Digital trust is essential to the security of every connected thing, from connected pacemakers and printers to transportation and critical infrastructure. And as the use of these IoT devices continues to explode, understanding trends in digital trust has never been more critical.
With that in mind, Keyfactor and Vanson Bourne partnered on a report, Digital Trust in a Connected World: Navigating the State of IoT Security, which draws insights from 1,200 survey responses from two unique perspectives – those who design and manufacture connected devices/products (OEMs) and those who deploy and operate connected devices/products within their organization.
Ready to dig into the data? Ellen Boehm, SVP of IoT Strategy and Operations at Keyfactor, and Mitch Mershon, Product Manager for Emerging Markets at Keyfactor, sat down to discuss key findings from the report, including trends in IoT device identity and management, the prevalence and impact of security breaches, and the impact of industry standards on product development. Read on for a recap of their conversation, or click here to watch the webinar.
Establishing digital trust: Trends in IoT device and identity management
First and foremost, it’s essential to start with the building blocks of digital trust: Every machine needs an identity, and every identity must be managed.
Traditionally, we think about identity management from the enterprise perspective, meaning server racks, laptops, and other devices on a corporate network. But we now live in a world of smart, connected devices that extend everywhere and to everyone, and each of those IoT devices needs an identity because each one represents an attack vector.
These modern devices can also be very complex, in some cases even a machine of machines. Think about a car or a plane – each has many different components with its own operational networks that can connect to the corporate network. In these cases, we have a machine with multiple identities inside it with its own broader identity that connects into a system.
So, how exactly does all of this work? First, you have manufacturers, designers, and developers that make an IoT device, whether a wind turbine, a train, a drone, or anything else. These OEMs handle efforts like security design, testing, certification, and identity provisioning. Once the device is produced and sold, it’s deployed into a facility such as a factory, hospital, or utility grid, where operators take over and manage service deployment, device health monitoring, and end-of-life decommissioning. Fortunately, both teams’ budgets for IoT device security will continue to increase year over year. According to our report, leaders expect a 45% increase in the next five years, which shows that IoT security is a priority investment for companies because they understand the risks it can have on the business if done incorrectly. However, 52% of that budget could be at risk if it needs to be diverted to handle cleanup after the fact, such as in the case of an outage or a compromise. This is notable because cyber attacks are on the rise.
Understanding risks: The prevalence and impact of security breaches on IoT devices
Security breaches are increasing, and no one is exempt: Nearly every company has already experienced a cyber attack and those that haven’t likely will in the near future. In fact, 89% of survey respondents said their organization’s IoT products have faced a cyber attack in the past 12 months, and 69% said they have seen an increase in attacks on IoT devices over the last three years.
The reason for this increase? IoT is being used everywhere: Survey respondents report a 20% increase in IoT device usage over the last three years. More devices mean more identities (both broader identities for each device and all of the identities for smaller machines contained within it), which multiplies the number of attack vectors.
For example, manufacturing used to be a tight, close-knit system, but now all the new machinery is connected with different sensors within each unit. Each of those sensors, plus the machinery at large, is an attack vector. Or consider the case of supply chain management, where one company talks to another and another and another, creating a chain. In both cases, operators must ensure they can trust every single identity and communication along the way to secure against attacks, even from seemingly innocent devices like an HVAC unit.
And the cost of these attacks is nothing to blink at:
- $236,000 is the average cost that companies have paid as a result of a breach in the past year because their IoT devices were able to leak data or someone was able to get in through a device into the network. Considering that number is from one year, it’s easy to imagine how that starts to add up over time.
- $2.3 million is the average cost for a certificate outage on a manufacturing line, meaning if a connected device tries to call a server, but the certificate is invalid, the factory line can no longer produce until the issue is fixed.
It’s not just about money, either. According to respondents, the top concerns following a cyber attack include external reputational damage, losing customer data, employees losing confidence in the organization, regulatory fines, and revenue loss.
