When we discuss digital certificates, most people think about SSL/TLS certificates. While these are the most “popular,” they are not the only ones. There are actually two more types of certificates: code-signing and user/client certificates, which are equally important to securing our online communications.
All three types of digital certificates share a common trait: trust. Let’s get to know them better.
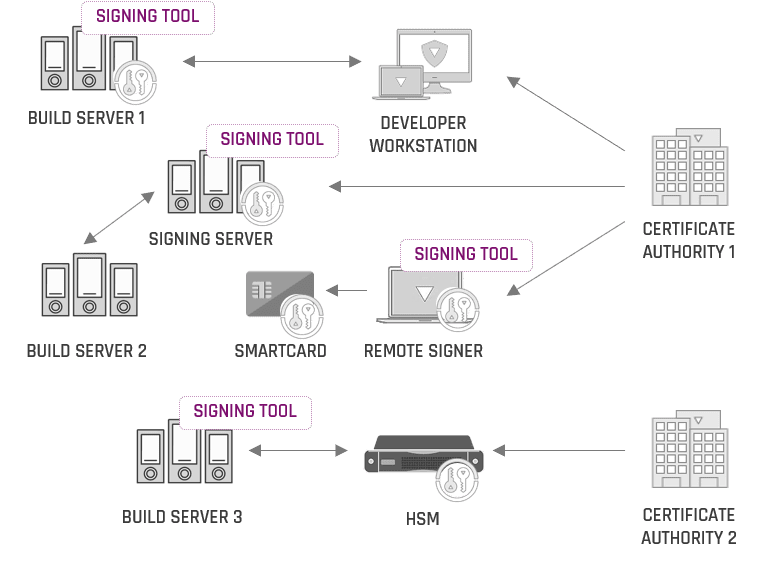
SSL/TLS Certificates
SSL/TLS certificates secure data in transit over the open internet and ensure the site’s trustworthiness. SSL certificates use asymmetric encryption, where a public and a private key are required to secure communications.
Technically speaking, an SSL certificate is a data file hosted on a website’s server. Websites need an SSL certificate to keep user data secure, verify ownership, and prevent attackers from impersonating the site to gain user trust. HTTPS addresses use SSL certificates, where the TCP layer is encrypted by applying the SSL encryption layer.
SSL certificates facilitate the public-private key pairing that is the foundation of SSL/TLS encryption. When a client, usually a browser or a device, attempts to establish a TLS connection with a server, they refer to the SSL certificate to obtain the server’s public key and identity.
Also, SSL certificates verify that a client is talking to the correct server that actually owns the domain. This verification ensures domain validation and prevents domain spoofing, man-in-the-middle attacks, and other malicious actions that target users’ trust.
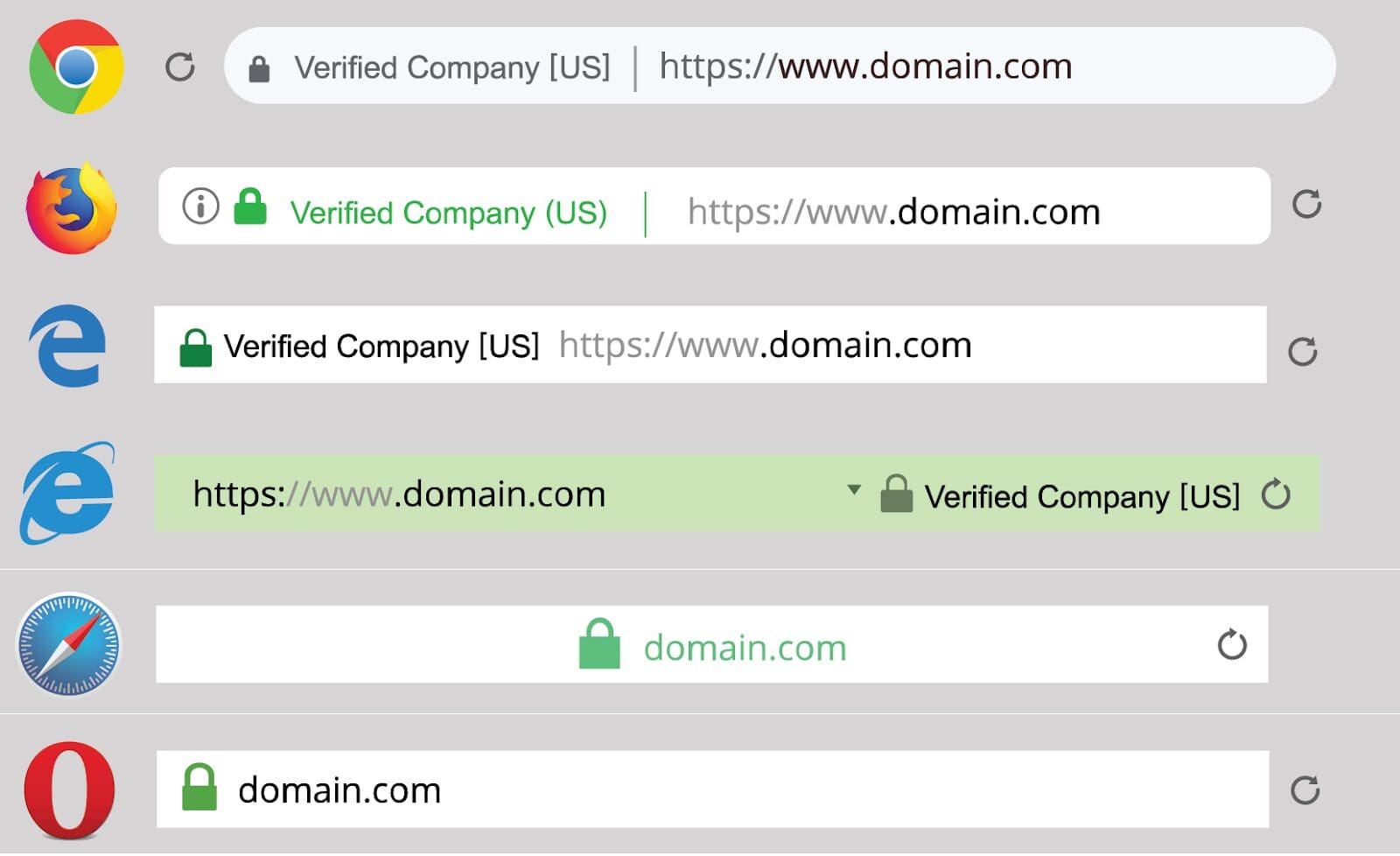
Code-Signing Certificates
Code-signing certificates ensure the authenticity of the code used for developing software applications. Code signing confirms who the software author is and proves that the signed code has not been altered or tampered with after it was signed. With the complexity of modern software supply chains, both functions are essential for building trust and minimizing supply chain attacks.
