Today we’re pleased to announce the general availability of Keyfactor Signum, a secure signing as a service platform that makes signing code, containers, software, and firmware effortless for application and operations teams, and easy to manage for security.
Code signing is a critical step in the build process to protect the integrity of software and critical infrastructure, but it’s more than just certificates and signatures. It’s about ensuring only the right people and tools have access to sign code. Otherwise, it opens the door to malware propagation, breaches, and software supply chain attacks.
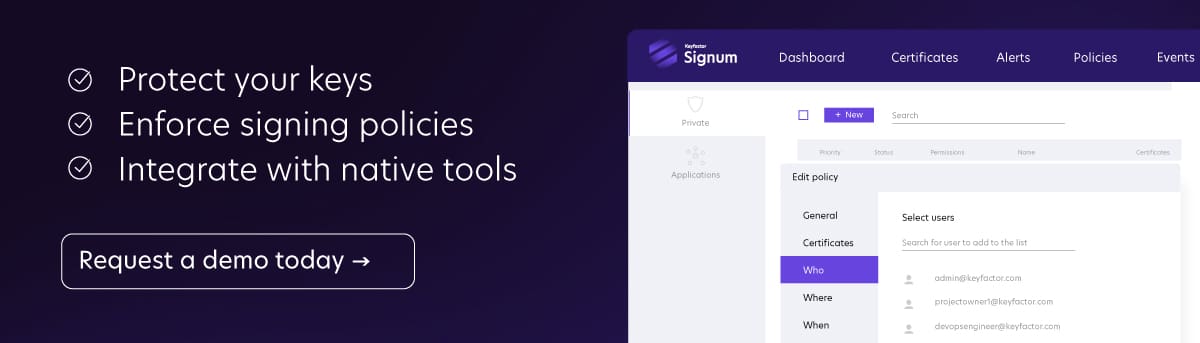
Signum is designed to protect sensitive code signing keys and control who and what has access to them, while also streamlining signing processes by integrating with the platform-native tools that developers already use. It allows security teams to protect the business against key misuse or theft and makes it invisible to IT admins and developers that need to sign code efficiently.
The new rule: trust nothing, sign and verify everything
In a world where nothing is inherently trusted — from the software we deliver to customers to the code and containers that run in our own environments — the need to digitally sign and verify the authenticity of everything has reached a critical point.
In recent years, we’ve seen rapid growth in the use of code signing to prevent malware spread and protect against the increasing threat of software supply chain attacks.
Companies have become increasingly dependent on code signing to assure customers that their software is trusted and safe, to protect the integrity of IT operations by enforcing the signing and verification of scripts, macros, and applications before they can run on internal systems, and to ensure authenticity and prevent tampering of artifacts, binaries, and container images.
The challenge: code signing is a powerful tool — if it's secure
We put a lot of trust in code-signing certificates. After all, they represent the identity of software and the company behind it. The problem is that, if code signing certificates aren’t properly protected, they’re susceptible to theft or misuse.
Attackers take advantage by stealing private keys from trusted companies and using them to sign and distribute malware that appears trusted. In fact, a recent report by VirusTotal found more than 1 million signed malware samples online — 87% used valid certificates to sign code.
If code signing processes aren’t secure, here’s what can happen:
- Sensitive signing keys are often left unprotected on USB drives, build servers, repo readme files, or developer workstations.
- It’s difficult for security teams to know who signed what, when, and where.
- Attackers seek to compromise vulnerable signing keys and steal them to sign malware or sell them on the black market to other cybercriminals.
- They could also breach the signing process and submit malware to be signed as if they’re a developer, without being detected.
- Or worse, developers accidentally embed signing keys in their software or firmware, where they are exposed to the public.
Keyfactor Signum: secure digital signing, without the hassle
Oftentimes, developers have to request keys from a project owner or the security team, which creates bottlenecks and just doesn’t scale in today’s development environments where application teams work from anywhere. Either that or they take insecure shortcuts and keep keys locally on their machines. A recent report by Keyfactor found that 37% of respondents still store keys on build servers, and another 17% say they’re stored on developer workstations.
With Signum, developers can simply sign code using native tools, while the built-in policy engine ensures that only authorized users and machines can access specific keys to sign their code.
