The Cybersecurity Maturity Model Certification (CMMC) is quickly becoming a household term in the IT and security community. Why? The new security standard impacts more than 300,000 companies across the globe.
In this blog, we’ll cover what it is, who needs CMMC certification, and why it’s important to the overall state of security in the complex supply chains that support the US Department of Defense (DoD) and national security.
What is the CMMC?
The CMMC is a certification procedure developed by the DoD to certify that their contractors have adequate controls to protect sensitive data, including Federal Contract Information (FCI) and Controlled Unclassified Information (CUI), against unauthorized disclosure. The CMMC Model is based on and harmonizes best practices from a variety of cybersecurity standards including NIST SP 800-171, NIST SP 800-53, and ISO 27001.
Previously, contracting authorities and prime contractors were responsible for implementing and certifying the security of their own information systems. Contractors remain responsible for implementing security controls, however, the CMMC now requires third-party assessments to ensure compliance with mandatory practices and procedures.
CMMC came as a response to the increasing number of cyber threats targeting DoD contractors. The DoD mission and operations depend largely on extensive and complex supply chains. Gaps in the cybersecurity policies and practices implemented by this vast network of DoD suppliers pose a huge cyber risk.
Who needs CMMC certification?
There are more than 300,000 defense contractors, manufacturers, and even small businesses involved in the defense industrial base (DIB). These include both “prime” contractors who engage directly with the DoD, and subcontractors who may perform fulfillment or execution for prime contractors.
The DoD began incorporating CMMC requirements into select RFPs / RFIs as of November 30, 2020. By fiscal year 2026, all DoD contract awards will require at least some level of CMMC certification.
Domains, practices, and maturity levels
CMMC Framework
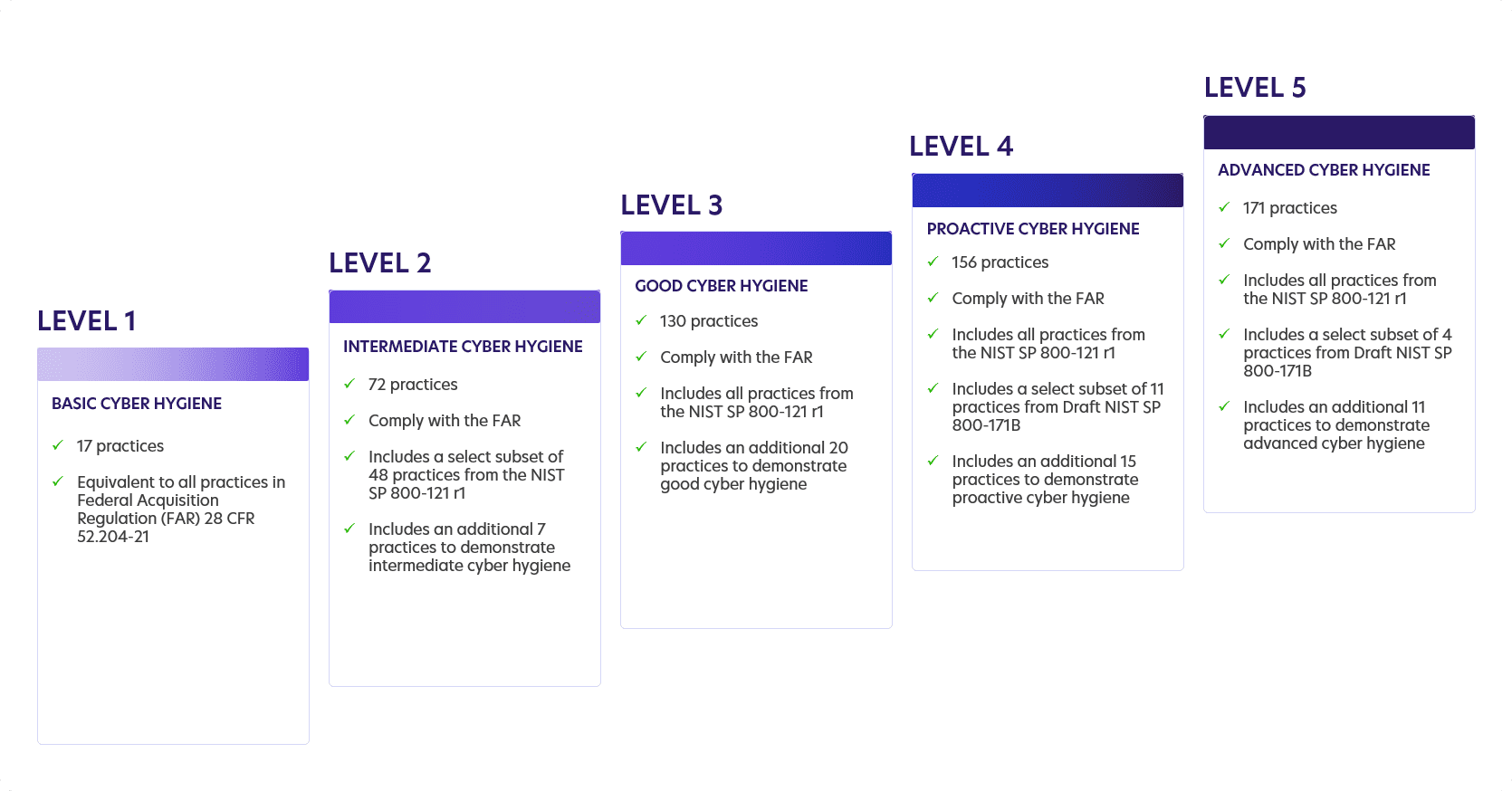
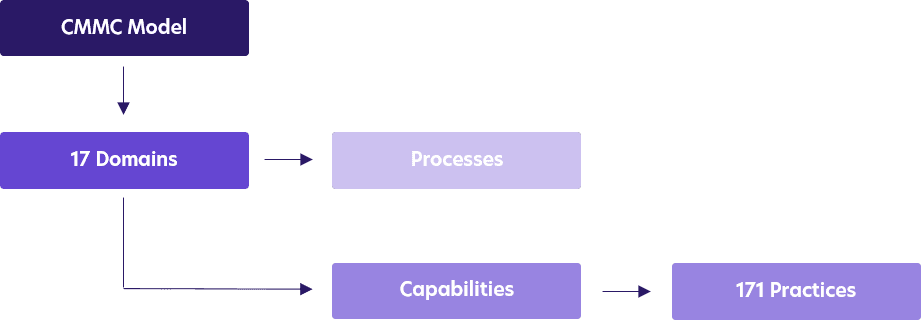
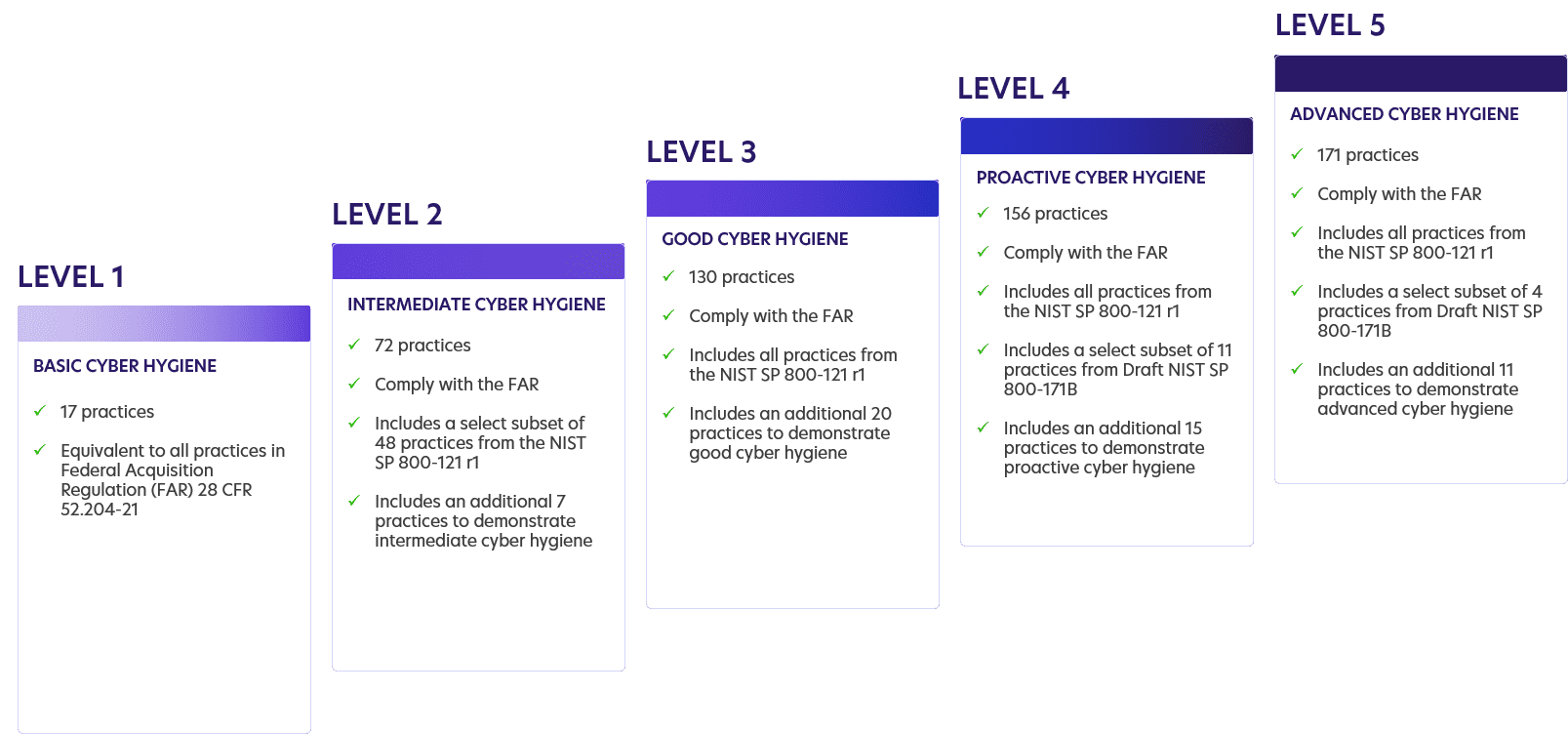
