“What makes a digital certificate secure?”
When I ask this question to our customers, the answer I get back most of the time is something like “it has a secure algorithm” or “it is issued from a certificate authority (CA) and not self-signed.”
Although these answers are both correct, there are so many more factors that make a PKI trustworthy. PKI is not only about the ability to issue a certificate from a CA, but also the overall plan and process of how a CA is secured and managed.
Let’s dive in a little more.
The C-Suite Misconception of PKI
Many CIOs and CISOs that I speak with have the misconception that just because their organization has a PKI that they are inherently secure, which is often not true. I commonly find that the security teams implementing the PKI are focused purely on giving their organization the ability to issue certificates from a technical perspective.
This leads to the common scenario of someone clicks “Next… Next… Next… “ during the install of the CA, and proclaiming “I got it working!”. While this may accomplish the goal of having a PKI, it does not meet the long-term security goals of the company.
Building a Multi-layered PKI
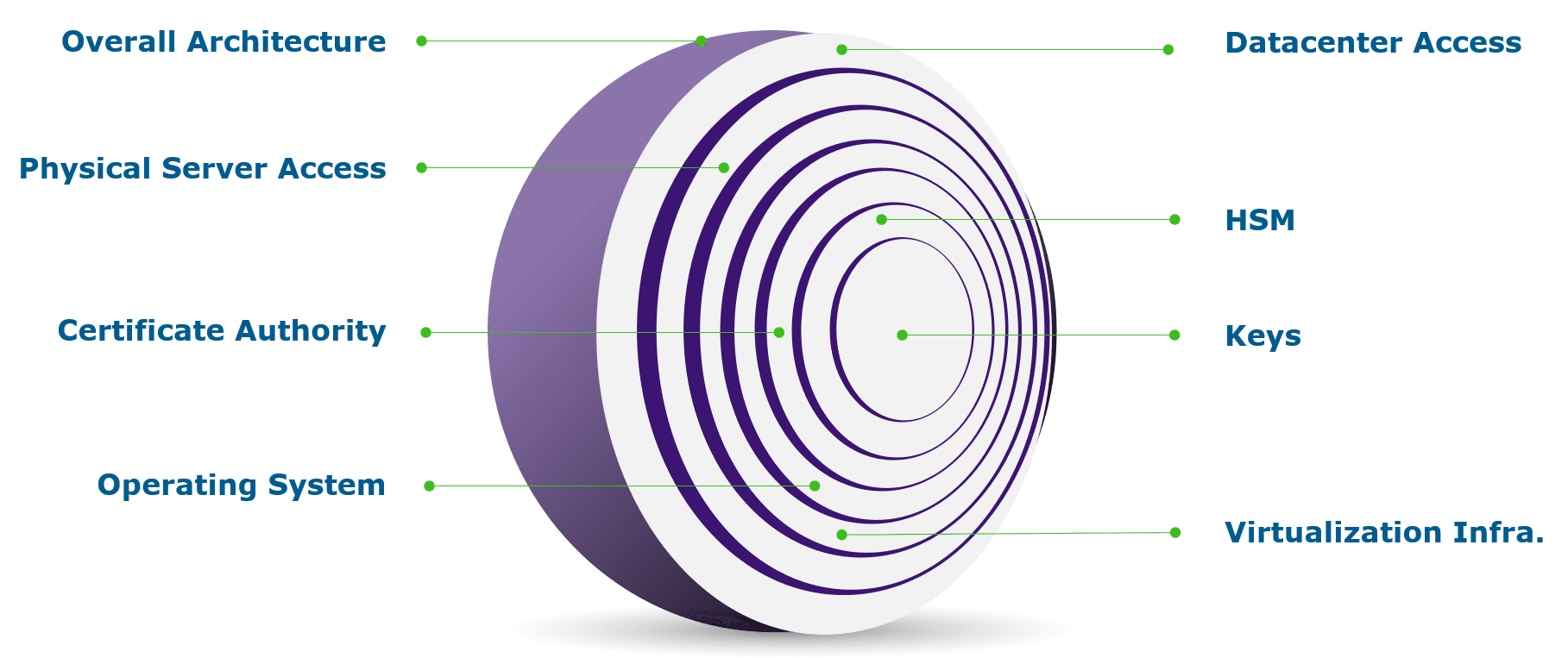
A good PKI implementation should be multi-layered and go beyond the narrow focus of issuing certificates. The implementation should be a well-thought-out, planned execution that considers all aspects of securing the PKI. This should consider securing the keys from both external and internal threats.
Who has access to the virtualization infrastructure and disks? Who has physical access to the datacenter? Who has access to the backups? All of these are potential points of compromise.
Components of Multi-layered PKI
Let’s unravel the PKI onion. As an executive, how do you know if your organization’s PKI is trustworthy? Below is a quick quiz that can identify some issues in the often overlooked areas of PKI security and help you assess the trustworthiness of your PKI infrastructure.
If you answer these questions honestly and find yourself answering “no” or “I don’t know” to many of the questions, it is time to re-think your PKI strategy.
| Layer | Questions to Ask |
| Overall Architecture |
|
| Datacenter Access |
|
| Physical Server Access |
|
| Virtualization Infrastructure |
|
| Operating System |
|
| Certificate Authority |
|
| HSM |
|
| Keys |
|
Moving Forward
Can an untrusted PKI be made trustworthy again? Unfortunately, the answer is typically no. Once a PKI has been deployed with poor key management practices, it is usually better to just start over with a new strategy and fresh implementation. This is due to the fact that you do not know if your keys have already been compromised.
There is the potential risk that an insecure copy of one of your critical certificates has already been downloaded or stored in an insecure location which could be compromised later. For this reason, it is probably best to just re-design properly and start over.
Don’t try to go down this path alone. If you discover that it may be time to update your PKI, Keyfactor has a team of PKI experts that are ready to help. We can deploy the best practices PKIaaS infrastructure that will provide the level of trust that you need to know that your data and applications are secured and reliable.




