If you’ve spent any time in the PKI space, you’ve likely heard a lot about crypto agility recently, but what does it really mean?
Crypto agility is all about future-proofing elements of your PKI program, like signing algorithms and key strengths, to account for upcoming evolutions. For example, right now there’s a lot of talk about getting ready for quantum computing, and that involves updating and strengthening your keys so that they remain up to date with evolving standards.
Ultimately, achieving crypto agility comes down to four critical areas:
- Ensuring visibility into all of your keys and certificates
- Getting in control of those elements to make sure they’re compliant with the right policies
- Automating the renewal of certificates to avoid outages vs. missed manual renewals
- Orchestrating those policies and renewals across all your different DevOps toolchains or pipelines by integrating with solutions like Istio and HashiCorp
All of these areas are important, but visibility is the big one to start. That’s because if you don’t know the state of your cryptography, PKI operations become exceedingly difficult. And when it comes to visibility, these are the top ten most important metrics to track.
1) Expiration Status
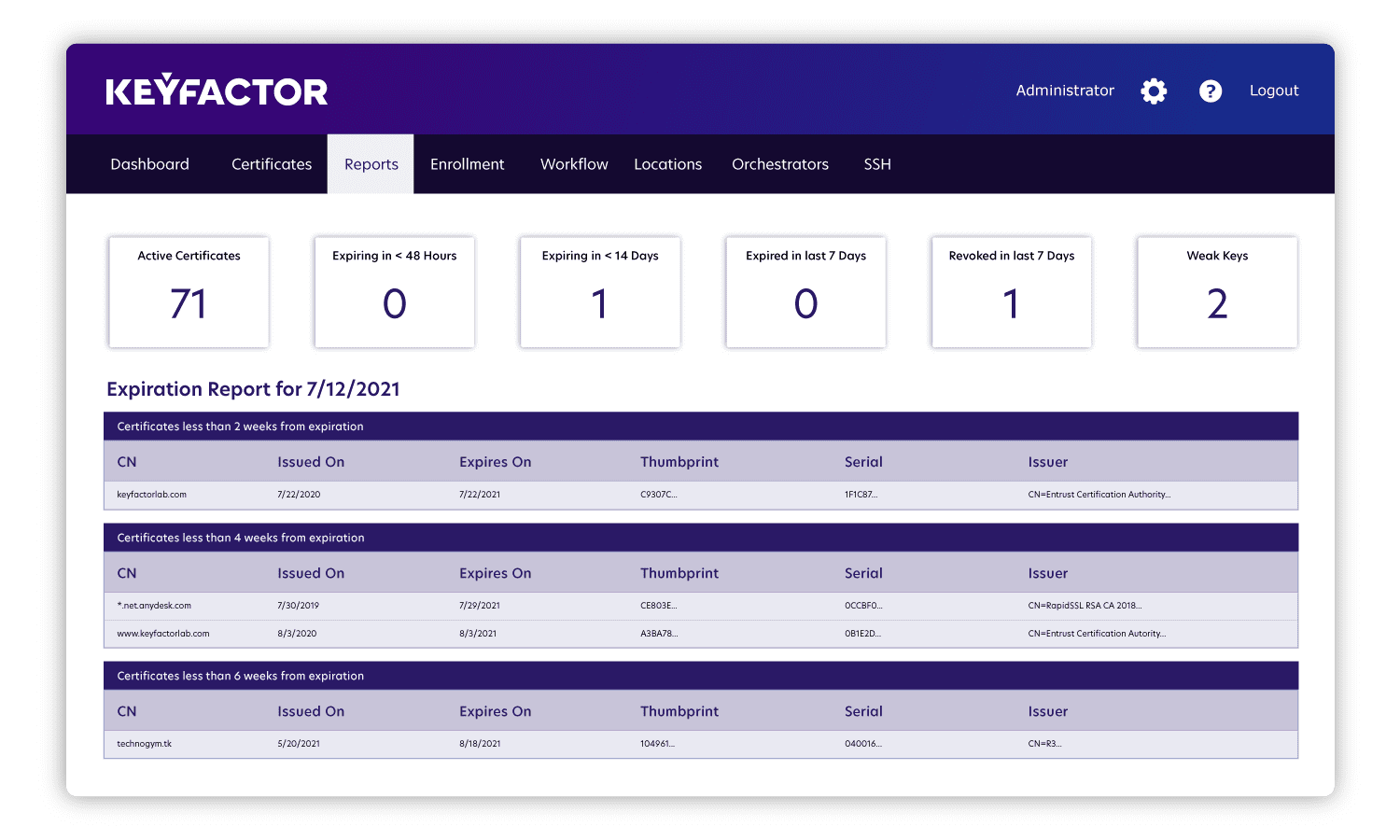
What to track: Gaining visibility into every certificate’s expiration status, including when they’re going to expire and who needs to be notified before that happens, can make an enormous difference for your PKI program. Otherwise, you run the risk of network outages, and that risk only multiples alongside the growing number of identities in the enterprise.
Why to track it: Expiring certificates are the leading reason organizations start doing certificate lifecycle management, particularly when an outage reinforces the importance of these activities.
Importantly, expired certificates can lead to more than just outages. In this example, the company had an expired certificate on a server that was monitoring network traffic. Because the certificate expired, it wasn’t reporting the data exfiltration that released customers’ personally identifiable information onto the internet. Once the company replaced the certificate (which took about 19 months past its expiration), they started seeing that theft. This is an example where the certificate didn’t cause an outage and, due to a lack of visibility into expiration status, the company didn’t immediately notice anything wrong.
How to track it: The best way to get visibility into expiration status is through a report that gives an overview of all your certificates and when they are going to expire, that way you can prioritize which ones you need to take action on. This visibility also gives you a chance to plan for the renewals that will take more time (e.g. in cases where you don’t know who’s in charge of a certificate or you don’t know how to replace it on the application that’s using it).