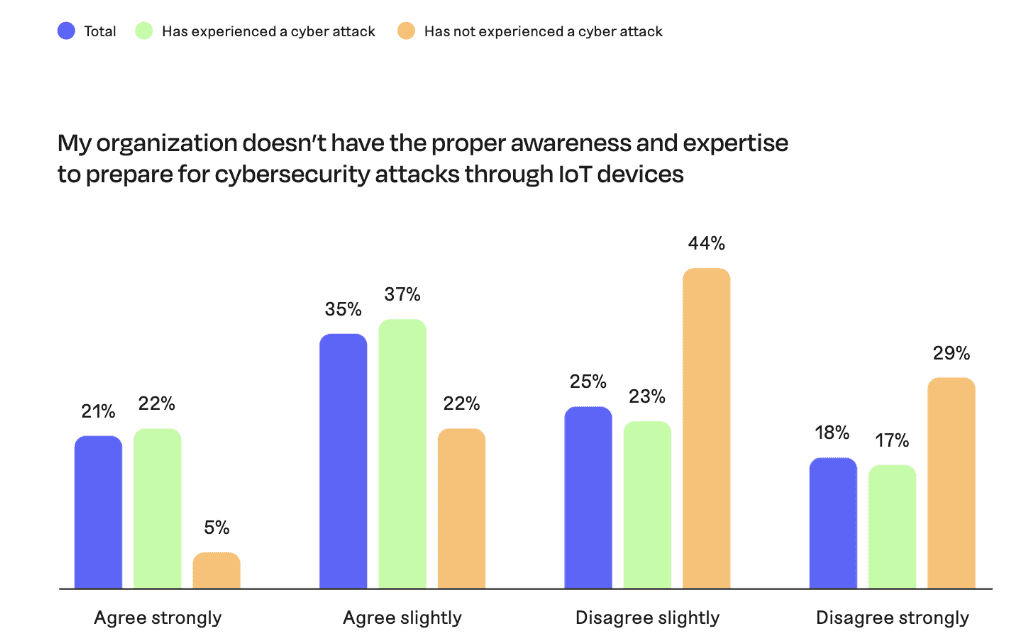
Across the board, survey respondents agree their IoT security needs improvement (88%) to protect against these risks. That said, 47% of respondents feel they’re already doing everything they can to protect their organization. Looking more closely, 56% of respondents agree their organization doesn’t have the proper awareness and expertise to prepare for cybersecurity attacks through IoT devices. That number jumps to 59% when looking only at organizations that have already experienced a cyber attack, compared to 27% among organizations that have not yet experienced an attack.
Fortunately, even though attacks are rising and security is challenging, protection is possible. It requires having complete visibility into IoT devices and their identities, including the ability to quickly find those identities as needed and automate lifecycle management activities so that devices don’t go down and everything stays operational, even as certificates expire or become compromised. It also requires partnering with a company that has the proper expertise in IoT security to fill in potential gaps on the internal team.
Embedding security from the start: Top trends for OEMs to take responsibility for IoT security
Narrowing in on OEMs, in particular, three trends stand out when it comes to IoT security:
1. Security must be at the heart of product design: OEMs understand that having proper security architecture from the beginning of product design is just as important as the electronics, functionality, and the software itself. That’s because if security isn’t done correctly, it becomes impossible to do things like send secure firmware updates remotely, activate new features, or upsell customers. As a result, more manufacturers are considering security from the beginning.
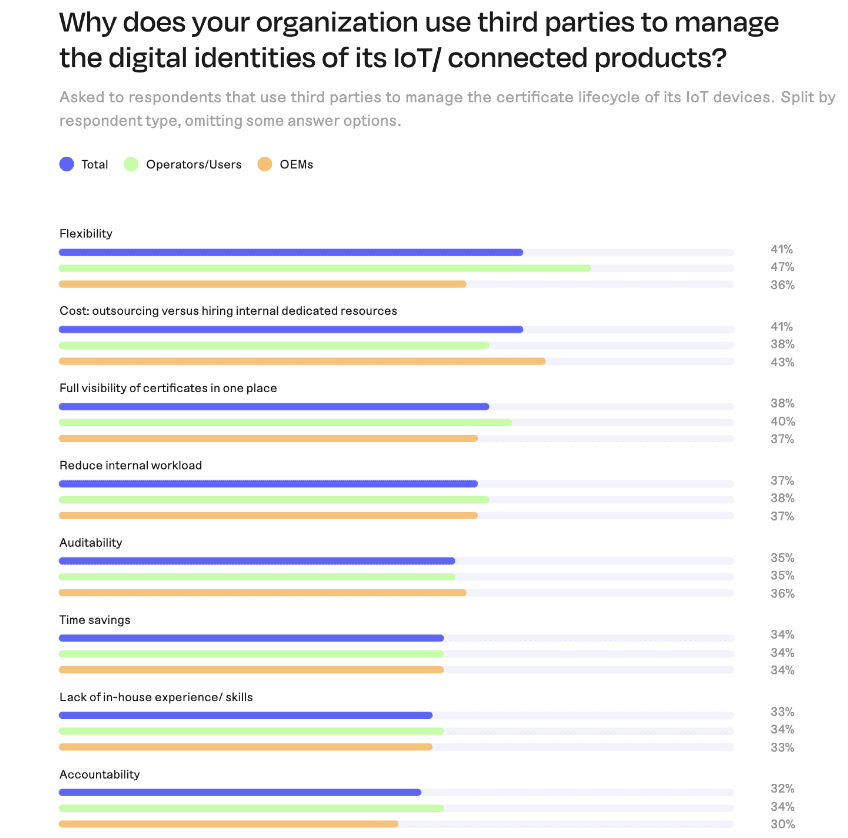
2. Third-party partners provide the expertise to implement security effectively: We’re also seeing more collaboration within the ecosystem as manufacturers realize they don’t need to develop everything from scratch. Now, OEMs are looking to implement best practices from across the field and work with expert partners to implement the best security possible. This approach is also essential as manufacturers think about how technology will change and how they can make their designs flexible enough to be used in the field for 10-15 years. According to respondents, the top reasons to partner with third parties include greater flexibility and cost from a resourcing perspective, the ability to gain complete visibility into hundreds of millions of device identities, and reducing internal workloads around a highly niche skill.
