Death, Taxes, and Weakening Cryptography
“Nothing is certain except death and taxes.” Ben Franklin is often credited with coining this phrase; however, the first known appearance of “death and taxes” in this usage came from a playwright named Christopher Bullock in 1716. But for all their wisdom, neither Ben Franklin nor Christopher Bullock may not have been able to predict something that most seasoned security professionals now regard as fact today:
The crypto algorithms we use today will be insecure in the future.
Several factors conspire to weaken cryptographic algorithms over time. These include the following:
- Advances in Computing Technology
Moore’s Law predicts that computing power and density increases exponentially over time. While not a “law,” this general trend has held true for quite some time and is often used by cryptographers to estimate minimum key sizes over time. The faster computers get, the larger your cryptographic keys have to be to remain out of reach. Websites such as www.keylength.org do a great job of encapsulating information regarding algorithm and key size strength recommendations.
- Quantum Computing
Another facet of computing technology is quantum computing. While research into quantum computing has been going on for quite some time, recent advancements have started to garner more attention from the cryptographic community. Many experts watching this industry, such as Gartner, now predict that quantum computers that can legitimately defeat 2048-bit RSA or 256-bit ECC may appear between 2025 and 2030.
- Unforeseen Cryptographic Flaws
Cryptographers are human and are therefore not perfect. And while cryptographic algorithms are subject to intense scrutiny before adoption, flaws that weaken the algorithms, or that lead to stipulations about how they may be used or implemented, often do come to light. The more widely an algorithm is adopted, the more motivation attackers will have to defeat it. Typically these flaws are not entirely catastrophic when discovered; however, they lead to a weakening of the effective key strength of the algorithm. Such flaws have been found in RSA, SHA-1, MD5, DES, and many others.
- Historical Inference
We also have history to draw from in this regard, in that we’ve seen this happen to other algorithms already: DES, MD2, MD5, SHA-1, smaller RSA keys, and others have all followed this path. Below is a chart that I put together for a webinar about the impending end-of-life of SHA-1, in January 2014:
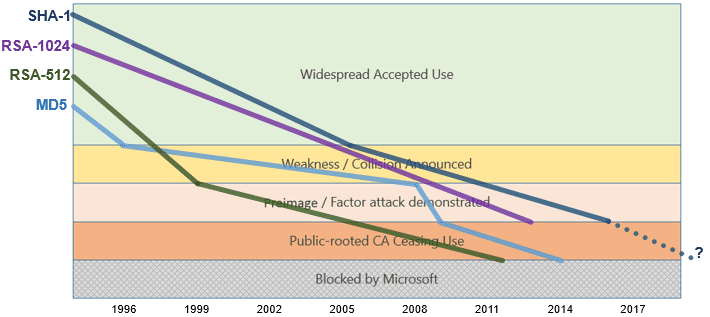
In essence, if you chart the aging of algorithms over time by the progress from accepted usage, through various stages of splintering on to outright banishment, MD5, SHA-1, 512-bit and 1024-bit RSA have followed a similar slope. In January 2014, 1024-bit RSA had not yet been blocked across the board, but it was on the horizon. My prediction for SHA-1’s termination would have been about 2020, but clearly, it’s happened a bit faster than that.
What now?
Savvy product architects and engineers have realized that products must be designed with “crypto-agility” in mind – meaning that static systems simply can’t be secure in the future. Cryptographic keys must be replaced over time, and even the algorithms involved must also change. This key replacement is especially critical for “Internet of Things” (IoT) devices, which may stay in the field for dozens of years or more.
IoT devices often have power, bandwidth, or processing constraints that may prevent cryptographic updates – or at least make the implementation of such updates much more difficult. Nonetheless, the architects of these systems will be well-served to acknowledge the reality of the situation, and to the best extent possible, design for the cryptographic landscape to which their devices will be subjected throughout their lifespan. This planning is essential, even if the mechanisms to do so require more work to implement; it’s why we list “crypto-agility” as one of our 5 Fundamental Tenets of IoT Security.
Even if the approach is to plan for a full-fleet replacement of devices when the cryptographic attacks materialize, it’s better to have planned for the eventuality up front, rather than be caught by surprise. And the planning is worthwhile because we know the algorithms we use today will be insecure in the future.
It’s as certain as death and taxes.