The increased digital transformation of businesses in response to the coronavirus pandemic brought machine identity management into the center of identity and access management (IAM) discussion. With all these identities to be managed, the situation could easily deteriorate and become chaotic unless you can control it.
A disruptive era
2020 (and 2021 as it seems) are highly disruptive years, impacting societies and businesses. In a battle for existence, organizations accelerated their digital transformation initiatives to adapt to the changing forces brought by the pandemic. The degree and speed of embracing cloud technologies, IoT-connected devices, containers, microservices, and remote working schemes changed, as well, the cybersecurity landscape.
Besides technologies enabling remote access to corporate data and services, businesses are also maintaining a plethora of traditional, on-premises infrastructure and computing models.
This level of diversity in technologies used to support business goals is creating headaches in security teams who are trying to protect a wide range of perimeters – from endpoints to home offices, from RBAC to VPNs, and from state-of-the-art SaaS apps to legacy OT systems. Security teams are becoming overwhelmed trying to figure out how to maintain the same level of security posture across the whole enterprise.
We need to simplify a complex world
Protection of data and apps is of utmost importance for businesses and their customers, employees, and partners. To address the problem of securely accessing these corporate assets, organizations are deploying a great variety of security solutions. These solutions from multiple vendors create disparate controls, with varying implementations, offering a range of protections.
However, this diversity creates more problems that those trying to solve – interoperability, vendor lock-in, compliance, complexity, increased costs. A single platform can rarely satisfy all business use cases and compliance requirements.
Complexity is the enemy of security. Therefore, it is essential to change this chaotic security landscape before it becomes too threatening for business resilience against increased cyber-attacks targeting data and apps. Simplicity will help security teams deliver streamlined security, enabling an enhanced user experience and avoiding costly misconfigurations that lead to data breaches and exposures.
Access security should be transparent, offering a smooth experience across all infrastructures. Access controls should be an enabler of productivity and not a factor of frustration which employees will seek to circumvent. It is high time for an equivalent to the network “control plane” to determine and apply access security across a wide range of access points.
What is a 'control plane'?
Cloudflare defines that “In networking, a plane is an abstract conception of where certain processes take place.” There are two planes in networking, the control plane and the data plane.
“The control plane is the part of a network that controls how data packets are forwarded — meaning how data is sent from one place to another. In contrast to the control plane, which determines how packets should be forwarded, the data plane actually forwards the packets,” explains Cloudflare.
A good analogy to understand how control planes and data planes cooperate is the traffic lights that allow city traffic management. The control plane is the traffic lights, while the data plane is the cars controlled by the traffic lights.
Machine identity is the new battlefield
Digital identities (human and machine) are already in use in businesses to define who is accessing what and how. Employees and customers are already familiar with the concept of providing an identity to access services and data. In a business environment where all other perimeter defenses have become obsolete, identity is emerging as the new perimeter, the new battlefield to defend.
Therefore, it is essential to adopt policies and practices that can enable a flexible, risk-sensitive, adaptive access security based on protecting these identities. Identities can be tailored to various business needs and use cases.
Still, it needs to be addressed with a zero-trust mentality to eliminate all past vulnerabilities – insecure passwords and password fatigue and “blind” trust. Digital identities are the control plane businesses should invest in, but they also need to take a well-planned approach.
How to defend the identity battlefield
The first step of your preparation should be to invest in technologies and solutions that are identity-centric and allow security teams to make security decisions based on the value of the identity. Identity-centric solutions should protect not only your on-premises services but increasingly your cloud-based SaaS applications. Providing practical and robust identity management in the cloud is the biggest benefit of your control plane. This will help your business to protect sensitive data in the cloud while maintaining compliance with security and privacy regulations and standards.
The second step is to create a single “source of trust” — a single and accurate repository for all your identities. Eliminating ambiguities in your identity control plane makes your security solution reliable and authoritative.
On the other hand, fragmented approaches and sources add unnecessary complexity and increase the level of risk in your access decisions. It is also a best practice to integrate the identity and access solution into your business processes to align security with business goals and address the overall business risk.
Keyfactor is your machine identity control plane
Once the single source of identity trust is established, you will need to put your control plane into operation. There is no better way to start by onboarding your remote workers and your SaaS applications to help your business adapt to this new norm. It is equally important to protect your on-premises critical applications and services and ensure that only authorized individuals access them.
This is where Keyfactor can help. With Keyfactor, you can establish a PKI and certificate automation control plane that provides policy enforcement for every machine identity.
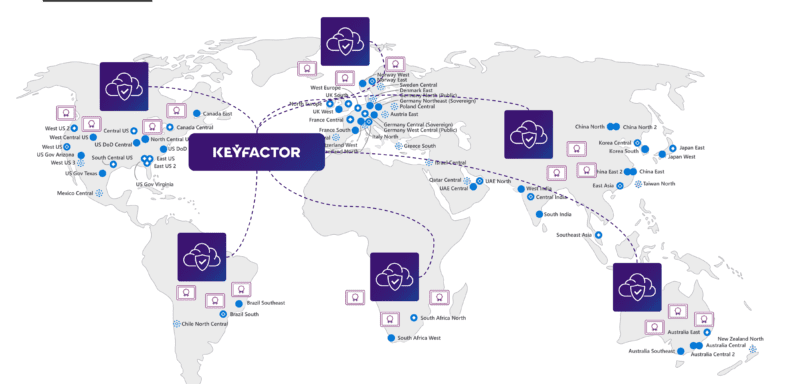
With an established certificate lifecycle automation and integration framework, Keyfactor can control all digital certificates throughout your global endpoints. Whether you need to issue certificates on-demand to authenticate cloud workloads, containers, microservices, as well as ingress and mTLS in service mesh architectures, Keyfactor provides a repeatable and reusable certificate trust plane across all machine identities.
Keyfactor can be your companion in your control plane journey. Ask our experts to help you navigate in safe waters.