2) Key Size and Strength
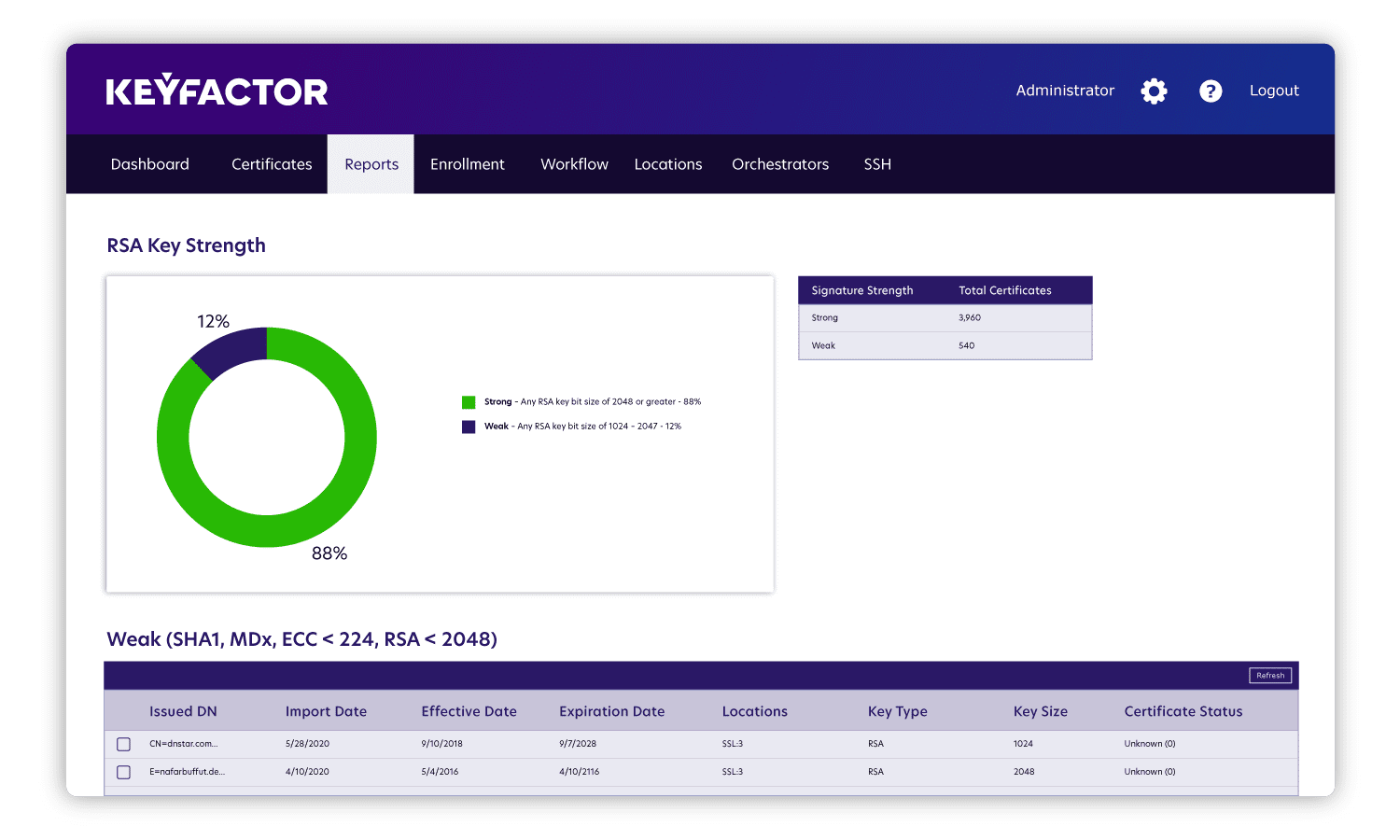
What to track: Understanding the size and strength of all your keys and certificates is also essential. Having this visibility can help you determine if your keys are weak and avoid becoming vulnerable to an attack as a result.
Why to track it: Every time we experience advances in computing, the algorithms behind cryptographic keys need to evolve. And given how often this happens, it’s important to make sure you can adapt key size and strength quickly, with minimal disruption to your existing infrastructure.
Additionally, a super weak key could indicate that you have something so old it may not even be used anymore, since a lot of applications simply refuse certificates based on such low standards. As a result, tracking key size and strength can also help identify instances of sprawl.
How to track it: The ideal report for this metric evaluates key size and strength to provide an overview of where you may have vulnerabilities. For example, is the issue that your key strength is too low or is it that you have a weak signing algorithm? The answers to these questions should offer insight into where you need to adjust your settings to maximize the strength of your keys so that you don’t have to update them again in a short time frame.
3) Signing Algorithms
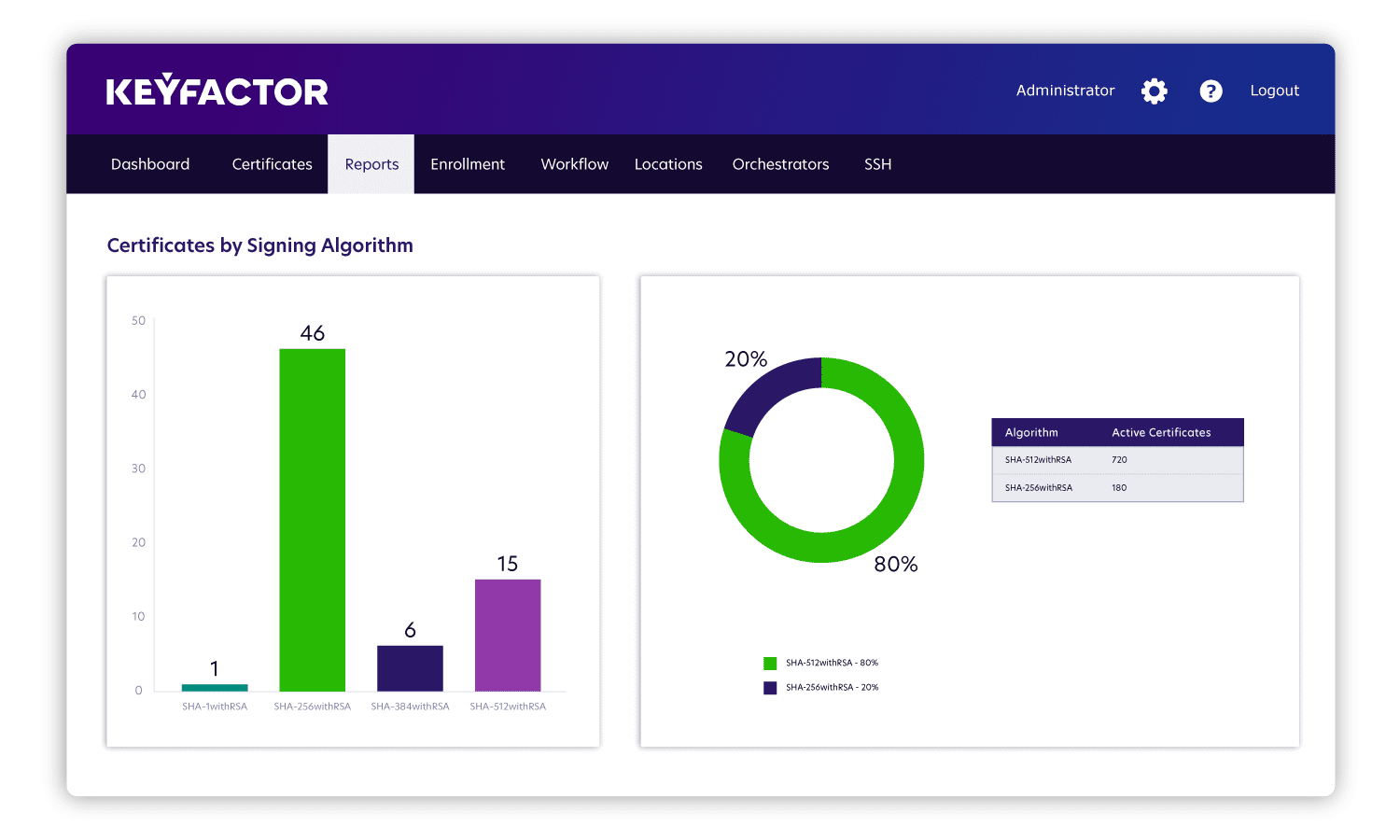
What to track: Signing algorithms are the foundation of trust and security for PKI. Similar to key size and key strength, it’s essential to track signing algorithms and prepare for migration if the algorithm will be deprecated.
