If you live in the world of public key infrastructure (PKI), you’re a rare breed.
Despite its importance in IAM strategy (namely, securing machine-to-machine connections with unique identities), PKI is often misunderstood. A rare few companies have in-house expertise, but for most, it’s more of a “hot potato” that gets passed around to anyone brave enough to take it on. So, where do these “PKI admins” turn for advice?
You guessed it, the Internet – and it turns out Reddit is a hotspot for PKI-related questions. In this blog, we search the depths of Reddit to uncover a few “stories from the trenches” and give some practical advice on 3 common mistakes we see in PKI and certificate management, and how to avoid them.
Problem #1: Outdated, Misconfigured PKI
PKI deployments are long-lived, 15-20 years typically. The problem is that PKI environments set up years ago just weren’t designed with modern IT infrastructure in mind.
Active Directory Certificate Services (aka Microsoft CA) may have been an easy choice then, but the shift to multi-OS, multi-cloud environments demands more from PKI than just auto-enrollment. Microsoft CA can be stretched, but only so far before it becomes an operational roadblock.
Another problem is that PKI deployments usually sit around long after their creator has moved on to another company or into a new role within the business. Even if it’s designed and architected properly, it’s all too easy to let configurations drift out of policy. Once that happens, there’s no easy way to reverse course.
“PKI is one of those things that is easy to do, but just as easy to do wrong. And if you can’t figure out it’s wrong early, it’s a real pain in the a%& to fix”
“Yup, our CA got nuked a few weeks ago and are in the process of repairing it. Fun times.”
Lesson Learned: Point is, running PKI is a marathon, not a sprint. It’s also more than just CAs and certificates. Consider the needs of your different teams and applications and determine the capabilities, process, and people you’ll need to support that.
Advancements in industry-standard protocols (e.g. ACME, EST and CMP), CA scalability, and SaaS-based PKI alternatives can help resolve many of the challenges of setting up a proper PKI and maintaining it as people come and go through the business.
Problem #2: Limited Visibility of Certificates
Getting your PKI straightened away is one thing, but how do you keep track of all those certificates you’ve issued? How about certificates issued by other teams in the organization?
Some combination of Excel spreadsheets, calendar reminders, or PowerShell scripts is a common approach, but there’s always that one certificate that gets away from you. Where is it installed? Who owns it? Are they still with the company?
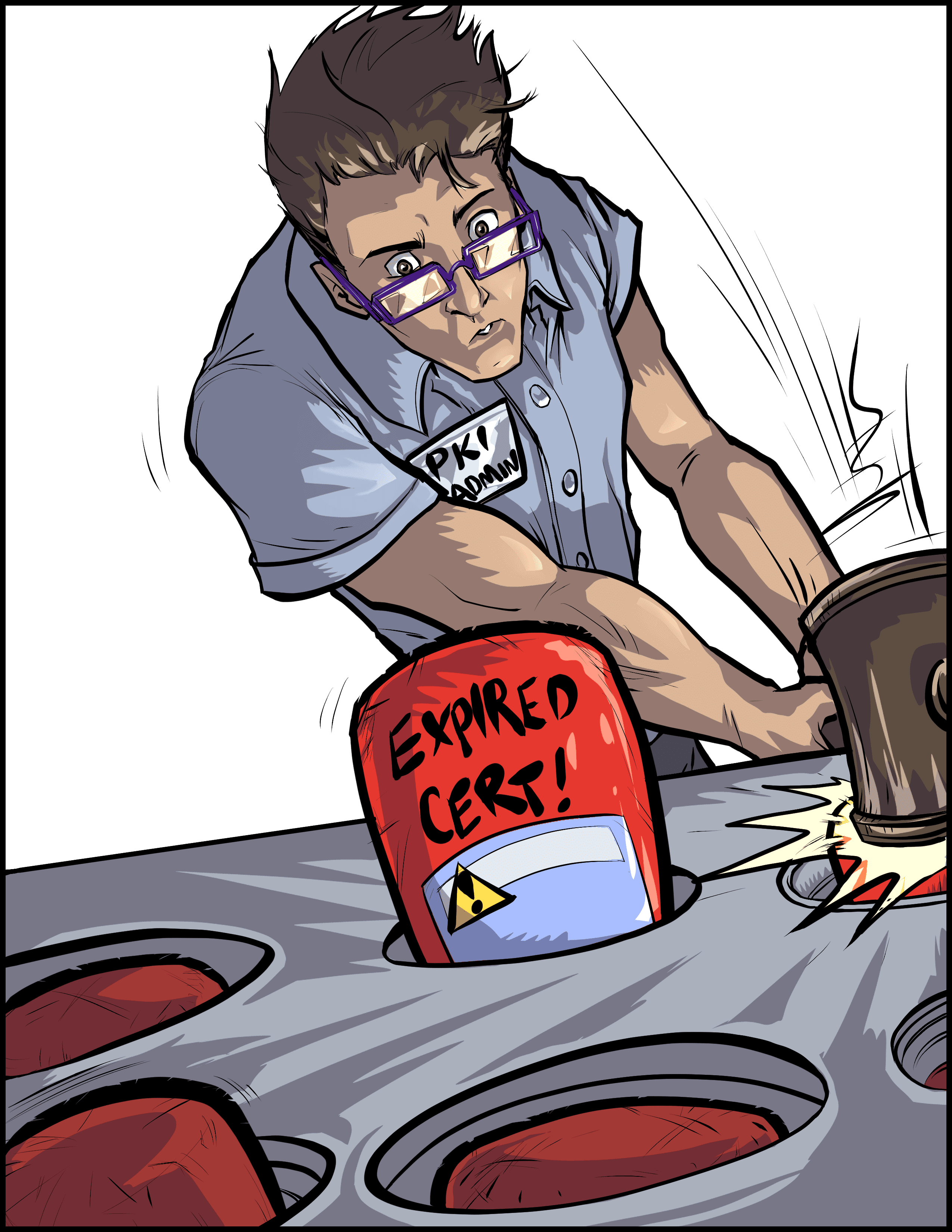
