DNS poisoning, also known as DNS cache poisoning or DNS spoofing, is a highly deceptive cyber attack in which hackers redirect web traffic toward fake web servers and phishing websites. These fake sites typically look like the user’s intended destination, making it easy for hackers to trick visitors into sharing sensitive information. Note: if you’re looking for information on IP spoofing attacks, check out my previous blog.
This article will explore everything you need to know about DNS poisoning, including:
- What is DNS poisoning/DNS spoofing
- How DNS poisoning works
- Why it is so dangerous
- Examples of DNS spoofing attacks
- How to protect your organization against DNS poisoning attacks
What is DNS poisoning?
DNS poisoning is a type of spoofing attack in which hackers impersonate another device, client or user. This disguise then makes it easier to do things like intercept protected information or interrupt the normal flow of web traffic.
In a DNS cache poisoning attack, hackers alter a domain name system (DNS) to a “spoofed” DNS so that when a legitimate user goes to visit a website, instead of landing on their intended destination they actually end up at an entirely different site. Usually, this happens without users even knowing, as the fake sites are often made to look like the real ones.
Think of it like telling someone you live at a certain address and then going to that neighborhood and changing around all of the street names and house numbers so that they actually end up in at the wrong address or a completely different house.
Once the attack is underway, diverting traffic to the illegitimate server, hackers can then accomplish malicious activities like a man in the middle attack (e.g. stealing secure login information for bank websites), installing a virus onto visitors’ computers to cause immediate damage, or even installing a worm to spread the damage to other devices.
How does DNS poisoning work?
Fully understanding how DNS poisoning works requires a bit of context on how the internet routes users to visit different websites.
Every device and server has a unique internet protocol (IP) address, which is a series of numbers used as identifiers in communications. Every website has a domain name (e.g. www.keyfactor.com) that sits on top of that to make it easy for internet users to visit the websites they want. The domain name system (aka DNS) then maps the domain name that users enter to the appropriate IP address to properly route their traffic, all of which gets handled through DNS servers.
DNS poisoning takes advantage of weaknesses in this process to redirect traffic to an illegitimate IP address. Specifically, hackers gain access to a DNS server so that they can adjust its directory to point the domain name users enter to a different, incorrect IP address.
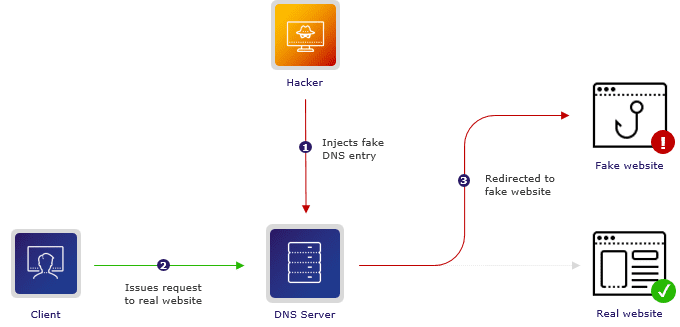
Once someone gains access to a DNS server and begins redirecting traffic, they are engaging in DNS spoofing. DNS cache poisoning takes this one step further. When DNS cache poisoning happens, a user’s device places the illegitimate IP address in its cache (aka memory). This means that the device will automatically direct the user to the illegitimate IP address — even after the issue is resolved.
The biggest weakness that allows this type of attack to occur is the fact that the entire system for routing web traffic was built more for scale than for security. The current process is built on what’s called the User Datagram Protocol (UDP), a process that does not require senders or recipients to verify they are ready to communicate or verify who they are. This vulnerability allows hackers to fake identity information (which requires no additional verification) and step into the process to start redirecting DNS servers.
While this is absolutely an enormous vulnerability, it is not as simple as it sounds. To pull this off effectively, a hacker must respond to a request within a few milliseconds before the legitimate source kicks in and include in their response detailed information like the port the DNS resolver is using and the request ID number.
Why is DNS poisoning so dangerous?
DNS poisoning poses several risks to individuals and organizations alike. One of the biggest risks associated with DNS poisoning is that once a device has fallen victim to it, especially DNS cache poisoning, it can become very difficult to resolve the issue because the device will default to going back to the illegitimate site.
Furthermore, DNS poisoning can be extremely difficult for users to detect, particularly in cases where hackers make the fake website to which they direct traffic look almost identical to the real one. In these cases, users are likely to have no idea the website is actually a fake and will input sensitive information as normal without realizing they are exposing themselves and/or their organizations to serious risk.
Overall, some of the biggest dangers with this type of attack include:
Viruses and malware
Once users get directed to fraudulent websites, hackers can gain access to install a host of viruses and malware on their devices. This can cover everything from a virus intended to infect their device (plus other devices they contact) to malware that gives the hackers ongoing access to the device and information it contains.
Theft
DNS poisoning offers an easy way for hackers to steal information, such as logins for secure sites (everything from banks to organizational systems that house proprietary information), personally identifiable information like social security numbers and other sensitive details like payment information.