A well-known example of this is the SHA-1 to SHA-2 migration. When that happened, even though the SHA-1 signing algorithm was deprecated, a lot of applications hadn’t caught up to being able to use the new SHA-2 certificates, so those migration projects required a very conscious approach based on which applications were consuming those certificates.
Why to track it: Even though larger hashes are generally more secure as they’re less vulnerable to collision attacks, the definition of larger constantly changes. For instance, right now we’re waiting for advice from NIST around quantum cryptography and quantum computing. Something could happen tomorrow that requires us to apply changes quickly, and we need to be prepared for that.
The instant that someone gets their hands on a quantum computer that can break the SHA-2 algorithms, everyone needs to reissue certificates with a much stronger algorithm. So being able to track what’s been updated and having automation to replace those algorithms quickly at scale is critical (at Keyfactor, we’ve reissued and deployed millions of certificates in 24 hours).
Interestingly, we sometimes find IoT devices designed without crypto agility in mind because the certificates have 20 year lifespans and any updates require manually going to each device and replacing the certificate. Not only is that a huge cost, but the changes in algorithms over time will leave those devices extremely vulnerable.
How to track it: The most helpful reports look at how many applications have been migrated, how many haven’t been migrated and what’s needed to get those remaining ones migrated. In cases like the SHA-1 to SHA-2 migration, which centered around applications’ inability to consume the updated signing algorithm, this report is also valuable in helping application owners understand what security updates they need to make.
4) Certificate Authority (CA) Issuance
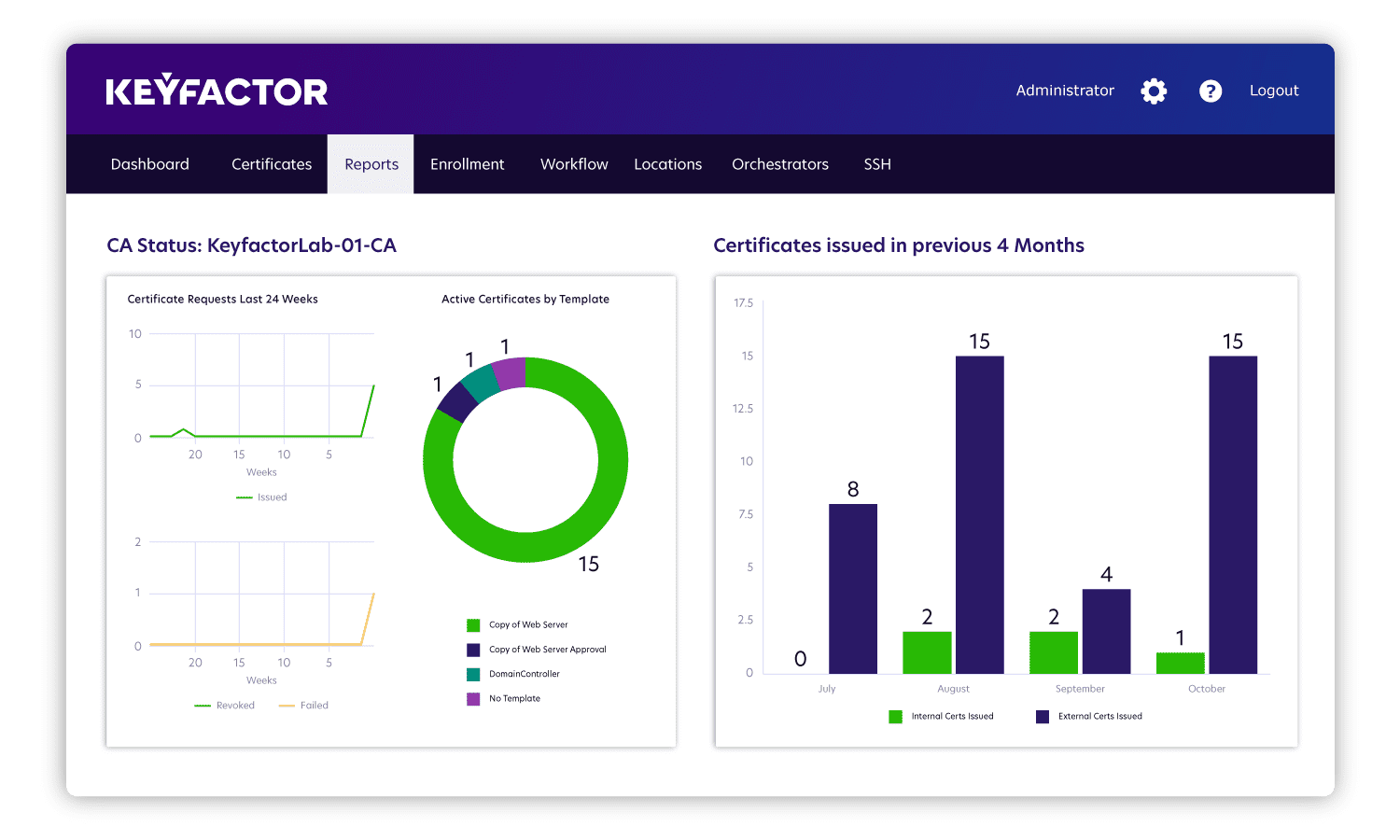
What to track: It’s essential to know all of the certificate authorities (CAs) your organization uses (both public and private) and to keep tabs on the certificates that they issue. Many teams are in charge of three to four public CAs that integrate across the entire company as well as an internal issuing CA. With all these CAs in play, you need an overview of activities at any time.
Why to track it: Visibility into CA issuance is important to detecting any unusual, ominous or hidden activity. For instance, one organization thought they had 1,000-2,000 certificates, but a Keyfactor inventory scan found more like 200,000 certificates. We discovered a server in the environment was rebooting every six hours, and whenever it rebooted, it requested a certificate — and this had gone on for two years without anyone noticing.
How to track it: A report can show you the number of certificates that each CA issues daily, providing visibility to pinpoint trends and get ahead of any issues. If your team expected to issue two or three certificates a day but then you see triple that activity, you can identify which CA is causing the spike and investigate further, since this could indicate malicious activity. Overall, seeing those spikes and anything else out of the ordinary is a great indicator that something might be wrong and warrants a closer look.