It becomes a never-ending game of “whack-a-mole.” No matter how many monitoring tools or rows and columns you draft up, expired certificates unexpectedly pop out of the woodwork. Just when you thought you had it under control, it happens again. An outage hits your production environment. Another untracked certificate expired, and it’s your job to chase it down and fix it.
“G@&%$!# CERTIFICATES EXPIRING AAAAAAAARRRRGGGHHH Seriously, why can’t they just never expire. Every g%#$@#! thing seems to need a thousand of them and they always expire before you can catch them.”
Lesson Learned: It’s not the certificates you know about that cause the headaches. It’s that one certificate you didn’t see. You know…that one cert that one admin installed on that one load balancer last year. You know where it is, right?
To get a full and accurate inventory, you need full visibility into (1) CA databases, (2) SSL/TLS endpoints on the network, and (3) key and certificate stores. If you don’t have visibility from the CA down to the cert store, it’s really difficult to detect any unexpected changes.
Problem #3: Manual Certificate-Related Processes
Even if you’ve got PKI experts on staff, your certificate users aren’t experts. They make mistakes and ignore policies. Engineers and developers are busy too, but their focus is on delivering new features and keeping things running, not handling certificates.
People are, for the most part, utterly terrible at anything they only have to do once in a blue moon, like installing a certificate. They may install it once, swear they’ve got it figured out, maybe even document it, then move on.
A year goes by and suddenly they forget how they did it. So when they get notified about a soon-to-expire certificate, they renew and install it onto a server. Done, right? A few days later, there’s another outage. Turns out they forgot to bind it to the right application.
“I would never want to work with certs enough to be called the “certs guy.” Every year when I have to renew a few, I find myself wanting to grab a fork and poke my eyes out.”
“I LOVE renewing certificates. Said no one ever.”
Lesson Learned: If you’re responsible for PKI, keeping up with certificate requests can feel impossible. On the other end, certificate users are often frustrated with manual processes to renew and install certs on their machines or applications.
Put the fork down. Using automation tools, including new standard protocols, open-source tools, and certificate lifecycle automation solutions, can cut down on hours of manual certificate-related tasks and reduce the risk of human error that comes with it.
Get the Full Story
If you’re experiencing one or more of these “PKI problems,” you’re not alone. That’s why we compiled an eBook on “7 Reasons Teams Fail in PKI and Certificate Management.”
Inside, we shed light on the ups and downs of a day in the life of a “PKI admin” and share lessons from those that have taken to Reddit to vent about all their frustrations. We hope you’ll draw as much enjoyment as you do insight from their words.