Security blockers
Malicious actors can use DNS poisoning to cause severe long term damage by redirecting traffic from security providers to block devices from receiving important patches and updates that strengthen security. This approach can make devices more vulnerable over time, opening the door for numerous other types of attacks like Trojans and viruses.
Censorship
There have been past instances of governments intervening in web traffic from their country via DNS poisoning to censor certain information. Intervening in this way has allowed these governments to block traffic from citizens to websites that contain information they do not want them seeing.
Examples of DNS spoofing attacks
Several high profile DNS poisoning attacks have occurred in recent years that highlight the dangers of this type of attack.
Stolen cryptocurrency from MyEtherWallet via a DNS spoofing attack on Amazon Web Services (AWS)
In 2018, a group of thieves managed to launch a DNS poisoning attack on AWS to reroute traffic from several domains hosted on this system. One of the most notable of these attacks centered around the cryptocurrency website MyEtherWallet.
Specifically, the thieves redirected traffic from people attempting to log in to their MyEtherWallet account to a fake website to capture their login credentials. From there, the group used that information to access those users’ actual accounts and drain their funds. In total, the group stole about $17 million worth of the cryptocurrency Ethereum throughout the course of this DNS poisoning attack.
Havoc and potentially stolen personal data via DNS poisoning attack on Malaysia Airlines
In 2015, a hacker group known as Lizard Squad launched a DNS poisoning attack on Malaysia Airlines in which they redirected site visitors to a fake website that encouraged them to log in only to be greeted by a 404 message and picture of a lizard.
First, this attack wreaked significant havoc on the airline, which had already come off a difficult year in which two flights were lost. Second, it raised serious questions around whether or not the hacker group stole personal information about any of the users who were part of the attack and logged in to the fake website.
Censorship spreads across countries via leak from China's servers
In 2010, internet users in Chile and the United States found their traffic to sites like Facebook, Twitter and YouTube getting redirected as a result of coming under the control of servers in China.
China had purposely manipulated its own servers via DNS poisoning as a form of censorship. In this instance, users outside of China got routed to the country’s servers and became a victim of that censorship, losing access to websites that China had blocked its citizens from visiting.
How can you protect your organizations from DNS poisoning and spoofing attacks?
DNS poisoning attacks are so dangerous because they can be difficult to detect and difficult to remediate once they do take hold (especially in the case of DNS cache poisoning). That said, there are several steps you can take to better protect your organization from the risks posed by DNS poisoning attacks. Some of the best ways to protect your organization include:
1) Introduce DNS Security Extensions (DNSSEC)
Introducing DNSSEC is one of the most valuable steps you can take to protect against DNS poisoning attacks. Quite simply, DNSSEC takes the added step of verifying DNS data — something that is not standard in the current internet protocols.
DNNSEC relies on public key cryptography to make this verification possible. Specifically, it uses certificate-based authentication to verify the root domain of any DNS responding to a request and ensure it is authorized to do so. It also evaluates whether or not the content of the response can be trusted and whether or not those contents might have been modified in transit.
2) Always encrypt data
Another important step you can take is always encrypting data included in DNS requests and answers. This offers an added layer of protection by preventing hackers who might be able to intercept that data from doing anything with it.
For example, even if a hacker does manage to intercept that data, if it’s encrypted, they won’t be able to read it in order to get the information they need to duplicate it for use in responses to future DNS requests.
3) Enable secure DNS configurations
Your organization can also take steps to configure your DNS in certain ways that provide an additional layer of protection. First, you can configure your DNS servers so that they don’t rely heavily on relationships with any other DNS servers. Doing so makes it far more difficult for hackers to establish a connection via their own DNS server, since establishing that relationship will no longer make sense in the normal course of business.
Second, you can configure your DNS servers to store more limited sets of data so that they only allow certain services to run. This configuration avoids opening up your server to more data, which creates far more potential points of weakness that hackers can exploit.
4) Regularly run system updates
As is now the case with most systems, your DNS will be eligible for regular system updates. Making sure you always run these updates so that you use the most recent version of your DNS is extremely important, since these updates often include new security protocols and fixes to any identified vulnerabilities. Additionally, staying on the latest version will ensure you can continue to receive updates going forward.
5) Introduce strong detection protocols
While prevention tactics are certainly important, you also need to have a good plan in place for if a DNS poisoning attack does take place. This is where strong detection protocols become very important.
The best detection protocols use regular monitoring to look for certain warning signs. Two of the biggest warning signs are (1) an increase in DNS activity from a single source about a single domain, which can indicate a Birthday attack and (2) an increase in DNS activity from a single source about multiple domain names, which can indicate attempts to find an entry point for DNS poisoning.
6) Lead end user training
Another important detection tactic is leading end user training to help users become aware of potential risks. While DNS poisoning attacks can be very difficult for even well-trained users to spot, strong training can certainly help stem the spread of certain attacks.
Training should instruct users to verify that websites are using a valid SSL/TLS certificate, avoid clicking on links they don’t recognize or links from sources they don’t recognize, regularly clear their DNS cache to protect against DNS cache poisoning and run security software that can scan their devices to look for signs of malware.




