Digital trust is the backbone of any technology, but as connected devices find their way into every facet of life, that trust has become non-negotiable.
But who owns that security?
Keyfactor’s first global IoT report surveyed 1,200 professionals across North America, EMEA, and APAC, representing organizations in manufacturing, IT, telecom, energy, oil and gas, retail, construction, financial services, and many more.
These respondents were evenly split between organizations using IoT devices and the manufacturing organizations building them. The report takes an in-depth look at what methods and priorities OEMs are leveraging to optimize their IoT and connected products and navigate the obstacles of risk and costs.
OEMs are embracing responsibility for securing devices but believe it should be a joint effort

48% of respondents believe the manufacturer of IoT or connected devices should be mostly or completely responsible for cyber breaches on their products.
It might be easy to assume that in a report split 50/50 between enterprise organizations and OEMs, that this 48% comprises the non-manufacturing organizations. But that’s not the case.
99% of OEM organizations said they are seeking ways to secure their devices, and over 90% of OEMs agreed they should prioritize security above overall functionality or product design. In fact, “lack of budget” ranked as the lowest challenge to securing devices.
OEMs broadly seem to understand that security adds to their value proposition and can ultimately boost their business and set them apart in the market. Just like in the mainstream business world, the OEM world is awakening to the fact that security can serve as an accelerator rather than a cost center with the right investments and strategy.
45% of OEM organizations strongly agreed that IoT security should be considered at the product design stage.
The “shift-left” movement is coming for security, too. Security is becoming so paramount, so relevant to every aspect of product creation, that it simply can’t be relegated to one entity or phase.
It’s possible that regulations will come to reinforce this reality. Digital infrastructure and cyberphysical systems have real-world implications. As governments seek to step up the security of these systems, they advocate for a shared responsibility among product designers, equipment manufacturers, and end users themselves.
OEMs are willing to share this responsibility, with over half agreeing that reporting security risks is a responsibility. If more organizations took this approach, it would allow for better collaboration with operator and user organizations to prevent risks.
A lack of standardization and supply chain complexity make IoT security difficult to achieve
The average OEM uses three methods to secure the connected devices they produce, as noted in Figure 10 in our report.
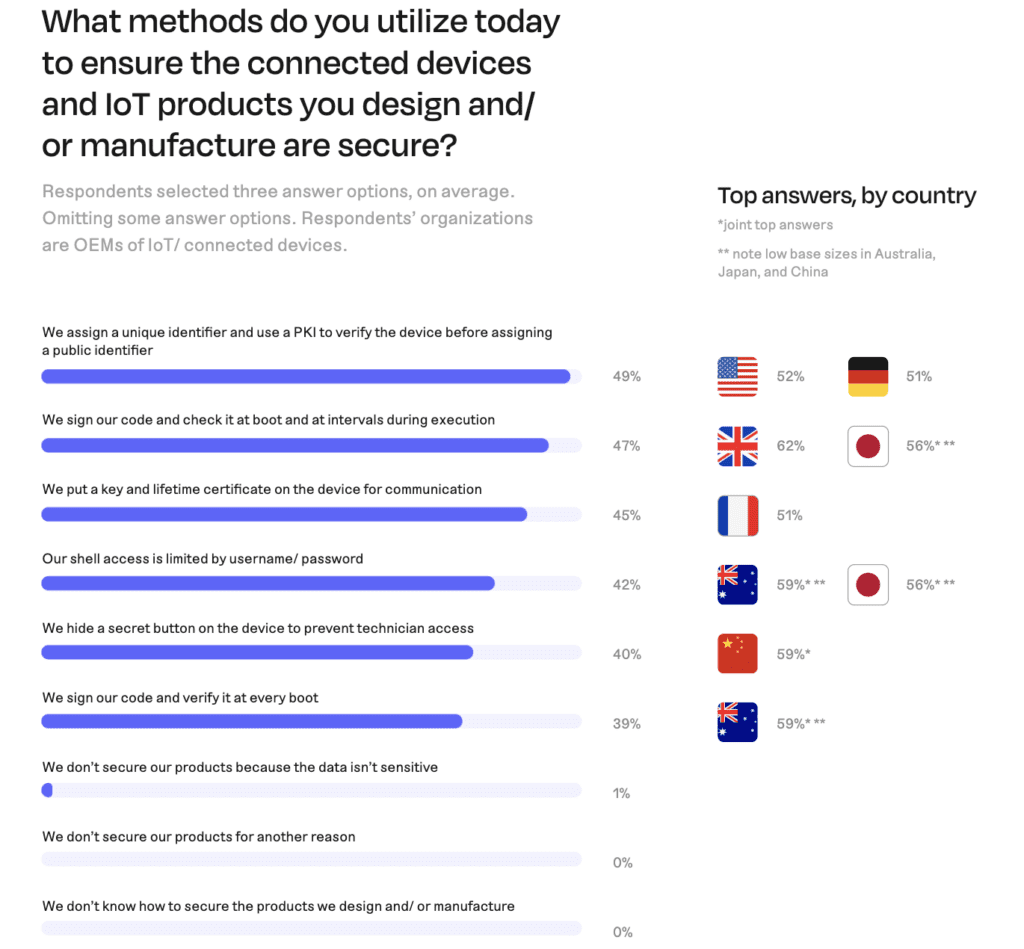
The top three methods were:
- Assigning a unique identifier verified using PKI before assigning a public identifier.
- Signing code and checking it at boot and at intervals during execution.
- Putting a key and lifetime certificate on the device for communication.
