EJBCA Enterprise 7.9.0, now generally available, introduces vehicle-to-everything (V2X) PKI capabilities to provide trustworthy and reliable communications between connected vehicles and road infrastructure.
By 2025, it is projected that there will be over 400 million connected cars in operation, up from some 237 million in 2021. Many vehicles already feature new capabilities that allow us to get real-time updates, drive more safely, and even connect with the world around us — whether we’re on our daily commute or a cross-country road trip.
The innovation is endless and it’s all driven by one thing — connectivity. From components within the car to infrastructure on the road, the number of connections in the transportation ecosystem is growing rapidly, and it’s just the beginning.
What is V2X?
Vehicle-to-everything (V2X) is an all-encompassing term for the communications between vehicles (vehicle-to-vehicle) and the infrastructure that surrounds them (vehicle-to-infrastructure). Several applications of V2X communications have emerged and many more are on the horizon, and the benefits are clear.
Communication between vehicles and road infrastructure, such as traffic lights, parking spaces, roadside units, and other systems can help to improve efficiency and safety by allowing vehicles to make real-time decisions based on changing conditions.
Just imagine: You take the train from your home to the city, then walk straight into a ride-share vehicle that is waiting at the station to drive you to your office. Or, imagine there’s been a minor car accident in the intersection, and the traffic lights automatically adjust to prevent further damage, while emergency vehicles are notified immediately.
The possibilities are endless, but the coordination required to make V2X a practical reality is still a work in progress. The future of V2X is dependent on collaboration between automakers, infrastructure developers, and government agencies to establish and comply with industry-wide standards.
Enter C-ITS and PKI
Cooperative Intelligent Transport Systems (C-ITS) is an ecosystem that facilitates communication between vehicles and infrastructure.
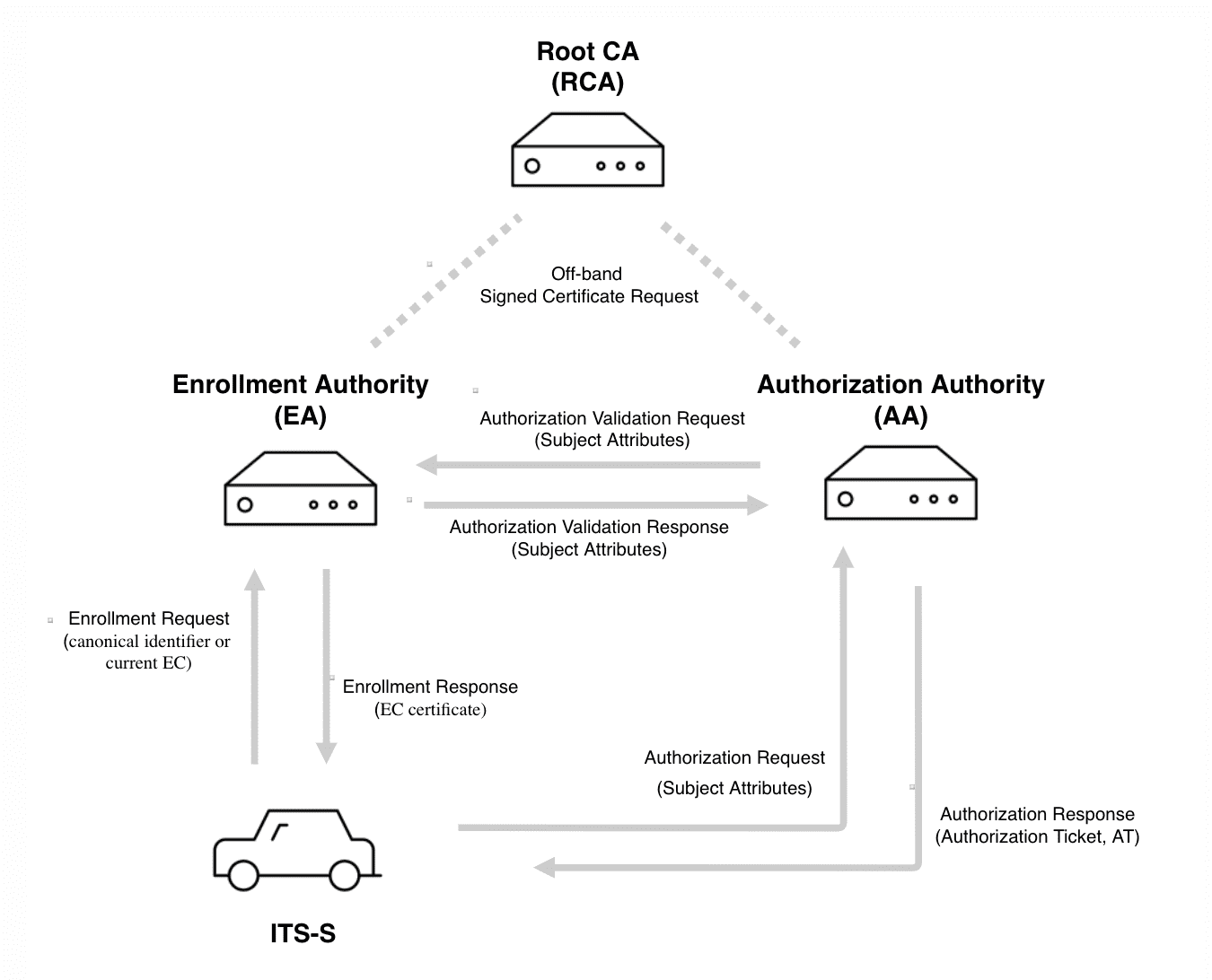
Since these communications involve exchanging sensitive data between the vehicles and other entities, such as road infrastructure and road safety applications, it is critical to protect and secure its communication. To enable secure V2X communications for C-ITS, public key infrastructure (PKI) is used to issue and manage trusted security credentials for vehicles and infrastructure components, commonly known as ITS Stations (ITS-S).
Technical security standards related to V2X communications are available and under development. The US standard IEEE 1609.2 covers security aspects, including secure message formats and security management. In Europe, ETSI publishes EU standards for C-ITS that extend the IEEE standard.
V2X PKI with EJBCA Enterprise
EJBCA is a highly scalable and flexible PKI platform, designed for modern connected ecosystems like V2X. Built on open standards and a Common Criteria-certified open-source platform, the certificate authority (CA) is transparent and reliable, with already widespread use across the automotive and transportation sectors today.
With EJBCA 7.9.0, we’ve furthered our commitment to securing the connected vehicle by introducing functionality that allows EJBCA to act as an Enrollment Authority (EA) in a C-ITS PKI, registering ITS entities and issuing enrollment credentials.
While there are several components that make up the C-ITS Security Management System, including the Root Certificate Authority (RCA) and Authorization Authority (AA), the development of EA capabilities marks our first effort toward supporting the C-ITS PKI lifecycle with EJBCA.
To learn more about V2X PKI capabilities with EJBCA, click here.