Organizations have thousands, or even tens of thousands, of certificates. If you handle certificates in your company, this comes as no surprise. It’s very complex and difficult to keep track of these certificates, much less maintain control over how they’re issued or used.
However, it is probably not the certificates that show up on your spreadsheet that cause problems. More likely, the certificate causing your next outage is the one you do not know about.
[Watch “How to Take Control of your SSL/TLS Certificate Inventory“]
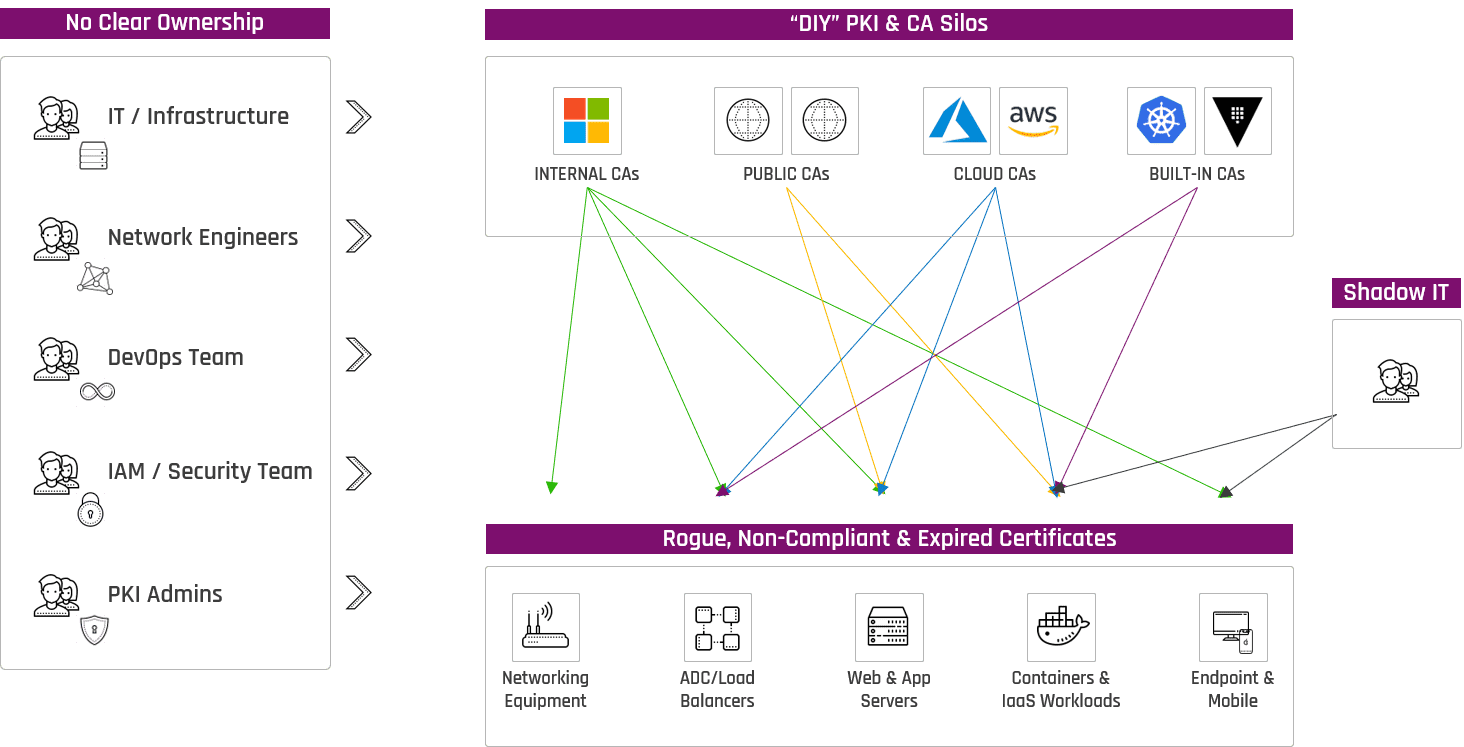
You don’t necessarily know where all the certificates are in your environment, since people in your organization might request certificates without you even knowing. While organizations give their best estimate on how many certificates they have, most of them admit they don’t know the exact number.
Without visibility though, there’s little chance of preventing the next outage caused by an expired certificate.