5) Certificate Requesters and Owners
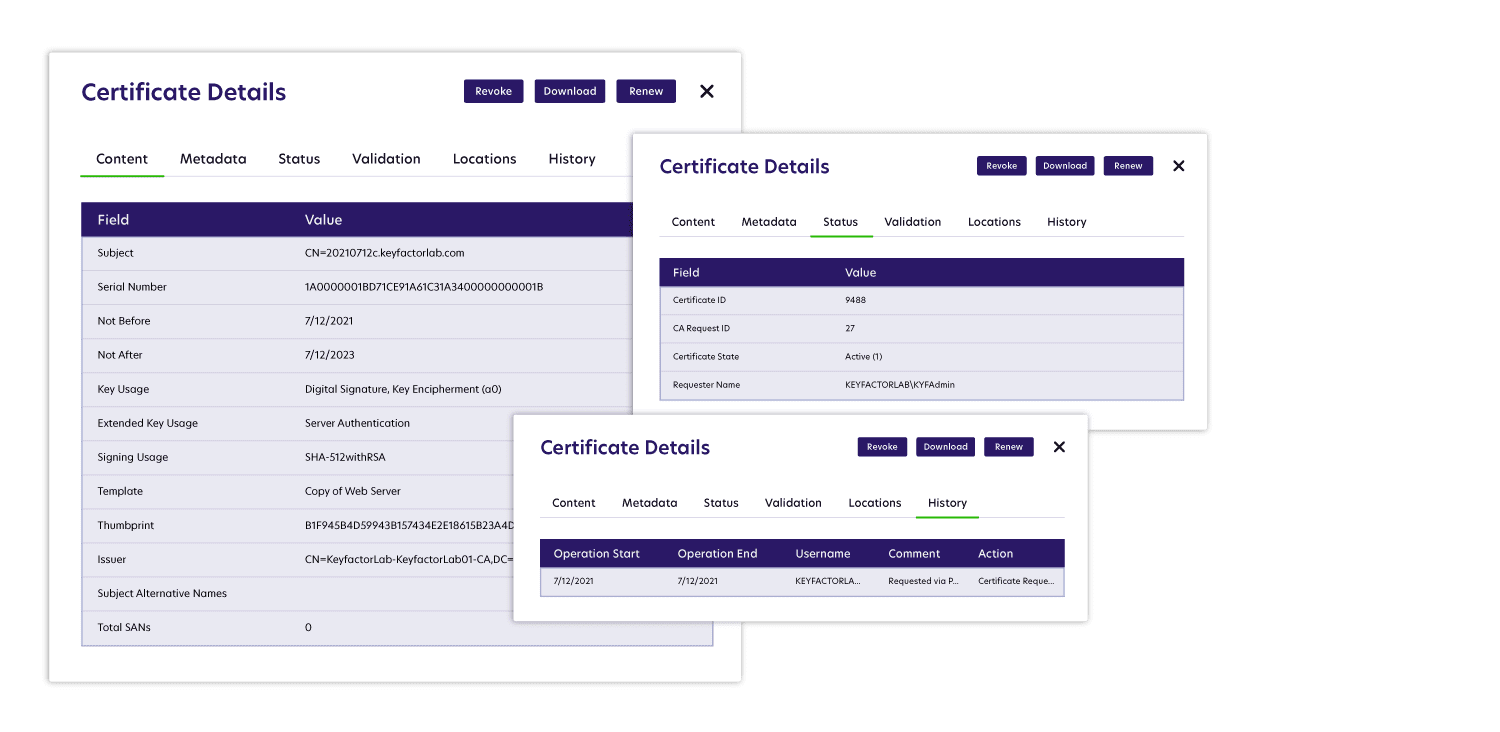
What to track: Next you need to know who is requesting certificates and who owns those certificates. Although this sounds simple, handing out certificates can get unwieldy very quickly, becoming like that classic Oprah moment “you get a car and you get a car!”
Why to track it: You need to know who requested a certificate and who owns it because when there’s a certificate expiration or operational downtime, you need to know who to go to for the renewal. Typically when outages happen it’s because someone wasn’t paying attention to a certificate or there was no renewal process in place.
And it only takes one certificate to cause an outage, such as the Microsoft Teams outage that happened shortly after COVID hit. It was just one certificate that expired, but it was a huge hit to Microsoft at a time when Zoom was starting to become dominant.
How to track it: The best way to track certificate requests and ownership is to introduce a report that offers a detailed view of who requested a certificate, who owns it, where it is and who to notify about an upcoming expiration and renewal.
6) Self-Signed Certificates
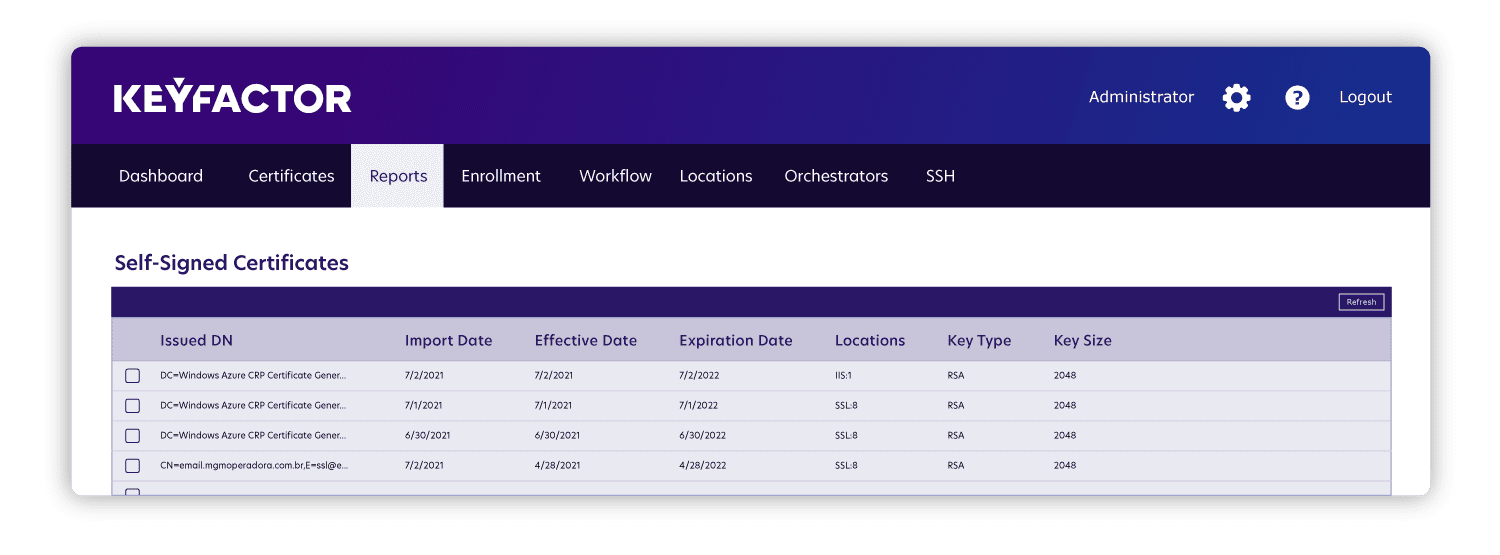
What to track: As DevOps teams grow, most organizations see a rapid increase in self-signed certificates put in place by the engineering team to keep up with the faster pace of development. A self-signed certificate is one that is not really public or private — it’s basically an onboard CA that’s attached to a certain tool, and it’s critical to understand where they exist.
