PKI now plays a critical role in our everyday lives, and that’s why it’s no surprise it’s been a recurring theme at PrimeKey Tech Days since 2015.
Tomas Gustavsson, Chief PKI Officer at PrimeKey Keyfactor, has led this topic annually, personally selecting the most hardcore PKI topics to feature in each discussion. And 2021 did not disappoint. Here’s a look at the highlights from his 2021 talk on hardcore PKI.
Covid Certificates
Covid certificates and the concept of tweaking standards were actually on the hardcore PKI agenda in 2020 as well. But much like with what’s been going on in the world, a lot has happened in the past year that made it worth revisiting this topic.
To start, it’s important to note that these are not x509 certificates like we typically discuss in the PKI world, but usually a ISO9000 or ISO27001 certificate. In fact, there are several different standards emerging in this area from the EU, WHO, ICAO, and more.
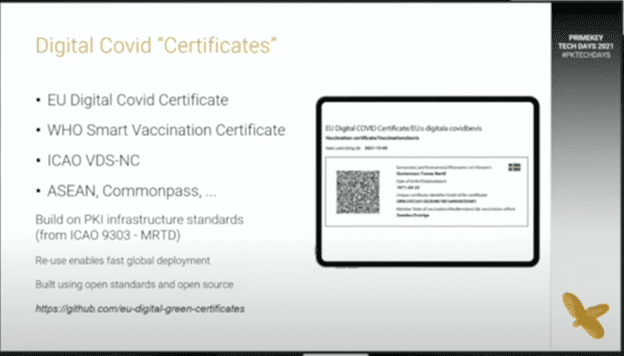
The teams behind these digital Covid certificates have moved fast on development and global deployment, and they were able to do so in large part for two reasons. First, because they built on already existing standards and models that are robust and well-tested, and second, because many also use open-source code accessible through Github.
Let’s dig into two examples of how this plays out.
ICAO Visual Digital Seals (VDS)
ICAO VDS builds on ICAO 9303 Part 12 for its PKI infrastructure, which is a country-signed CA that has previously been used to issue documents like passports and eIDs. Most recently, it added capabilities for a barcode signer. ICAO is currently working on personalization and constructing 2D barcodes with a digital seal, but the fact that they started with this well-established and trusted infrastructure represents a huge step forward in the development process.
EU Digital Covid Certificate (EU DCC)
The EU DCC takes a very similar approach to ICAO VDS from a PKI perspective, reusing the same robust and well-known concepts from ICAO 9303, which has made it relatively easy for many countries to deploy. However, the EU DCC takes a slightly different approach for constructing the 2D barcodes by inserting a signature in the middle of them. They have developed open-source code available via Github for the process of creating data and verifying the signatures, which has also helped them deploy faster.
(I)IoT Standards
Next up, IoT standards — or IIoT (Industrial IoT) standards as the case may be — also revisits some themes from 2020, but managing these standards remains a challenge as the verticals that rely on them continue to grow rapidly.
Specifically, the industrial space takes security very seriously and the critical infrastructure market is highly regulated, which has put a lot of pressure on developing these standards. From a PKI perspective, this has led to an explosion of RFPs and RFIs to come up with new standards, but most organizations still don’t have a strong grasp on what’s most relevant in these standards.
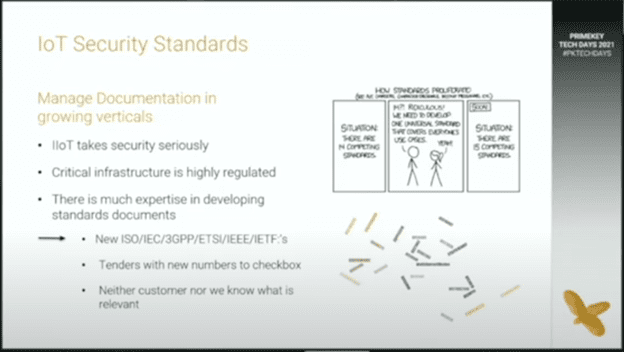
For example, let’s look at an electricity metering data exchange that uses the IEC 62056 standard. If the standard has 24 parts and you don’t know which part is relevant for PKI, then you have to go through all 24 parts to document compliance.
Ultimately, this leads to more protocols and more protocol modes, new CA types and more complex profiles with “more options” — creating even more choices and more to manage when developing and adhering to these standards.
Complex Ecosystem Integration
When you want to integrate fully into an ecosystem, it can end up becoming quite complex in certain cases, and that earned it a spot on the list for hardcore PKI this year.
One thing that always comes up when you develop a new complex system or start integrating into an ecosystem is that you can develop the initial concepts and functionality fairly rapidly, but once you move into production, each set of users wants to do things differently and suddenly you have numerous new details and use cases to consider.
