Today, we are excited to announce a new partnership between Keyfactor and Google Cloud. The integration combines Keyfactor’s highly scalable cloud-based certificate lifecycle automation with Google Cloud Certificate Authority Service to meet the needs of modern security, infrastructure, and application teams.

Before we dive into the integration, let’s talk a bit about how the use of public key infrastructure (PKI) and machine identities has changed in recent years, and why it demands a new cloud-first approach to PKI and certificate management.
The machine identity boom
Digital certificates have been the de facto standard for device and machine identity since the start of the Internet. However, with the normalization of identity-driven zero trust security and multi-cloud strategies, the sheer volume of certificates has increased from hundreds to hundreds of thousands (even hundreds of millions in larger enterprises).
These certificates are consumed by various teams and applications across the organization: from traditional web servers and load balancers, mobile and IoT devices, and increasingly, in CI/CD tools and cloud-based infrastructure.
If we break it down, there are three primary use cases behind the rapid growth of certificates in the enterprise, each with its own unique challenges:
Enterprise IT
Certificates are routinely deployed to establish trusted identities for machines and users on the corporate network. This often includes server and Wi-Fi access points, network devices and load balancers, and device authentication for workstations and mobile devices.
Typically, these use cases are supported by an internal PKI team that maintains a private CA on-premise, and manually handles certificate requests for other IT functions – a task that becomes next to impossible at scale. With more certificates and shorter lifespans, the effort to keep up with requests and track expirations manually just isn’t feasible.
DevOps
Certificates have also emerged as a powerful tool in DevOps environments to authenticate cloud workloads, containers, microservices, as well as ingress and mTLS in service mesh architectures. Unlike in traditional IT infrastructure, developers and application teams are in the driver’s seat, and security is frequently overlooked.
DevOps teams need rapid, high-volume issuance of short-lived certificates to support the on-demand nature of cloud infrastructure. To avoid manual PKI processes, many opt for non-compliant or self-signed CAs that introduce several risks. Once security teams get involved, they often hold up projects or even halt operations until trust requirements are met.
IoT Devices
Manufacturers and developers also recognize certificates as the ideal solution for identity in connected/IoT devices. However, managing millions of certificates across a fleet of distributed devices from design through the device lifecycle is no easy feat. Hardware constraints, intermittent connectivity, and scalability all factor into the complexity of PKI for IoT.
With the sheer scale of IoT devices in the market today, it’s impossible to imagine provisioning and managing certificates manually. More importantly, if a security incident occurs, millions of certificates will need to be revoked and reissued very quickly and without disruption to end-users. That just isn’t doable without an automated approach.
There's just one problem (make that two)
As the use of PKI and digital certificates grows, two fundamental challenges emerge: (1) how to effectively manage and scale PKI to meet increased demands, and (2) how to manage many thousands of certificates across all of your different teams and applications.
Traditional CAs are a pain
Setting up a PKI is more than just generating a private CA and issuing certificates. It requires highly skilled personnel, specialized infrastructure and security controls, and continuous maintenance to remain secure and operational. Traditional private CAs like Microsoft ADCS also aren’t well-equipped to integrate with cloud platforms and DevOps toolsets.
Certificates are everywhere
Now consider the thousands of certificates issued into these combined enterprise IT, DevOps, and IoT environments. Each certificate needs to be individually provisioned, installed, and eventually renewed before it expires, and every application has a different process to make that happen. At this scale, things can quickly get out of hand.
To thrive in the era of hybrid and multi-cloud infrastructure, IT and security teams need to seriously rethink how they deploy their PKI and manage digital certificates. The key to success is simple, repeatable processes for certificate management across all platforms and devices.
Keyfactor + Google CA Service
Google Cloud Platform’s Certificate Authority Service (CAS) allows teams to simplify the deployment and management of private CAs for their cloud-native workloads and applications. Now Keyfactor customers can plug directly into Google CAS to seamlessly integrate cloud-based private CAs into their overall enterprise PKI strategy.