The CMMC framework evaluates cybersecurity maturity within five levels of maturity. Each CMMC level consists of a set of processes and practices which are mapped against the type, sensitivity, and risks to the information that must be protected. The processes are organized into domains, while the practices are aligned to a set of capabilities per domain.
Domains
There are 17 domains in the CMMC framework ranging from access control to systems and information integrity. Each domain represents a group or “bucket” of security practices that must be met by the organization. Companies are certified against five levels of compliance across all of these security domains.

Light purple represents areas where PKI and machine identities play an important role.
Practices
Within the CMMC model, there are 171 practices that span across all 17 domains. These practices are mapped to five levels of maturity. More advanced practices are required to meet higher levels of maturity.
Maturity Levels
Each maturity level includes processes, and the vendor needs to demonstrate process maturity by integrating the activities into the operations of the organization. Basic cyber hygiene starts at Level 1 and each level requires compliance with additional practices, procedures, and capabilities all the way up to advanced cyber hygiene at Level 5.
The importance of PKI and machine identities to CMMC compliance
Ensuring the confidentiality and integrity of Controlled Unclassified Information (CUI) is a key component of CMMC compliance. Once DoD contractors identify and classify their data, they need to cryptographically protect it both at rest and in transit.
- Practice SC.3.185 requires implementing cryptographic mechanisms to prevent unauthorized disclosure of CUI during transmission.
- Practice SC.3.191 asks DoD contractors to protect the confidentiality of CUI at rest.
Besides protecting the confidentiality and integrity of CUI, protecting the authenticity of communications is also essential.
- Practice SC.3.190 determines that the authenticity of communications is to be protected against man-in-the-middle attacks, session hijacking, and the insertion of false information. This requirement establishes confidence and trust at both ends of communications sessions on the identity of the parties and the validity of information transmitted.