This type of integration is something our team has been working on a lot in the past year to be able to fully support and merge into a Microsoft ecosystem (although it is helpful that Microsoft has a reference implementation you can mimic, even if it is quite detailed).
When it comes to the Microsoft ecosystem integration, our team has had two main focus areas over the past year: Native Microsoft auto-enrollment and Azure Intune enrollment support.
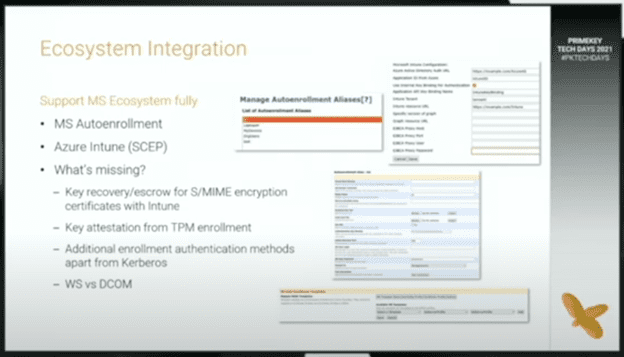
Here’s a high-level look at what’s been involved:
- Microsoft auto-enrollment: Our team has been working to add Microsoft auto-enrollment using the web service API. This includes EJBCA aliases that allow for multiple configurations to support multiple domains and, therefore, run multiple CAs in the same instance.
- Azure Intune enrollment: We’ve also been adding Azure AD parameters to support requests for Azure Intune enrollment either directly or through a proxy.
- Additional elements: Once we started moving into production, users started to request functionality beyond the areas in which we started. This has led to a few additional elements we’ll work toward:
- Key recovery/escrow for S/MIME encryption certificates with Intune
- Key attestation with TPM modules
- Additional enrollment authentication methods apart from Kerberos, such as client certificates or username/password
- Introducing DCOM for certain use cases that require the older API (versus the web service API, which covers about 90% of the use cases)
Hardware Security Modules
That brings us to our last hardcore PKI topic: Hardware security modules (HSMs), which were part of the hardcore PKI discussion in 2018 and 2019 as well.
HSMs made a reappearance this year because we found that the trusted Java PKCS11 that we’ve used for decades is no longer agile enough to support security for modern HSMs. Specifically, it doesn’t provide enough control.
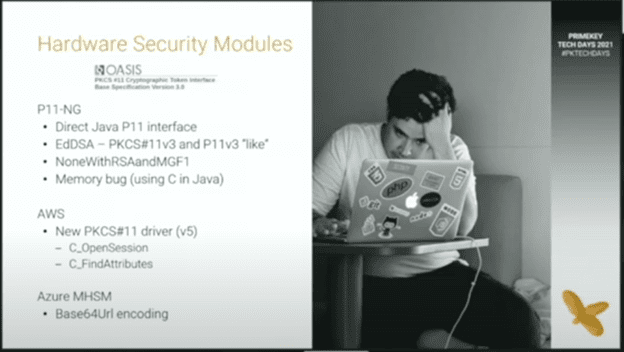
In response, our team has been working on how to increase control and support a large number of signature keys within the HSM. We’ve been doing so through a direct Java P11 interface which also enables us to support EdDSA, which is a PKCS#11v3 feature. Importantly, support for EdDSA can today look a bit different depending on which HSM you use, since many vendors started to support it before the PKCS#11v3 standard was officially specified.
At the same time, we’re also seeing cloud HSMs become very popular, despite the fact that many people were skeptical when these externally hosted HSMs first started to emerge. Now, however, organizations are starting to feel much more comfortable with cloud hosting and have found several benefits in the ease of use of a cloud HSM.
Bonus: What didn’t make the “Hardcore PKI” cut?
Last but certainly not least, there are some topics that didn’t make the cut for hardcore PKI, not because they’re uninteresting, but just because they’re not “hardcore” enough. Here’s a quick look at these runners-up:
- Product pipelines: We’re working on an example using containers as building blocks to deliver source code into a full user product.
- Supply chain attacks: Secure software development lifecycles have been a very hot topic in the last year.
- Digital sovereignty: This means different things to different people, but it’s often associated with the use of open-source frameworks
Interested in Learning More?
The idea of “hardcore PKI” isn’t going anywhere anytime soon — PKI is a complex and ever-changing concept, and because of that we’ll continue to encounter new challenges and new ways of doing things as the technology evolves.
Interested in learning more about the topics that made the cut this year? Click here to watch the full session on Hardcore PKI featuring Tomas Gustavsson from PrimeKey Tech Days 2021.