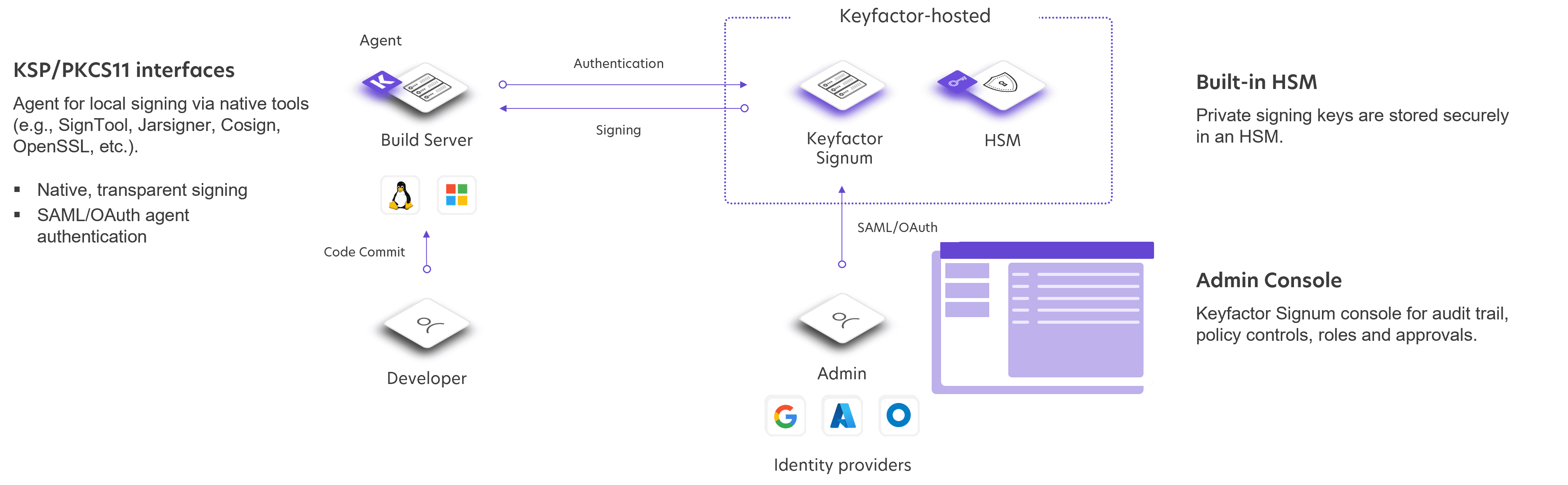
Even during singing, private keys remain locked away in a built-in FIPS 140-2 certified cloud HSM. Lightweight agents are installed on workstations or in an unattended mode on build servers to enable local signing in either automated or manual workflows.
Key features and capabilities:
- Built-in HSM for secure generation and storage of code signing keys.
- Authentication via SAML, OAuth, and other methods to ensure that users and machines are authenticated before signing or accessing the Signum platform.
- Granular policy controls allow security teams to define rules for certificate access and usage based on use cases and security requirements.
- PKCS11 & KSP interfaces integrate directly with signing tools such as SignTool, Jarsigner, Cosign, OpenSSL, Microsoft HLK, and more to enable local signing.
- Event logs provide irrefutable records of key access and usage for easy auditability.
- Centralized dashboard to manage all code signing certificates, policies, approval workflows, reporting, and auditing.
- SaaS platform makes deployment fast and simple, with a built-in HSM and guaranteed SLAs for security and uptime.
Signum vs SignServer: What's the difference?
If you’re familiar with Keyfactor, you may know that we already offer a code and document signing solution — SignServer Enterprise — through our merger with Primekey in 2021. What you may not know is that we acquired Redtrust, a Spanish-based company, back in 2019. It’s the unique technology offered by Redtrust that allowed us to build Keyfactor Signum.
So, why did we build Keyfactor Signum?
The simple answer — now we can offer signing solutions designed to address the different use cases and requirements of our customers.
On the one hand, SignServer is a powerful server-side signing engine, built for high performance and interoperability with a wide range of signing formats and key types. It’s highly configurable and uses client-side hashing to sign code, executables, and documents in large-scale environments.
On the other hand, Signum is a policy-driven signing solution, focused on enforcing specific guardrails around who can sign what code, when, where, and with which keys. Rather than API-based signing, Signum leverages lightweight agents that plug into platform-native signing tools, and signing is performed locally on the build server or workstation, while keys remain secure in the centralized HSM.
Different use cases, security requirements, corporate policies, and workflows require a different approach to code signing. SignServer and Signum offer the flexibility to meet the unique needs of our customers, no matter their use case.
Ready to learn more?
If you want to learn more about our signing solutions and find the right fit for your use case, you can check out our solution page here. If you’re ready to dive deeper and see Signum or SignServer in action, request a demo with our team today.