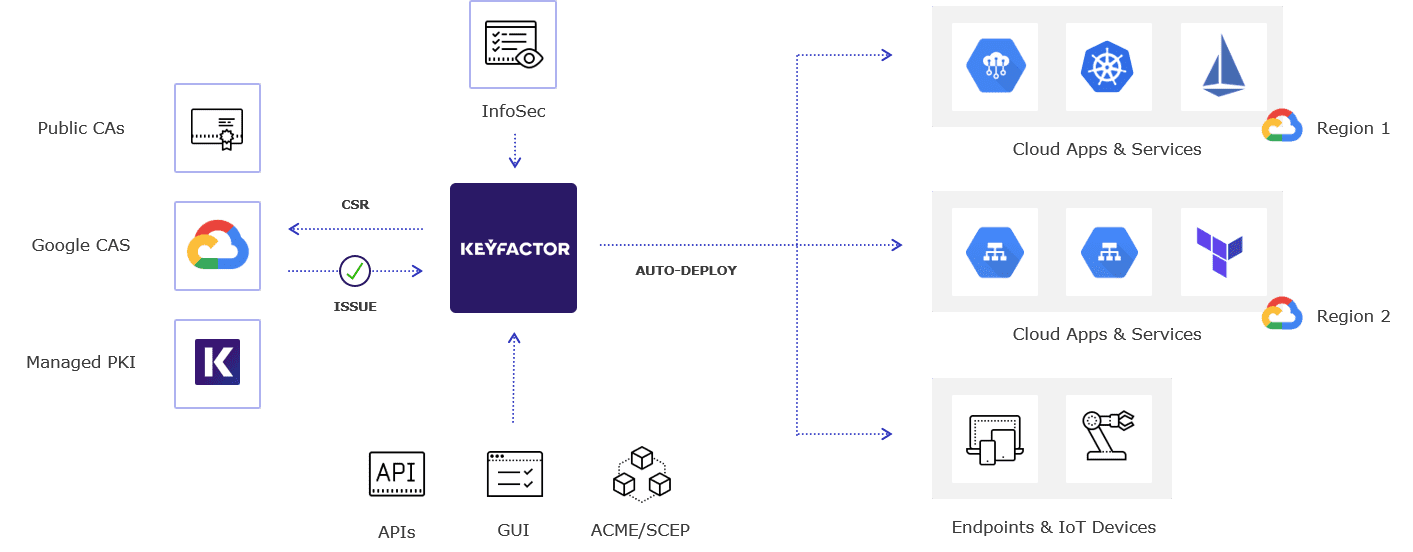
Using the flexible AnyCA GatewayTM, Keyfactor synchronizes in real-time via the Google Certificate Authority Service API to continuously inventory every certificate issued. With a complete inventory, PKI teams have a centralized view into the health and status of all certificates, backed by powerful protocol-based and out-of-the-box automation.
- Multi-CA, multi-cloud: Keyfactor provides a comprehensive view of all machine identities in a single console via public and private CA integrations, network-based discovery, and authenticated discovery of key and certificate stores.
- Self-service: Application owners can quickly request and provision certificates automatically via a user-friendly self-service interface or RESTful APIs.
- Auto-enrollment: Google-issued certificates can be auto-enrolled via protocol-based automation, such as SCEP or ACME, using proxies built into the Keyfactor platform.
- Automated provisioning: Keyfactor Orchestrators automatically renew and provision certificates to multiple servers, devices, and network endpoints.
- DevOps & IoT integrations: Native integrations and plugins make it easy for teams to automate certificate deployment to popular tools such as HashiCorp Vault, Jenkins, Kubernetes, Istio service mesh, and more.
- Flexible deployment: Customers can deploy certificate lifecycle automation (CLA) within their datacenter, in Google Cloud, or as a service (CLAaaS).
Get started today
Explore our integration hub to learn more about our plugins with Google Cloud Certificate Authority Service (CAS) and Google Cloud Load Balancer.
Ready to talk to Keyfactor? Request a 1:1 demo with a solutions engineer today.