3. Security doesn’t end when the device rolls off the line: Security is not just about what the device looks like when it’s first produced. Rather, OEMs are responsible for security for the entire lifetime of the device. Think about a software update on an iPhone: When a user clicks “install,” the phone first validates that the firmware has a certificate. It does a signature verification before installing anything to know where the update is coming from and that it can be trusted. This ongoing verification is essential to security.
All of this is especially important because as much as anyone can prepare for a secure experience, breaches happen. And when there’s a breach on an IoT device, more than 70% of respondents believe at least some level of responsibility falls on the manufacturer.
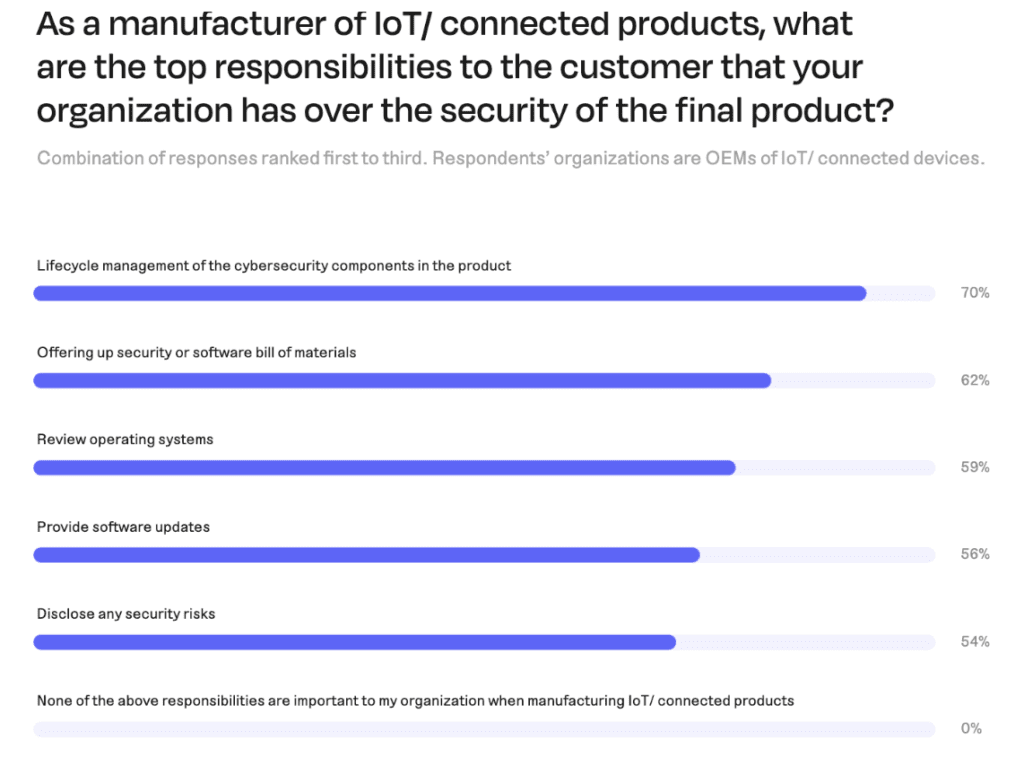
With that in mind, OEMs view their top responsibility (among many) as lifecycle management of cybersecurity components within products. Other important responsibilities include sharing a security or software bill of materials, reviewing operating systems, and providing software updates.
Adopting industry standards: The impact of regulations on IoT product development
Even with all the progress manufacturers and operators are making regarding IoT security, there’s still a lack of clarity around best practices. And that’s mainly due to the fact that regulations vary significantly from one country to another. Keeping up with these standards is another reason why partnering with third-party experts benefits OEMs.
Looking at the big picture, standards are becoming more common and having a much more significant impact on product development. For example, Matter’s open-source connectivity standard for smart home and IoT devices is one of the most recognized standards to come together over the past several years. The automotive industry has also led the way with various regionally-based standards.
Regardless of the industry, many manufacturers must make changes to meet these standards. If they don’t, they either can’t sell their product due to governmental regulations, or they’re missing out on part of the market thanks to consortiums like Matter. The fact that these regulations can now impact sales and market fit – not to mention that end users are starting to expect products to meet specific standards – has forced manufacturers to adjust how they do business, and that trend will only continue.
IoT security is evolving: OEMs and providers must keep pace
The state of IoT security has changed tremendously over the past several years, and we’re now reaching a new level of risk.
As IoT devices become so much more prevalent across the entire world, they’re increasingly becoming attack vectors. At the same time, both manufacturers and users admit that they lack the proper expertise to secure these devices. Already, this situation has led to severe ramifications from breaches that extend well beyond immediate financial impacts, such as reputational damage and audit risks.
In response, OEMs and providers must prioritize IoT security by embedding it from the beginning and partnering with experts who can help fill gaps in knowledge, maintain proper awareness, and adhere to new and changing standards. When that happens, organizations will be well on their way to protecting against these increasing risks.