Why to track it: Many organizations try to figure out how they can make self-signed certificates compliant with their PKI policy. Often they go about this by integrating their PKI program with HashiCorp Vault or a CA on their Istio service mesh. These integrations can get out of hand fast, but they do show exactly where the certificates are. Otherwise, security teams likely have limited to no visibility into where the engineering team issued self-signed certificates.
How to track it: This type of shadow IT primarily exists when certificates are cumbersome for developers to obtain. What you need is a report that shows who is going around your policies and when. Then you can use that insight to identify ways to improve your processes to make it easier for them to get certificates securely without slowing down their processes.
7) Wildcard Certificates
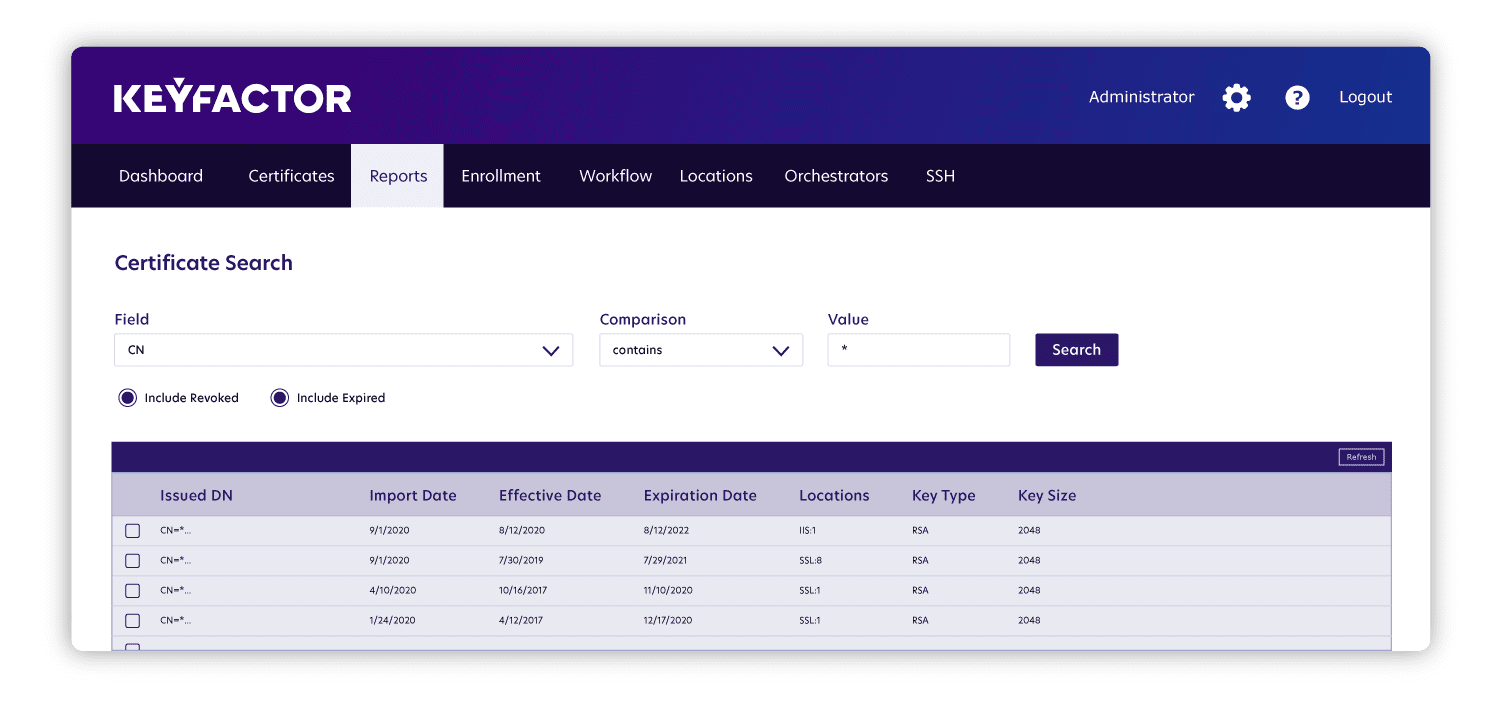
What to track: A wildcard certificate is a single certificate that’s used on multiple subdomains. They provide a lot of cost savings, but a single point of failure with the certificate can affect multiple areas of the business. This presents a huge risk in terms of outages and attacks.
Why to track it: If you don’t know which certificates are wildcards or if you don’t know every application using a certain wildcard certificate, you’re left with a blindspot. Specifically, if something goes wrong with that certificate or you need to renew it, you’ll have difficulty identifying everything that could be affected. This recently happened to Spotify, when the entire service went down because the team forgot to renew a TLS certificate that was a wildcard.
How to track it: You need a report that tells you which certificates are wildcards and the subdomains to which each one is attached. The best way to do this is to mark any wildcard certificates in a certain way, for example with an asterisk. Without this type of report, you might not know that a certificate is a wildcard. Or even if you do, you might not know every application consuming the certificate, and the only way to identify that is through manual network scans.
