The world of IoT devices and machines is divided into two classes: those with abundant power and connectivity bandwidth and those with a much more strictly limited budget. But both classes of devices still have the same security requirements.
The first category does not prioritize energy savings or communication protocol efficiency. These devices are fluent in IP, TCP, TLS, HTTP, MQTT, etc., and have no excuse not to use X.509 certificates and private PKI to secure their communications. Cars, factory machinery, wind turbines, HVAC systems, gateways, home assistants, and TVs: their favorite media are ethernet, WiFi, and 4G/5G cellular. These types of devices are always connected and ready to interact with distant servers, making it easy to update them with new firmware whenever necessary.
While the second category of devices does not have the same abundant power or connectivity as the first device group, they’re still called “smart” devices. It includes things like battery-operated meters, smart home thermostats, smart asset or pet trackers, smart crop sensors, cellular-connected electricity smart meters, and even electric bikes or scooters. They all have in common a vital need to fit into a strict business model where every cost has been carefully planned. For example, a smart meter must operate on the same 10Ah battery for at least 15 years because sending someone to replace it would more than double the total cost of ownership. Or consider an electric bike – it has a connectivity allowance of no more than 12MB per month because this is how the manufacturer has negotiated and pre-paid their six-year contract with the cellular operator. These assets are constantly trying to optimize everything they do. They connect to the internet via WiFi, cellular LTE-M or NB-IoT, LoRaWAN, BLE, SIGFOX, Zigbee, or Thread but need to remain as silent as possible and go to sleep as much as they can.
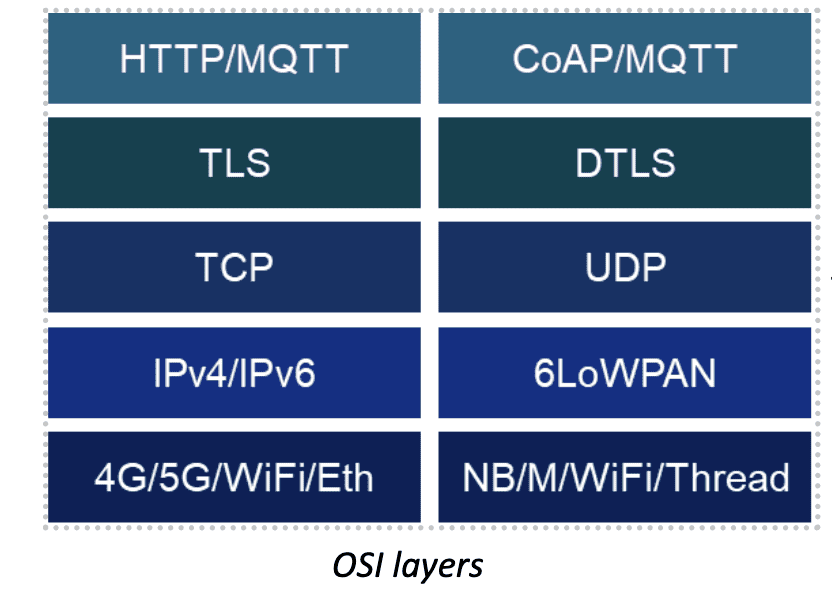
It takes a lot of thought to design the latter class of smart devices because of their “low” profile: low-cost and low-power silicon, low-bandwidth connectivity, low-memory footprint stacks, and, more recently, low environmental impact. Since these devices generally transmit lesser amounts of data – from a few bytes to a few hundred at a time – they need to optimize how they connect to other devices or servers. In this regard, the TCP/TLS/HTTP stack, which was primarily designed for web pages and internet browsing, with an average packet size of 1500 bytes, is not a good match, as it adds too much overhead at every layer.
For this reason, in its RFC7252 the Internet Engineering Task Force (IETF) has standardized the Constrained Application Protocol (CoAP) as an efficient alternative to HTTP for this class of devices. It is accommodating to lossy packet transmissions and is, therefore, a perfect fit for UDP, the lighter alternative to transport layer TCP.
But it’s important to keep in mind that in this context, a “lower” profile does not mean “sub-par” or “cheap.” In the past, lower-powered devices have relied on pre-shared symmetric keys that are awkwardly commissioned and never renewed as digital certificates were viewed as too heavy for the devices. Now, however, with advances in technology and protocols, X.509 certificates and private PKI can be used in both classes, providing resource-constrained devices with the same security that their more powerful counterparts currently use today.
The Matter and WiSUN standards for smart home and smart metering, respectively, are the perfect illustration of how low power and low bandwidth can coexist with state-of-the-art PKI. By selecting Elliptic Curve Cryptography (ECC) over legacy RSA, the size of an X.509 certificate can be limited to a few hundred bytes, perfectly designed for constrained devices.
And by choosing a PKI software or service which allows Enrollment over Secure Transport (EST – RFC7030) over CoAP (EST over CoAP), it is now possible to pull unique initial device certificates securely from a private PKI and inject them into devices at manufacturing. Additionally, you can renew devices’ operational certificates over the air, at will, throughout the life of the devices without needing to design any special certificate life-cycle management agent or dedicate power and connectivity budgets to the task. Now enrollment, re-enrollment, and renewal are all handled by CoAP requests and responses to and from the PKI and are secured by DTLS.
Keyfactor’s latest release, EJBCA 8.0, introduces EST over CoAP to support the enrollment and certificate renewal of WiSUN, NB-IoT, and LWM2M connected smart meters into the private PKI of the electricity, water, or gas provider. Until recently, smart meters were protected by permanent symmetric keys or relying on the partial security of their wireless connection only. Now, with X.509 certificates issued and managed by the utility providers, they can now guarantee end-to-end authentication and security to the back-end servers of these utility providers and securely accept occasional over-the-air firmware updates.
Learn how new EJBCA capabilities bolster IoT device security.