However, these methods are hardly ubiquitous. Just like it takes a variety of ways to develop and manufacture products, it also takes a variety of methods to secure them, and no single approach stood out as a defacto or must-do method.
This illustrates how achieving IoT security is anything but straightforward. In the wide range of IoT applications, each comes with its own unique set of requirements and constraints. This elevates the complexity of devising effective security protocols that can be applied universally.
As the landscape evolves, product designers and sellers will likely move toward a more interoperable world, as evidenced by the Matter Standard released earlier this year. However this plays out, it will likely result in a more streamlined approach to securing connected devices across different manufacturers.
The biggest reported supply chain concerns spotlight the need for vendor partnerships

The lifecycle of IoT devices is complex, from design, development, manufacturing, distribution, and continued updates. Each stage represents its own set of vulnerabilities and potential entry points for cyber threats.
The top challenges OEMs face in securing the supply chains are:
- A lack of clarity around best practices for implementing security across global manufacturing lines
- Concern that an outage will result in equipment downtime that impacts production output
- Greater, increased potential for cyber attacks
- The lack of appropriate digital infrastructure
- The lack of skills or talent to manage complex structures
Generally, OEMs feel unprepared to make the changes necessary to enable device security at scale. For many, updating their systems would require a digital transformation so drastic and disruptive that it is a non-starter. Others simply lack the resources and know-how.
Forging partnerships with vendors will be key to achieving and scaling device security.
Certificate-related outages accrue catastrophic costs
Ninety-eight percent of organizations reported at least one certificate outage in the past 12 months.
The total average cost to organizations for certificate outages on their manufacturing lines in the past year came in at an incredible $2.25 M. Costs in APAC ($2.84 M) and in North America ($2.61 M) were even higher.
While only 6% of organizations do not use PKI to manage certificate lifecycles, 27% of organizations manage them with internal solutions. Outsourcing PKI may be an obvious place to start when it comes to trimming the burden of security and maintenance.
Security for the entire life of the product
Managing the lifecycle of cybersecurity components within the product emerged as the biggest responsibility OEM organizations have to their customers. It’s important that organizations understand that their obligation doesn’t end with the sale of the product. Ongoing support and development against the evolving threat landscape is crucial.
But communication will be just as important. Collaboration and a proactive mindset among OEMs, operators, and user organizations, and even end users will be necessary to truly achieve digital trust in tomorrow’s connected world.