8) Automated vs. Manual Certificates
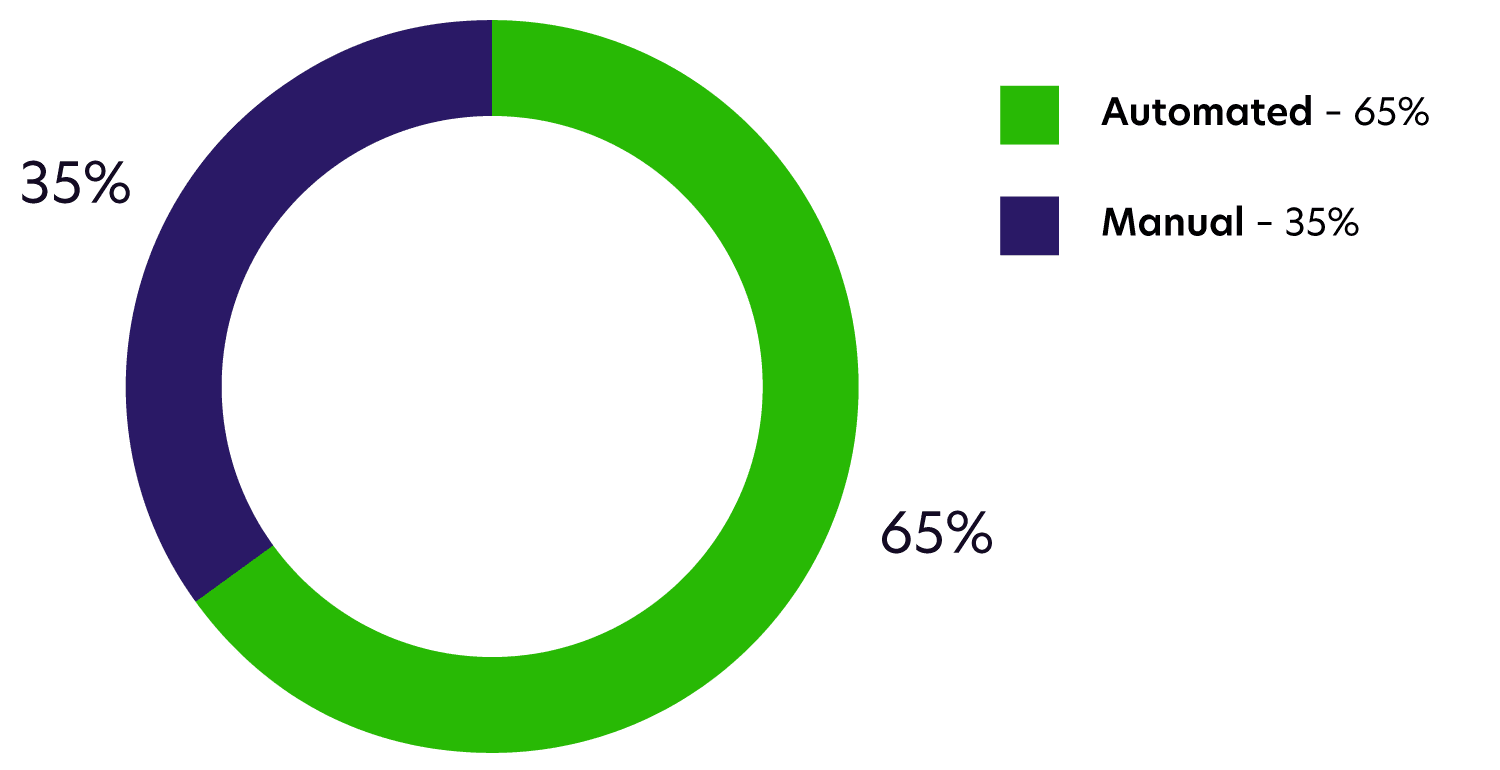
What to track: Which certificates have automated deployments and renewals and which certificates require manual updates? Generally, the more automation the better.
Why to track it: High automation allows for a more dynamic approach to your PKI operations and certificate management practices, whereas lower the automation leads to higher risk for outages. Further, automated certificates help with the default 90 day lifespan of certificates, as you don’t want someone to have to replace those certificates manually every 90 days.
How to track it: First you want a report that shows which certificates are automated and which are manual. Going one layer deeper, the nice thing about automation is that it will also create reports that show you how many certificates are getting renewed. This will display the lifecycle of certificates, so you can even get them replaced earlier than needed.
9) CRL Health
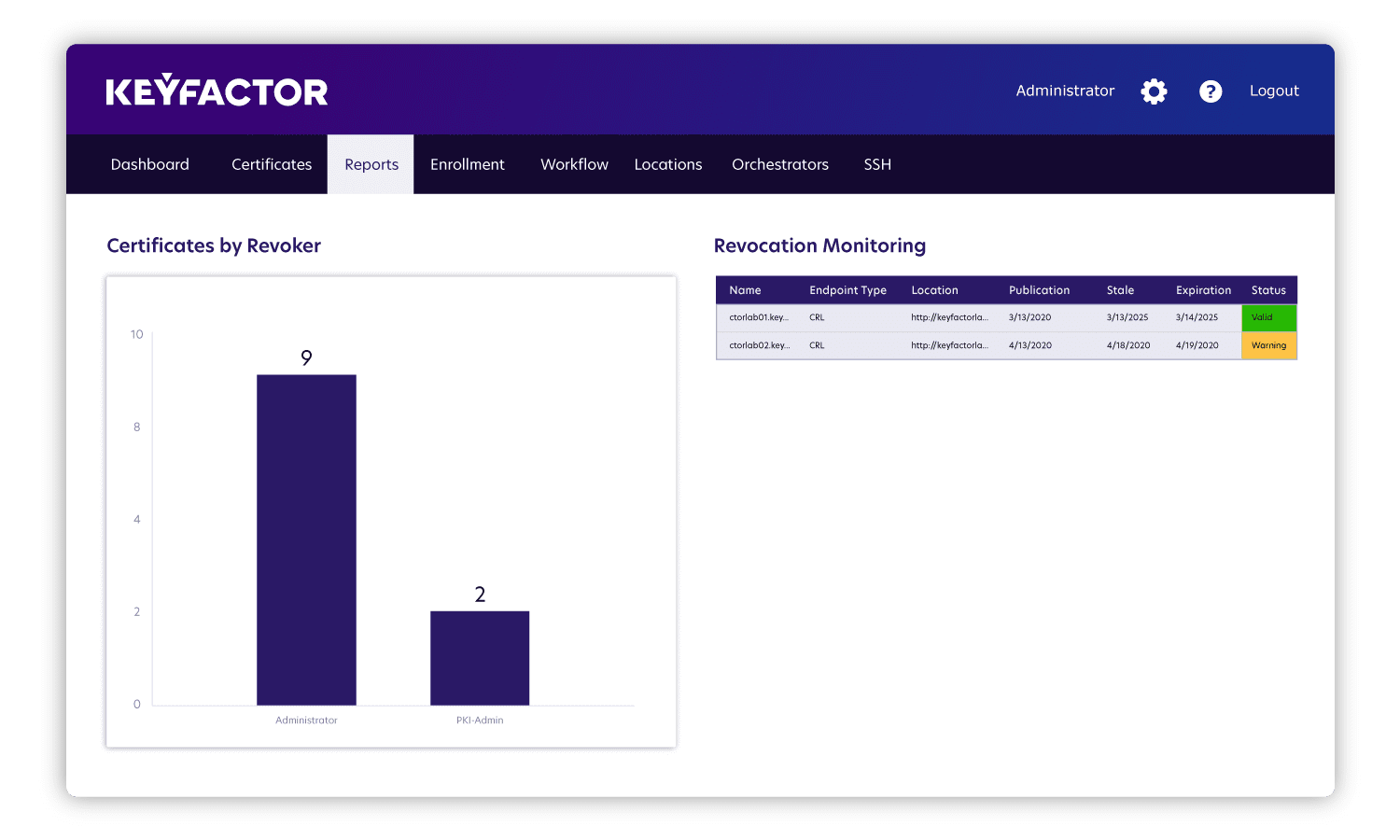
What to track: Certificate revocation lists (CRL) tell you whether or not a certificate is still valid, and they sit at the crux of PKI management. For example, if someone leaves your company, you might revoke their certificates, and a CRL makes that known so that others don’t trust those certificates anymore.
