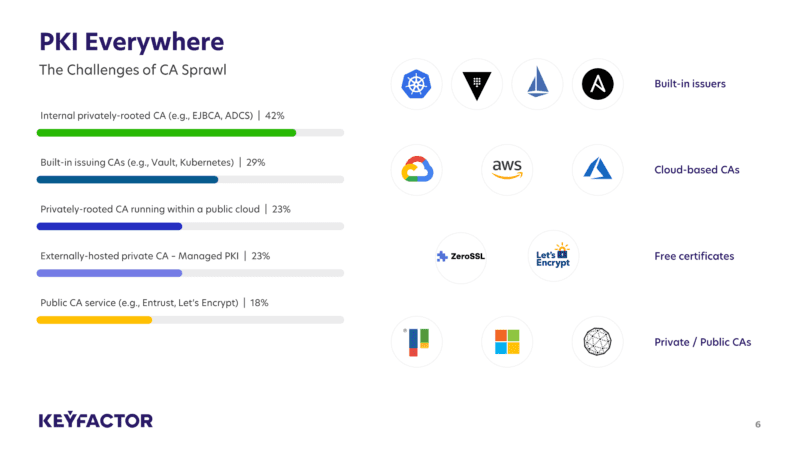
Unfortunately, this situation has created a serious challenge, as the more prevalent PKI and cryptography become, the more difficult they can be to manage. Specifically, reports show that many organizations today use multiple certificate authorities (CAs) to manage various PKI programs, which has led to CA sprawl. In short, this makes it difficult for anyone to get a centralized view of what certificates exist in the organization — visibility that’s needed to properly manage and maintain certificates to avoid them becoming vulnerable throughout their lifecycle.
Most organizations focus on generating cryptographic keys and certificates, which is needed for identity-based authentication, but it’s also important to maintain them by rotating and relocating them as access needs and overall security requirements change. The fact that this lifecycle can get very complex very quickly for both human and machine identities makes having a centralized and automated way to manage the complete certificate lifecycle essential.
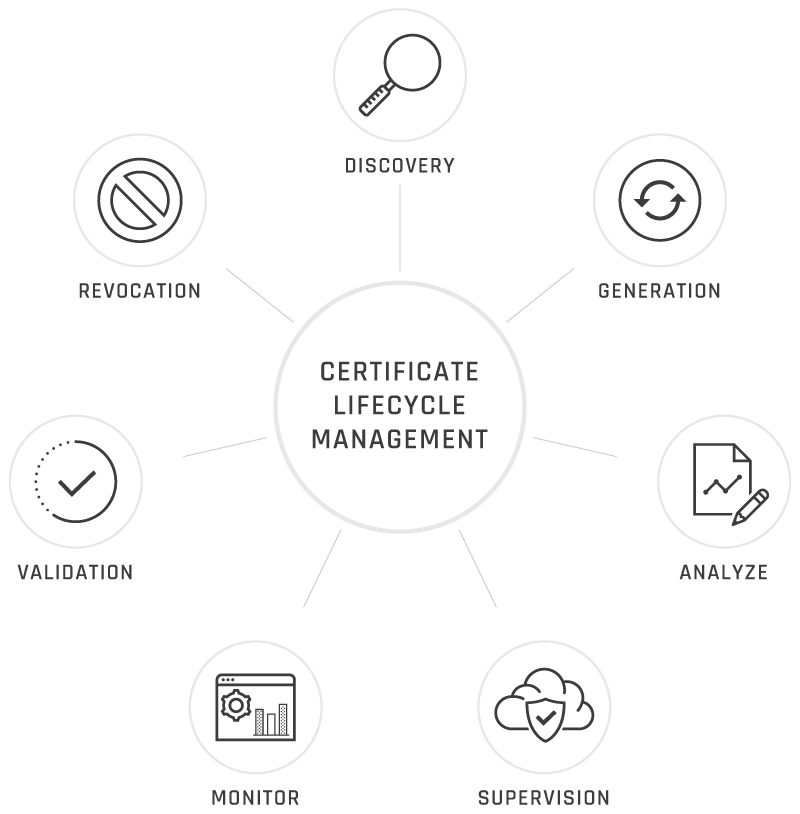
Notably, this challenge will only continue to increase as the number of identities, both human and digital, requiring authentication expand.