Certificate Discovery and Management
There are many different evaluation factors to consider before deploying certificates to your network. Many existing market solutions just aren’t successful in effectively managing the large number of certificates in organizations today.
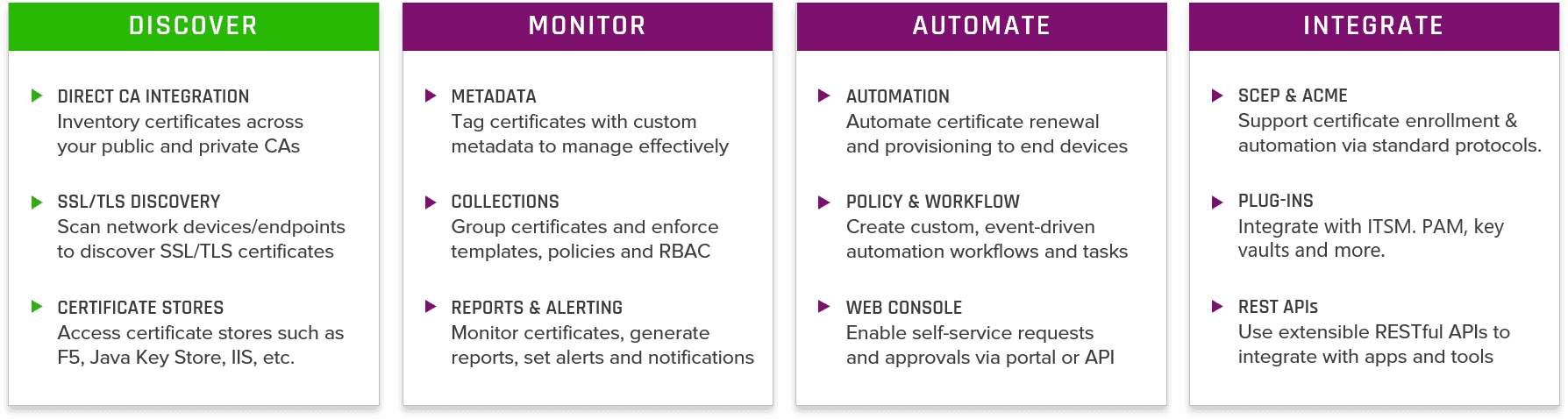
When we break down the core steps to a solution, discovery is number one, then monitoring and automation beyond that, then how to integrate certificate deployment with different toolsets and applications.
Certificate Discovery
Effective certificate discovery can essentially be broken out into three different capabilities:
- Direct CA Integration
- SSL/TLS Discovery
- Certificate Stores
Direct CA Integration
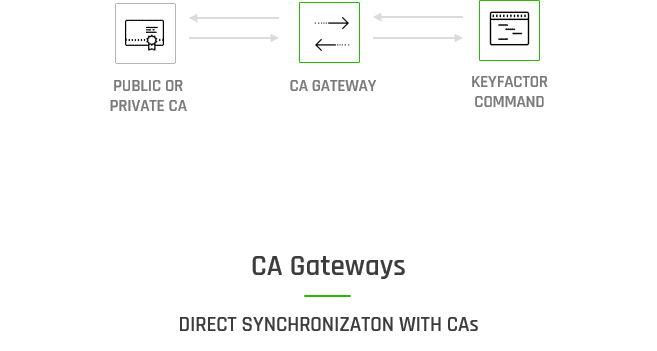
The first certificate discovery method involves integrating with not just your on-premise certificate authorities, but also third-party certificate authorities. This will allow your to bring all of your inventory into one place right from the source.
Direct synchronization with CAs allows you to request new certificates, revoke them, renew them, and renew them prior to expiration.
SSL/TLS Discovery
Having a direct integration to your CAs is a great first start, but it won’t give you visibility into where those certificates are located on your network. Furthermore, developers and admins will often go out and request certificates from CAs that you might not be managing.