Why to track it: The CRL lives in a public place where anyone can check it. If for some reason a person or service can’t reach it, then they should not trust a certificate. So if the CRL is expired or unavailable, every certificate issued from that CA will be considered untrustworthy. As a result, CRL health is a single point of failure and needs monitoring.
How to track it: Introduce a report that shows which certificates have been revoked and add the ability to see who’s revoking those certificates. It’s important to note that certificates can be revoked for all kinds of reasons: They might be compromised, they might not be needed anymore or they might have been superseded.
10) Unknown Certificates
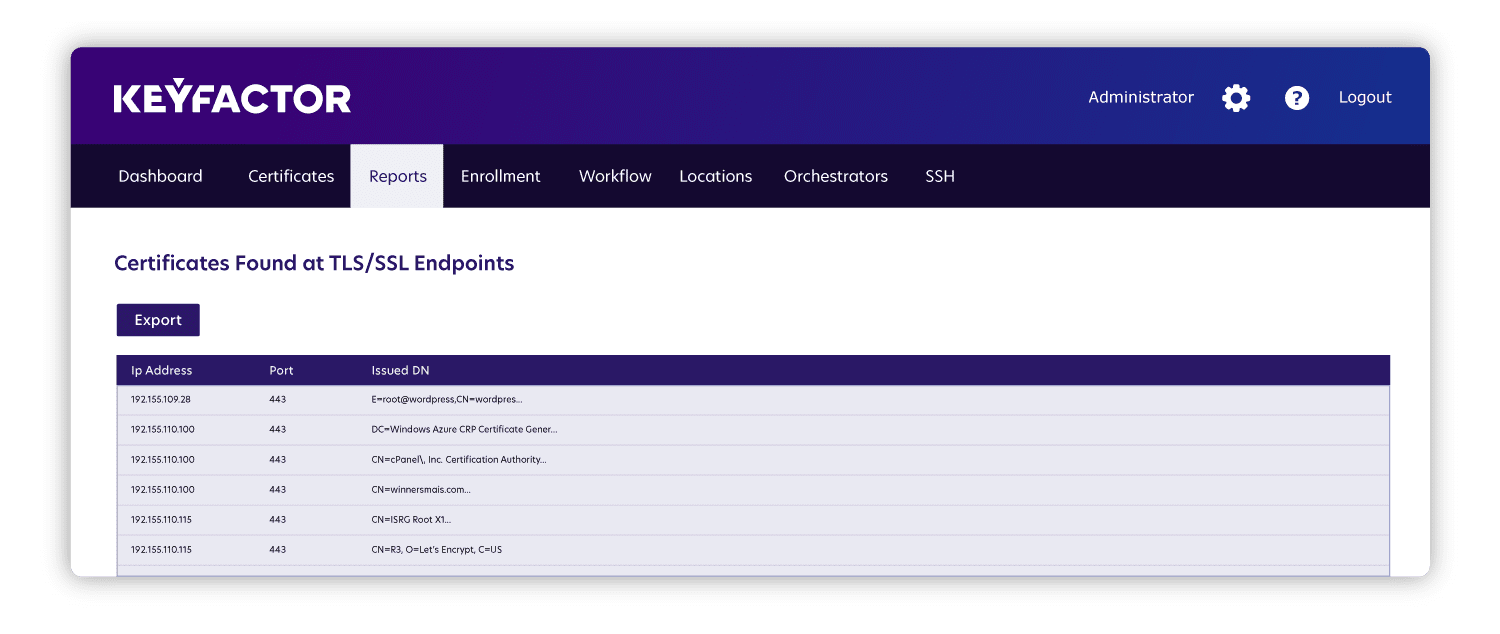
What to track: The previous metrics are all things that you can easily find by scanning your network or scanning different endpoints. The last one involves finding all of the certificates in your environment that you don’t know about, that way you can bring them into your database to eliminate blindspots and allow for reporting.
Why to track it: Before you can scan certificates to get specific information on them, you first have to know every single certificate that’s out there. What’s worse than not managing a known certificate is not managing an unknown certificate, and that makes it essential to have a complete inventory of all the certificates that exist.
How to track it: Scan your environment for all the ports that you have open that could be hosting certificates. If you know where certificate stores are, even if you just know the server name, you should be able to configure automation or an orchestrator to crawl that server and look for certificate stores. Then you can bring everything you find into one single database that you can report on. As you do so, look for things like a misspelling in your company name on a certificate, as that could be an indication of malicious activity.