Centralizing PKI: Supporting Identity-First Security with Consolidated Management
As identity-first security becomes increasingly important and more and more identities, particularly machine identities, come into play, the only way forward is to centralize PKI programs.
Most organizations today have somewhere between 50-70 solutions to manage security. This creates a lot of silos and means that very few, if any, solutions are fully optimized. While there will never be one single solution to rule them all, the more organizations can consolidate onto a centralized platform, the better the outcomes will be.
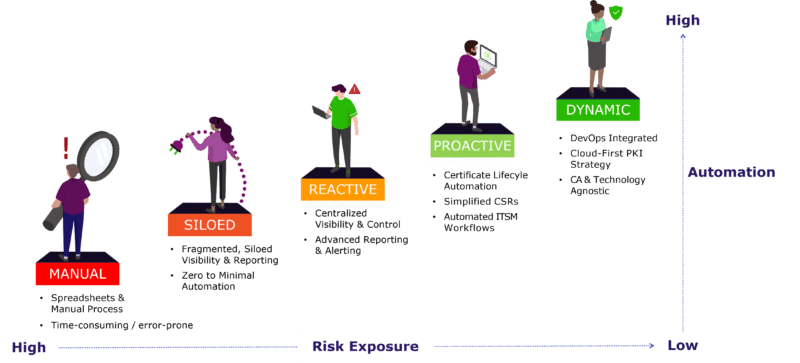
This is where a scalable and automated PKI solution that can support machine identity management comes into play. The best solutions help limit risk exposure by thinking through identity-first security and support scale through automated certificate management for the ever-growing number of identities. We can think of the maturity model to achieving this ideal solution as follows:
Establishing and Maintaining Trust: The Value of People and Processes
Having the right cryptography solutions in place is an important first step, and a big one at that, but it’s not the last step in the shift to digital. Making this shift also requires introducing the right people and processes to the mix.
For example, if your organization establishes a public key infrastructure (PKI) program, you also need to think through how everyone creating systems and applications (which now includes developers and even non-technical teams) can easily get certificates.
If they don’t know they need a certificate or can’t get one easily, then the PKI program can quickly fall apart. They don’t need to know the inner workings of everything, they just need to know what they need and where to get it, similar to if you needed an oil change in your car.
Overall, the responsibility to establish and maintain trust sits with the people in every organization, and enabling people from the security team and beyond to fulfill that responsibility effectively requires processes that make it easy for everyone to participate.
One of the best ways to support PKI programs through people and processes is to introduce a Cryptography Center of Excellence. This can be a group of cryptography experts who set guidelines for the organization and develop processes that make it clear for people from across the business what security solutions they need and where they can get them.
The mission of the Cryptography Center of Excellence should be to:
- Define ownership
- Provide leadership
- Research and gather requirements
- Deliver best practices
- Act as advisors and subject matter experts
- Educate and enable business unit leaders
Ensuring a Secure Future: Top Recommendations from Gartner
As the shift to digital barrels forward, organizations must recognize the importance of identity-first security and the value of PKI programs to properly manage the explosion of those identities in the enterprise. Against this backdrop, Gartner recommends the following best practices for getting started:
- Establish a machine identity management program: Assess the tools and technology you have today to understand how you’re currently managing machine identities and where responsibilities lie within the organization.
- Assign ownership of machine credentials management: Introduce a Cryptography Center of Excellence to centralize management and responsibilities. A big part of this will be thinking through which security and non-IT leaders need to be a part of this group.
- Evaluate the available solutions as the market comes to fruition: As the market continues to mature, take the time to understand the different solutions available to help scale and automate identity management. While you may need different tools for elements like identity management vs. certificate management, the more you can consolidate, the better.
Interested in learning more about what it takes? Click here to watch the full webinar.




