Issue certificate-based identities from a trusted and highly scalable PKI to secure your vehicles after they roll off the line.
Secure vehicles and charging infrastructure
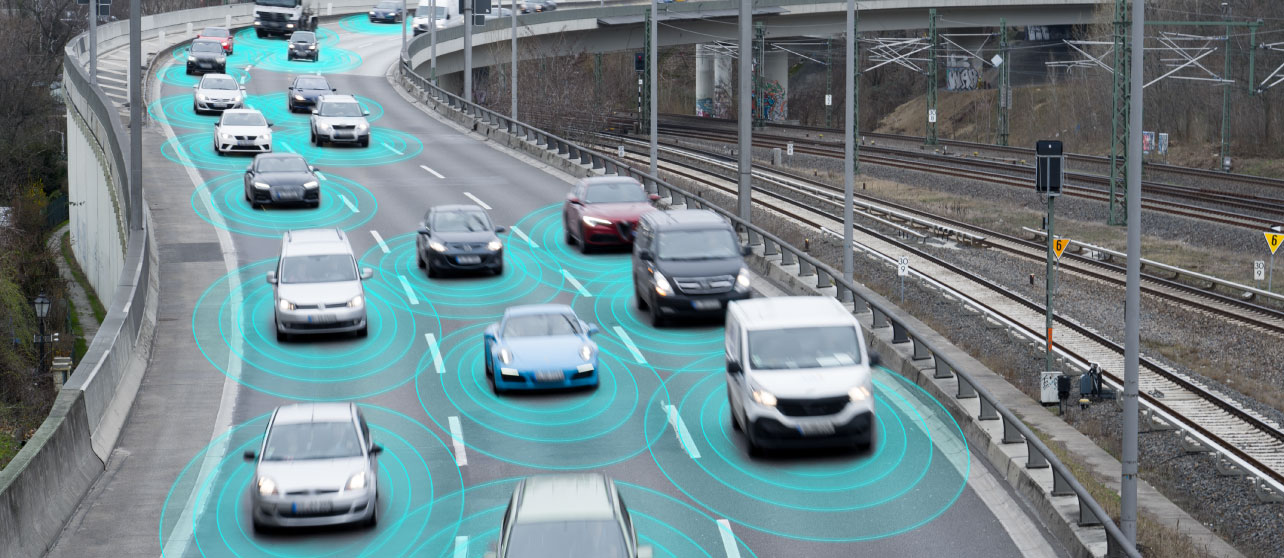
Every year vehicles are becoming more advanced — and complex. With hundreds of engine control units and millions of lines of code, automotive OEMs and suppliers must ensure that every vehicle and charging component has identity-first security from manufacturing to the end of the road.

THE CHALLENGES
Complex vehicles mean
complex security risks.
Every year, vehicle manufacturers develop and combine new technologies to make travel safer and more enjoyable. But every new controller and line of code opens a new attack surface. With hundreds of communicative components, complex supply chains, and millions of lines of code, automotive manufacturers and suppliers must ensure that every component is secure.
OUR APPROACH
Identity-first security for
Vehicle manufacturers & suppliers
Identity-first security makes it possible for manufacturers to issue and manage
identities for every connected component and vehicle, at scale,
and keep them up to date with only authorized, trusted code.
WHY KEYFACTOR
Protect your production line,
without slowing it down
Keyfactor combines the right expertise and technology to help
leading manufacturers protect their vehicles and supply chain
across their production environments and beyond.
Solutions for automotive security
Meet the Keyfactor solution stack. Our solutions are supported by an army of
PKI and IoT security experts that work with our customers from solution design
and architecture to deployment and implementation.
WHITE PAPER
How to Navigate Complex Supply Chains to Build Trusted IoT Devices