Pulling it All Together
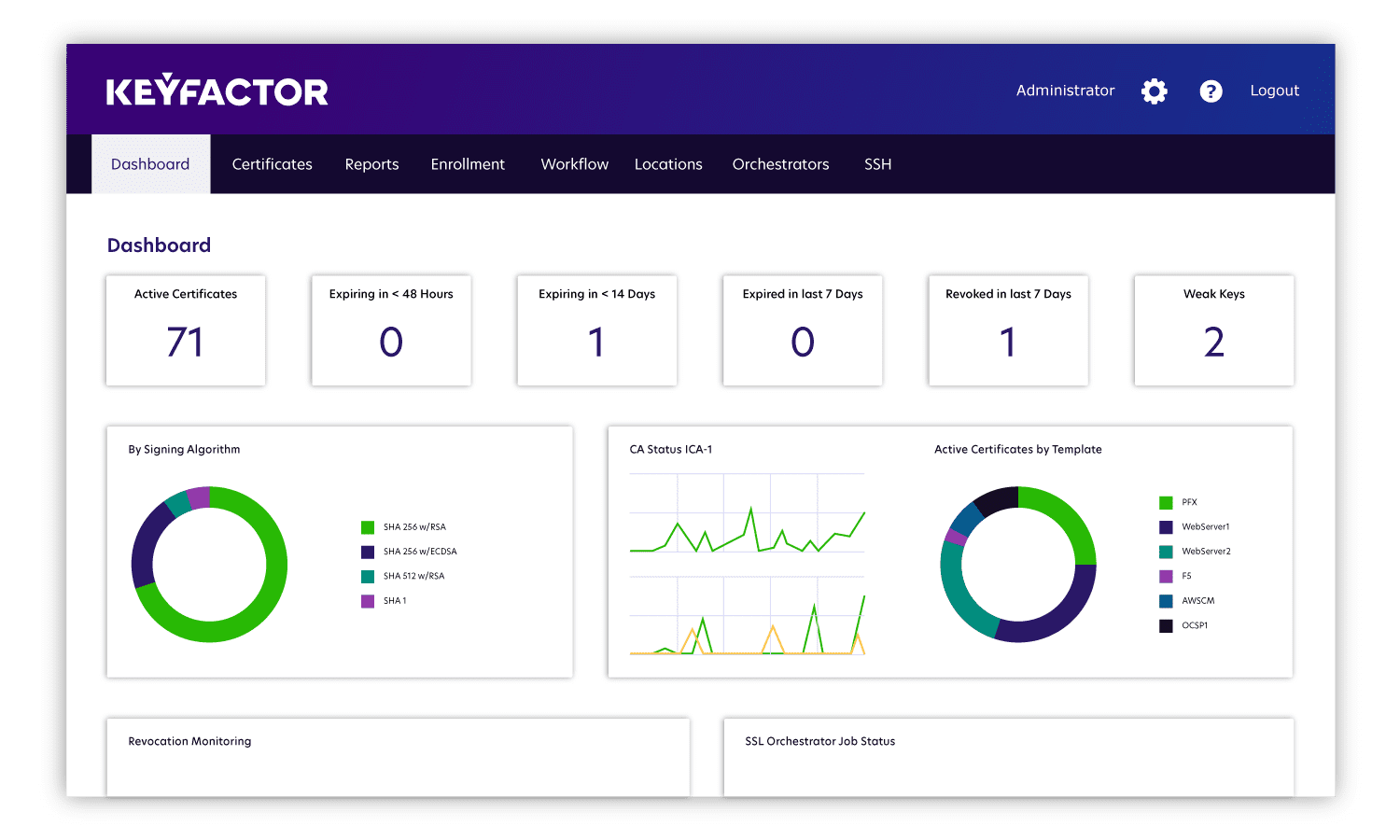
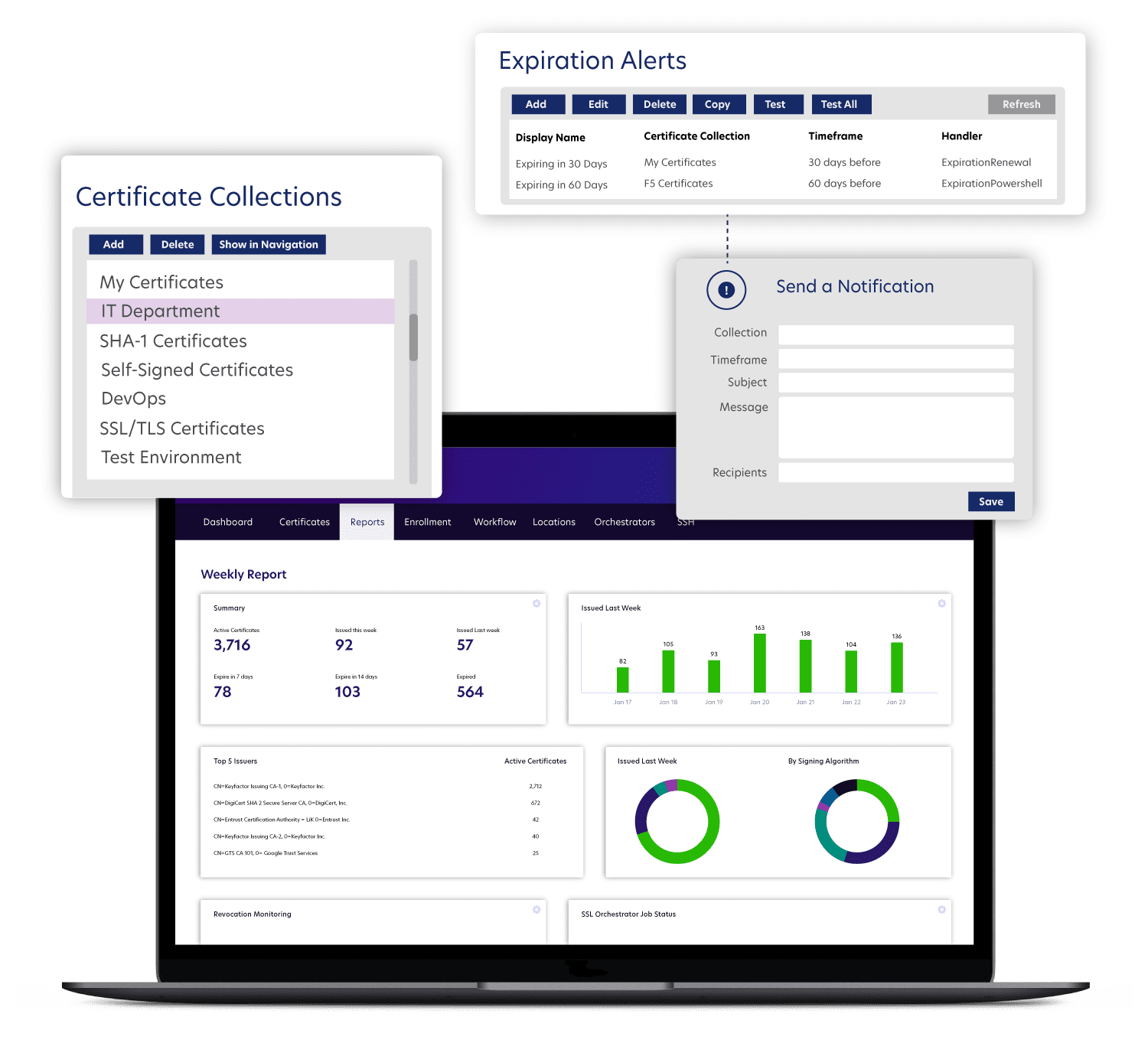
While these are only ten of many PKI metrics to track, together they provide a great deal of visibility that can help your team achieve crypto agility. So what’s next? It’s time to pull everything together for easy viewing. We recommend starting with the following dashboards:
- Monthly Executive Report: Give executives a glance into issuance activity over the past month compared to the previous month. This provides a quick peek into the health of the CA, and it allows executives to quickly see if there are any red flags that need investigating (such as a large number of certificates set to expire in the next 2-4 weeks that could present a risk of outages). It also helps executives understand what to plan for when it comes to scaling the PKI architecture. For instance, do you need to stand up another issuing CA to take care of an increased load of certificates?
- PKI Status Report: Create a birds-eye view of PKI health metrics, like issuance, expirations, key strength and CA activity, for the more technically-minded executives. This gets into more detail while still providing an at-a-glance view of everything going on. It should also allow you to filter things like certificate collections by departments and to view or adjust expiration alerts. Overall, it provides a nice overview for a busy executive that understands the value certificates bring to the security of the organization and allows them to plan for improvements, like introducing more automation to reduce risk and free the security team’s time to focus less on renewals and more on value-add activities.
Interested in learning more about why these metrics are so important and how to get started tracking them? Click here to watch our webinar on the top ten PKI metrics to care about for even more details and advice.