However, these controls will not be sufficient if they are not supplemented by an effective mechanism for the lifecycle management of machine identities, such as cryptographic keys and digital certificates.
- Practice SC.3.187 requires DoD contractors to manage the cryptographic keys used for securing CUI and authenticating communications.
In accordance with CMMC, organizations need to “develop processes and technical mechanisms to protect the cryptographic keys’ confidentiality, authenticity, and authorized use in accordance with industry standards and regulations.”
In other words, defense contractors and companies within the defense supply chain must build a robust Public Key Infrastructure (PKI) to issue keys and certificates that are trusted, up to date, and compliant with established standards.
Not only that, but they must ensure they have a complete inventory of all cryptographic assets, enforce standardized policies around their use, and automate the lifecycle of keys and certificates to prevent loss, compromise, or misuse.
Securing the defense supply chain
Here we’ve covered just a few of the most important PKI and machine identity management practices within the CMMC model. However, it takes more than just a few practices to protect every machine identity across the defense supply chain.
Considering the vast and complex supply chains supporting the mission and operations of DoD, getting security right is critical. Just take a minute to reflect on the impact of SolarWinds attacks to realize why DoD contractors need a solid strategy to manage every machine identity – including SSL/TLS, SSH, and code-signing certificates.
More machines, such as containers, cloud workloads, IoT, and mobile devices, are being introduced into the supply chain, increasing the risk of machine identity compromise. Complying with CMMC requirements is a start, but it takes more than checkboxes to ensure that your organization is protected from costly outages and security risks.
Want to learn more about how you can take control of machine identities and ensure compliance with CMMC security requirements? Request a demo today.