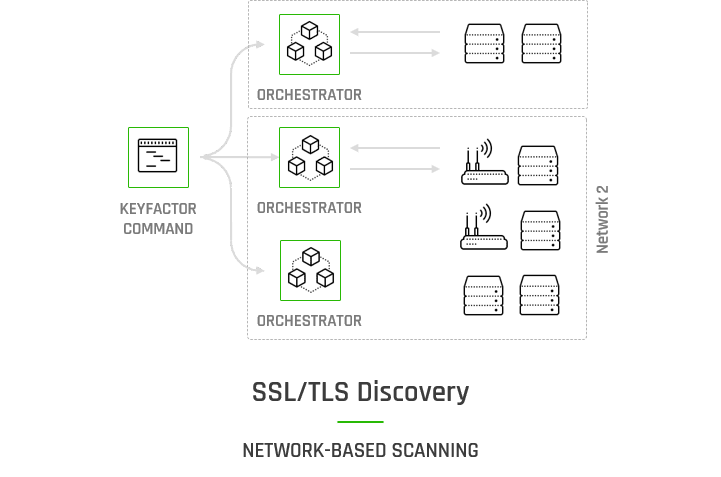
SSL/TLS discovery capabilities allow you to map certificates to your network topography and schedule scans to inventory certificates and ensure that they are still at the endpoints where you expect them to be.
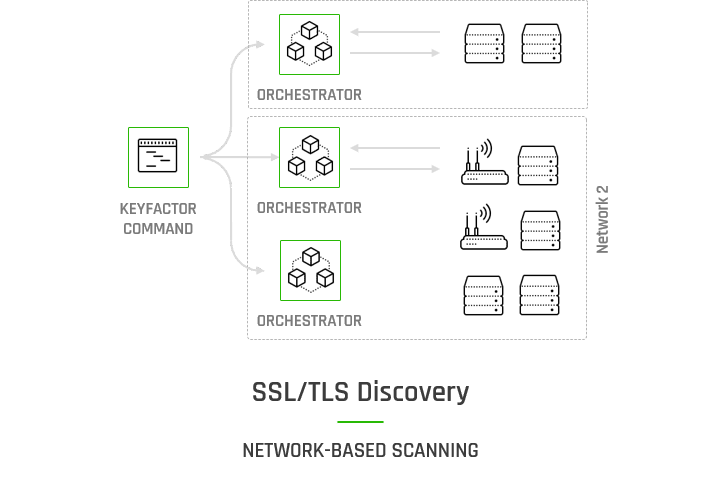
Performance is the number one problem we come across with SSL / TLS discovery. Not only has the volume and velocity of deploying certificates increased, but also the sources of issuance of those certificates has expanded.
Knowing where every certificate is located allows you to quickly and easily replace them in bulk in response to cryptographic changes or a CA compromise, for better crypto-agility. From there you can start doing things like tracking and reporting on those certificates, setting expiration notifications, and automating deployment. It all depends on getting an accurate and up-to-date inventory.
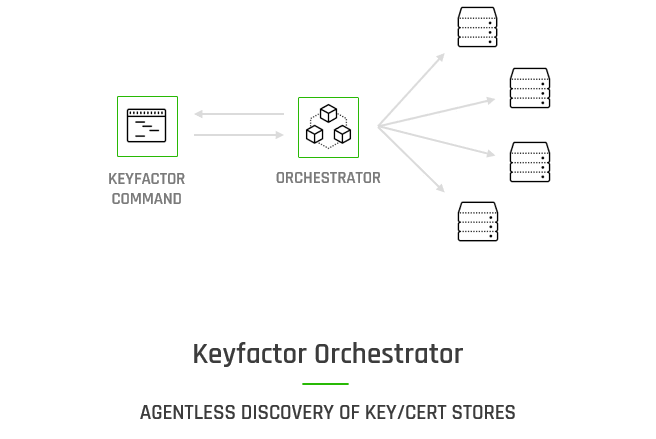
Certificate Stores
And finally, some certificates aren’t even necessarily exposed to a port on the network. They are residing in certificate and key stores, such as Java KeyStores (JKS), F5 devices, IIS servers, or cloud services like Azure Key Vault and AWS Certificate Manager.
Keyfactor orchestrators and agents allow for the discovery of these certificates so that you can bring every certificate under management. This will catch rogue certificates that are out there that could come up unexpectedly and cause an outage. Tools should be able to perform this discovery using agents or agent-less methods.
Take Control of All Your Certificates
Ready to take control of all your certificates?
Join the discussion and watch a demo of the three simple ways that Keyfactor gives you complete visibility of all certificates in your inventory, regardless of where they were issued from or where they live.