As with the SSL certificates, code signing is based on the pairing of public and private keys. The developer signs the code with its private key, and the end-user uses the developer’s public key to verify their identity. Code-signing identifies that the software or application is coming from a trusted source, removing any “unknown publisher” warnings.
Additionally, code-signing certificates ensure the integrity of the application and that the code has not been altered. If the application is tampered with or changed after being digitally signed, the signature will appear invalid and untrusted.
When a piece of code is digitally signed, a timestamp is applied. Timestamping ensures that the signed code remains valid even after the digital certificate expires. Unless the developer changes the code, there is no need for them to apply a new digital certificate.
User/Client Certificates
While the SSL certificates validate site domains, user/client certificates authenticate people or devices requesting access to sensitive corporate data or services. User certificates work like passwords, but they remove the friction of remembering lengthy and complicated passwords and are much more secure than passwords.
Client certificates, just like the server SSL certificates, use Public Key Infrastructure (PKI) for authentication. But, unlike server certificates, client certificates are used only to validate the identity of a person or device; client certificates are not used to encrypt data. User/client certificates ensure that only authorized people are accessing services and/or data.
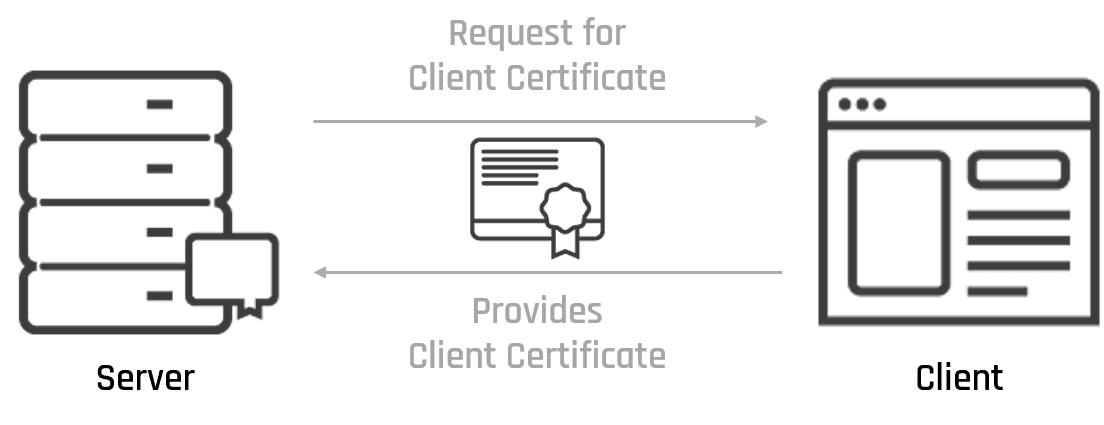
Client certificates are gaining popularity in businesses. Companies are increasingly migrating data and apps to the cloud, and they need to find a way to validate people’s authenticity through remote access.
Traditional authentication mechanisms, like passwords, are no longer adequate. Attackers are keen on stealing or compromising weak passwords. Stolen credentials are the most prevalent attack vector, and passwords are considered a vulnerability rather than an authentication factor.
That is where client certificates come in handy. Instead of validating people via insecure passwords, client certificates authenticate people through the systems they use. Client SSL certificates are installed on the users’ devices, which they use to connect to a given site or service. If the user does not have the required permissions, they will not be granted access.
Client certificates are also used in two-factor authentication (2FA) schemes. They are the “something you have” factor of the process, making connections to sensitive data or services even more secure. While 2FA might not be the panacea to all authentication problems, it presents an additional level of complexity for attackers, who normally seek the easiest way to infiltrate corporate networks.
Besides strengthening the authentication of people, client certificates also enhance user experience. Data security is a balancing act between proper controls and user convenience. As such, client certificates remove any user intervention and eliminate the friction of having to type in passwords.
Considering that user inconvenience is often cited as a barrier to effective security controls, client certificates are a huge plus for establishing a strong security posture. This is especially important in zero trust security schemes, where strong identity authentication is the basis for placing trust to remote users and employees.
Looking Ahead: Managing All Digital Certificates Effectively
Organizations need to establish a robust, centralized, and automated certificate lifecycle management. Poor certificate management policies and practices erode the trust businesses and users place on digital certificates and can result in costly outages or attacks.
Keyfactor’s certificate lifecycle automation and management platform make it simple to manage the lifecycle of keys and digital certificates across your business. You can gain visibility from certificate discovery and monitoring to issuance, renewal, and revocation, keeping digital certificate-related outages and security breaches at bay, without compromise.